- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Decryption certificate
- LIVEcommunity
- Discussions
- General Topics
- Re: Decryption certificate
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Decryption certificate
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-25-2014 07:58 AM
Hi,
I have a PA500 (OS 5.0.11)
I already configured it for SSL Decryption with a self signed certificate.
I need to use a Digicert Certificate. I already have a wildcard certificate with Digicert.
Question is: can I use my wildcard certificate for SSL Decryption?
How?
I try to import my certificate but I cannot use it for SSL Decryption
Thanks
Regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-25-2014 08:03 AM
Hi !
For SSL decryption you'll need a CA certificate as it will be posing as the signing certificate of the websites the users are accessing.
A document that may come in handy
How to Implement SSL Decryption
regards
Tom
PANgurus - Strata specialist; config reviews, policy optimization
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-25-2014 08:26 AM
Thanks but in case of a Certification Authority like Verisign or Digicert I need to request a new certificate (signed by them) or I need to import a root certificate?
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-25-2014 08:31 AM
In case of CA like verisign or digicert, you need to import chained certificate signed by the Public CA
This document is very helpful:
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-26-2014 03:26 AM
I follow this guide and I create a pkcs12 chained certificate with this command:
openssl pkcs12 -export -in [certificate.pem] -inkey [certificate.key] -CAfile [chain.cer] -caname digicert -out [server-chain.p12] -name digicert -chain
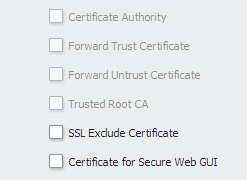
but when I import my certificate (IMPORTANT: it is a web server certificate) it is not recognized as a CA.
I think problem is that my certificate was request for a web server.
If I try to install DigiCert CA root certificate it is recognized as a CA but I cannot use it for decryption.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-26-2014 09:44 AM
You cannot use a certificate from a public CA like VeriSign or Digicert. A public CA will never give a subordinate (intermediate) CA certificate to someone outside their trust. With a subordinate certificate, you can create new certs that are trusted to the root, even for existing and common sites.
For SSL decryption, you need to use an internal CA certificate or generate a self-signed certificate on the firewall and use that. In both instances, you will need to distribute the public key of that certificate to all clients you wish to be decrypted.
Hope this helps,
Greg
- 4343 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Can't install device certificate in General Topics
- Setup > Management > Cortex Data Lake > Cortex Data Lake Status > Show Status in AIOps for NGFW Discussions
- Can't import a certificate via XML API using C# in General Topics
- Potentially Dangerous Tool Alert in Cortex XDR Discussions
- Device Certificate for managed device in Panorama Discussions



