- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How do I identify which PC made a suspicious DNS query?
- LIVEcommunity
- Discussions
- General Topics
- How do I identify which PC made a suspicious DNS query?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2016 08:18 AM
Hello
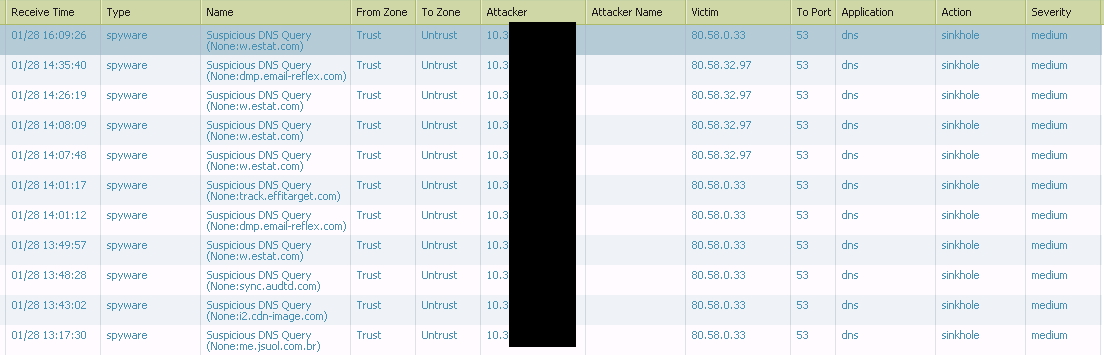
I have setup the Anti-Spyware Profile in our firewall and I have a lot of threat logs of type spyware suspicious DNS queries from a domain controller machine and this is cleansed.
Monitor > Logs > Threat list
As you can see I have configured the sinkhole method. But I woluld like to know how could I identify which PC are making this suspicious DNS queries?
Thks
Diego
- Labels:
-
Configuration
-
Logs
-
Threat
-
WildFire
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2016 09:21 AM
You have to look for traffic towards the sinkhole IP in your traffic log, if it's configured as an IP outside the PC LAN.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2016 06:26 PM
@SOC_CSG You can create filter the traffic log for the DNS queries directed towards the Sinkhole address. You may create a report using traffic logs as well :
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2016 07:19 PM
HI ,
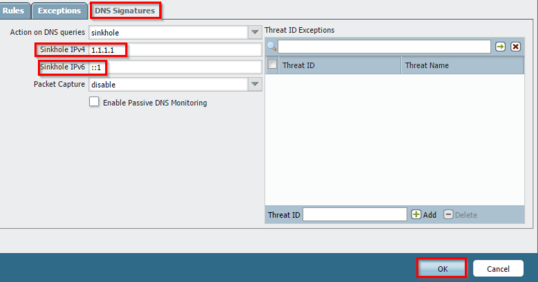
I think that you should configure fake ip address on sinkhole ipv4 field. That fake ip addressin not used inside of the network.
Then you need to have security rule that block all access to fake ip address .
Maybe it's helpful
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2016 09:21 AM
You have to look for traffic towards the sinkhole IP in your traffic log, if it's configured as an IP outside the PC LAN.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2016 06:26 PM
@SOC_CSG You can create filter the traffic log for the DNS queries directed towards the Sinkhole address. You may create a report using traffic logs as well :
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2016 07:19 PM
HI ,
I think that you should configure fake ip address on sinkhole ipv4 field. That fake ip addressin not used inside of the network.
Then you need to have security rule that block all access to fake ip address .
Maybe it's helpful
- 3 accepted solutions
- 6342 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- XSOAR Playbook SQL Query in Cortex XSOAR Discussions
- Generate traffic report to identify any suspicious traffic in General Topics
- Filtering panorama policies by modified date. in Panorama Discussions
- XQl query to identify software installation attempt and/or launching a software in MacOS in Cortex XDR Discussions
- RQL Query to search for suspicious activity on specific S3 Bucket in Prisma Cloud Discussions