- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
IPSEC VPN support for both side as Dynamic, Supported on Juniper but not on PA
- LIVEcommunity
- Discussions
- General Topics
- IPSEC VPN support for both side as Dynamic, Supported on Juniper but not on PA
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
IPSEC VPN support for both side as Dynamic, Supported on Juniper but not on PA
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2016 01:40 AM - edited 12-04-2016 01:46 AM
Hi There,
I was migrating configuration from Juniper to PA, everything worked as expected except IPSEC VPN.
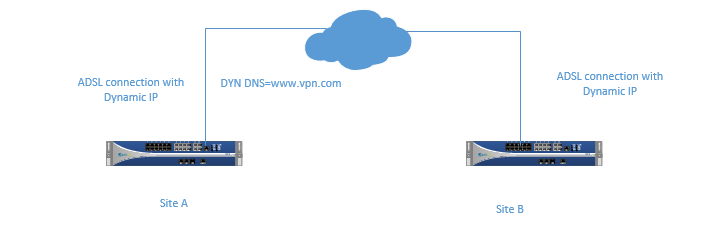
Customer has two sites and both sites have ADSL connection with Dynamic IP address, however on one end Dyn DNS is used. In the below example Site-A has Dyn DNS and www.vpn.com gets updated as soon as IP gets changed on Site-A. But on PA there is no option to configure FQDN for static peer only IP address. However on Juniper you can select peer as Static and you can configured IP/FQDN, even though peer is dynamic you can select it as static and configure the FQDN "www.vpn.com" and Site-B fires IPSEC VPN traffic and works like a charm.
Below is the example, where you can configure FQDN on Juniper, I was wondering that does PA has any plan to allow both IP and FQDN if you select peer type as Static like Juniper.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2016 10:10 PM
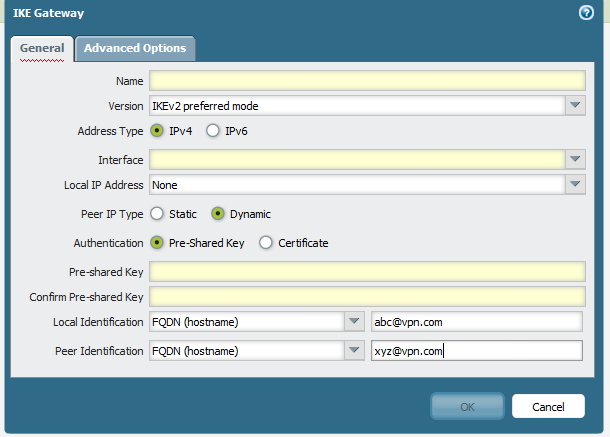
IN Palto firewall if you are using dynamic ip .. please select as below.. the you can established site to site vpn
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2016 11:11 PM
That could work. But you need to make sure the other side uses FQDN for phase 1 identification. From that Juniper screenshot FQDN is used only for getting the IP for transport while peer ID is left empty.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 12:11 AM - edited 12-05-2016 02:03 AM
Hi,
Agreed with the comments above. Make sure PA can resolve FQDN of the peer (bi-directional). DDNS has to be configured for the both peers
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 07:29 AM
Hi,
I configured peer identification as FQDN, but PA does not fire IPSEC VPN. Enabled debug for ikemgr.log and could see that "can't initiate IPSEC VPN for Dynamic peer".
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 07:45 AM - edited 12-05-2016 08:08 AM
Hi,
Post the IKE Gateway config and logs from the both devices if possible.
Can you resolve the FQDN for the remote peer? Can peer resolve yours? Can you reach the peer with simple ping? How about your security policies. Do you have IPSEC traffic permitted on the untrust interface (same zone traffic untrust>untrust)? (you can enable management profile for outside interface for the test)
Thx,
Myky
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 08:07 AM
You likely have a configuration error on the IKE gateway, I assume that the security policy to allow the traffic has already been generated on both devices. To clarify this connection is between two Palo Alto devices right, it isn't a Palo Alto to something else?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 08:20 AM
Hi,
Yes I can resolve the FQDN of peer. I can reach to peer (ping source X.X.X.X host www.xyz.com).
I don't see any traffic reaching on remote peer.
A security policy has been configured on both end to allow IPSEC traffic.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 08:28 AM
Hi,
What is on the remote side (device)? Logs will help. Also, who is an initiator of the tunnel? Best to check responder side logs.
Can you provide the logs?
Thx,
Myky
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 08:30 AM
Hi All,
Got the confirmation from PA TAC that tunnel can't be stablished if both peer is DYNAMIC, one end has to be static.
But it is supported on Juniper, henec I will raise a feature request for this.
Thank you for your help.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 08:32 AM
Hi,
Very good info)) I always thought you can with PA. Theoretically should work
Thx,
Myky
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 10:10 AM
Same, I guess I never had a need for both ends to be dynamic.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 10:58 AM
Yes, I concur with you. I had an impression that if FQDN gets resolved to an IP, it should work.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2016 11:16 PM
FQDN in this case is just an ID for phase 1. If peer is set as dynamic, PA can't know to which IP address to send the packet to. I assumed you have static IP on PA and the other gateway could be initiator. And yeah, if both gatways have dynamic IP nobody can know to what IP to send packets to start negotiation.
In Juniper case i guess FQDN was just a mechanism to feed IP to FW and IPSEC was basically set as static to static. Which I agree is a good feature to have.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-06-2016 08:54 AM
Yep this is what l thought so that PA resolve a DNS>IP before initiate a tunnel P1
- 6702 Views
- 17 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Dynamic DNS Registration Support for Mobile Users—GlobalProtect in GlobalProtect Discussions
- Policy Based VPN in Next-Generation Firewall Discussions
- Zero trust in AWS issue with ALB in VM-Series in the Public Cloud
- PAN OS 8.1 support after March 1st 2022 in General Topics
- User's in session table hitting wrong NAT rule in General Topics