- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Convert Local Security Policies to Panorama Policies
- LIVEcommunity
- Tools
- Expedition
- Expedition Discussions
- Convert Local Security Policies to Panorama Policies
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 09:10 AM
We have quite a few Palo Altos that we inherited that have many local policies. We would like to manage these policies via Panorama. Is it possible to convert Local Security Policies to Panorama Policies using Expedition? If so is there a guide on how to do that?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 09:42 AM
"because the device serial #'s stick in the Panorama firewall rules." - in what, the targets of the rules? Yeesh, that sounds like a bad situation.
I think what I would do, honestly, is go get the "set" commands from the local firewalls that consitute their firewall policies, and then do some clever find/replace, and put those rules into Panorama as Pre-Rules via Panorama's CLI. You'd have to do things like set device groups, etc in the text you would paste into Panorama's cli, etc. Without seeing it in total, its hard to say, but on the surface, that sounds like the direction I would go.
Don't get me wrong, there might be a case to use Expedtiion for this, but it sounds to me like something that would be easier to do with a little "manual" effort.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 09:29 AM - edited 08-20-2018 09:29 AM
In such as situation, I would do an import of the local firewall config into Panorama via the function "Import device configuration to Panorama" , which will import the devices config into Panorama as a device group and template. Expedition doesn't really gain you anything that I am aware.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 09:35 AM
Tim Thank you for responding. The firewalls in question are already in Panorama and currently use a combination of Panorama pre/post rules as well as local rules. Are you saying that it is possible to import a firewall configuration into Panorama that is already in Panorama? We tried removing the firewalls from Panorama in order to then import them but ran into a situation where we cannot automatically remove any firewalls from Panorama because the device serial #'s stick in the Panorama firewall rules. We would then have to go to each rule and remove the firewalls serial individually and there are 1000's of rules and close to 50 firewalls.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 09:42 AM
"because the device serial #'s stick in the Panorama firewall rules." - in what, the targets of the rules? Yeesh, that sounds like a bad situation.
I think what I would do, honestly, is go get the "set" commands from the local firewalls that consitute their firewall policies, and then do some clever find/replace, and put those rules into Panorama as Pre-Rules via Panorama's CLI. You'd have to do things like set device groups, etc in the text you would paste into Panorama's cli, etc. Without seeing it in total, its hard to say, but on the surface, that sounds like the direction I would go.
Don't get me wrong, there might be a case to use Expedtiion for this, but it sounds to me like something that would be easier to do with a little "manual" effort.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 12:23 PM
Thank you Tim for your advice. I agree with you that this may be best to attack from the CLI and possibly using the "load config partial" commands. Looking at the policies on one of my 5000 units I see close to 700 local policies and am wondering how the address objects will play a role in the load config partial functionality. I appreciate your help again.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2018 07:16 AM
Hi,
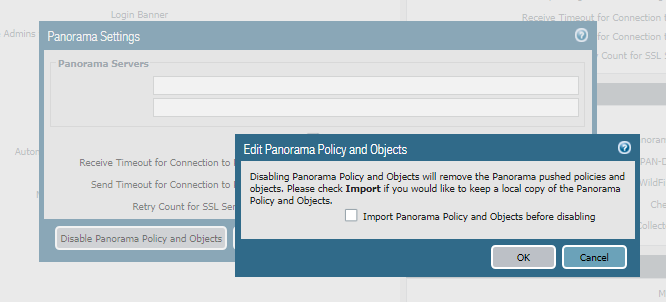
Go to the firewall panorama setting and disable device group and template settings. When you doing that it will popup window to tick import panorama objects and policies. Enable that tick and commit then all the panorama objects and policies will be available on the local firewall. After get a backup from firewall and import it to the panorama and do the force commit ( When importing config to panorama it will create default name for the device group and template you can change it ).
Please see the attached screenshot.
Thanks.
- 1 accepted solution
- 8180 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Merging is not happening when I tried the JUNIPER to PA in Expedition Discussions
- Management Port ASA Migration in Expedition Discussions
- Cisco ASA To Panorama Partial Configuration question in Expedition Discussions
- Security Policies Green Check Mark Spinning? in Expedition Discussions
- Expedition 1.2.85 Hotfix Information in Expedition Release Notes