- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Configure Certificate Based Authentication for IKE: ISSUE Cert
- LIVEcommunity
- Discussions
- General Topics
- Re: Configure Certificate Based Authentication for IKE: ISSUE Cert
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Configure Certificate Based Authentication for IKE: ISSUE Cert
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-24-2014 08:31 PM
Hi all,
I config IPSec betwen two PA device: 1 PA5020 and 1 PA
I config as guide: How to Configure Certificate Based Authentication for IKE on PAN-OS 6.0
I generate CA on PA 5020 and import to PA 200
But on PA 200 i can't sign new Cert with the imported CA certificate.
I try generate all cert on PA 5020 ( root CA & signed CA) and import to PA 200.
But when config IKE gateaway, i can't chose CA
Something wrong, but i don't where
Pls help me
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-24-2014 08:52 PM
Hi dat.tran
Could you please show us the snapshot of the CA imported ?
Also can you try generating the certificate to be used on PA-200 on PA-5020 itself ?
Hope it helps !
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2014 06:16 AM
Hello,
When you exported and imported certificate did you by any chance exported private key also?
Regards,
Hari Yadavalli
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2014 07:12 AM
Hi Dat,
Make sure you have imported private key of the certificate along with certificate. If that is done for sure you sign another certificate.
Export certificate : make sure you click on private key and put passphrase. Exa; Passphrase is "test123"
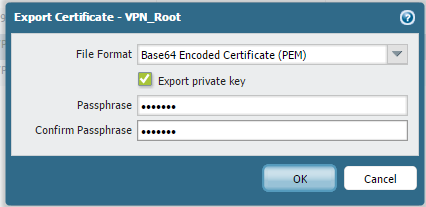
Import Certificate : Make sure you click Import Private key. Put above specified passphrase "test123"
Regards,
Hardik Shah
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-26-2014 08:30 PM
Thanks for support,
now, i can import and used Cert
But, my tunnel IPSEC can't UP
I don't know what wrong.
Thanks.
My config:
PA 5020
PA 200
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-26-2014 08:36 PM
Hello dat.tran,
Could you please apply below mentioned CLI command to initiate the tunnel manually:
> test vpn ike-sa gateway XXXXXX
Initiate IKE SA: Total 1 gateways found. 1 ike sa found.
> test vpn ipsec-sa tunnel XXXXXX
Initiate IPSec SA: Total 1 tunnels found. 1 ipsec sa found.
After applying above CLI commands, i would request you to check MOnitor > Logs > System for more detail information (subtype= "vpn")
Hope this helps.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-26-2014 09:10 PM
Thanks, Time on PA 200 fault ![]()
Now, IPSEC tunnel is UP>
Thanks for your help :smileygrin:
- 5285 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Firewall fails to register to Wildfire appliance in Next-Generation Firewall Discussions
- Should I override the intrazone-default to deny? in Next-Generation Firewall Discussions
- Issue: New Palo Altos crashing domain controller with migrated config in General Topics
- AZURE VM Configure GP with certificate in GlobalProtect Discussions
- GP SAML authentication with multiple client configurations in gatway in GlobalProtect Discussions



