- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
NAT translation help
- LIVEcommunity
- Discussions
- General Topics
- Re: NAT translation help
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
NAT translation help
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-15-2019 09:30 AM
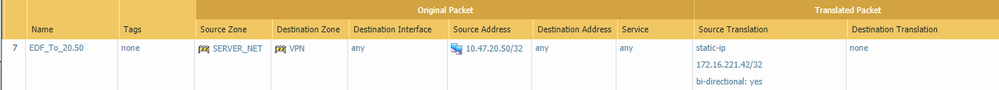
For the life of me I can't figure out something that should be simple. I'm having a problem with a nat translation setup. Here is the requirement:
I have various computers/devices on several IP addresses and different subinterfaces, for example:
Device 1:
IP address: 10.47.5.21
Subinterface: Ethernet1/1.5
Zone: Control_NET
Device 2:
IP address: 10.47.20.50
Subinterface: Ethernet1/1.20
Zone: Server_NET
I need to NAT these devices to another range, in this example, to 172.221.16.32/28 range. So it should go like this:
10.47.5.21 <-> 172.221.16.32
10.47.20.50 <-> 172.221.16.42
...
The reason for this is I have a customer that has a site-to-site VPN connection and will only be looking at the 172.221.16.32/28 range. What sort of NAT translation do I need to do? I've tried the following and it's not working:
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-15-2019 10:03 AM
Hello,
Do you have corresponding security policies to allow the traffic? The logs should show if/why the traffic is getting blocked. This is just the NAT part of it. Also check routing?
Just some thoughts.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-15-2019 10:22 AM
I believe so. I have an allow policy with Control_Net and Server_Net as the source zone and the VPN as the destination zone, and a corrisponding allow policy with the VPN as the source zone and Control_Net and Server_Net as the destination zone. I'm not sure if this is the right way as the Control_Net zone is for the 10.47.5.0/24 addresses and the Server_Net zone is for 10.47.20.0/24 addresses. Where do I place a security policy that allows traffic to/from the NAT range of 172.16.221.32/28? Do I need to devine a zone for the NAT range, and if so, how do I go about it?
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-15-2019 12:00 PM - edited 02-15-2019 12:04 PM
| ip nat inside source static 10.47.5.22 172.16.221.33 route-map 2EDF |
| ip nat inside source static 10.47.5.21 172.16.221.34 route-map 2EDF |
| ip nat inside source static 10.47.28.100 172.16.221.35 route-map 2EDF |
| ip nat inside source static 10.47.20.22 172.16.221.36 route-map 2EDF |
| ip nat inside source static 10.47.20.5 172.16.221.37 route-map 2EDF |
| ip nat inside source static 10.47.20.11 172.16.221.38 route-map 2EDF |
| ip nat inside source static 10.47.20.12 172.16.221.39 route-map 2EDF |
| ip nat inside source static 10.47.20.26 172.16.221.40 route-map 2EDF |
| ip nat inside source static 10.47.20.27 172.16.221.41 route-map 2EDF |
| ip nat inside source static 10.47.20.50 172.16.221.42 route-map 2EDF |
| ip nat inside source static 10.47.20.51 172.16.221.43 route-map 2EDF |
! access-list 101 permit ip 172.16.221.32 0.0.0.15 172.16.200.0 0.0.0.255 |
| access-list 101 permit ip 172.16.221.32 0.0.0.15 172.16.202.0 0.0.0.255 |
| access-list 101 permit ip 172.16.221.32 0.0.0.15 172.16.207.0 0.0.0.255 |
| access-list 101 permit ip 172.16.221.32 0.0.0.15 172.16.208.0 0.0.0.255 |
| access-list 105 permit ip 10.0.0.0 0.255.255.255 172.16.0.0 0.0.255.255 |
| route-map 2EDF permit 10 |
| match ip address 105 |
- 2089 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- NAT mapping public to private IP in General Topics
- Panorama and Firewall Communication in Panorama Discussions
- Trouble routing from Guest zone to Internal Server in General Topics
- Demystifying NAT Traversal with VPN IPsec in Next-Generation Firewall Discussions
- Full Cone NAT, Restricted Cone NAT and Symmetric RFC NAT Terminologies versus Vendor NAT Terminologies. in Next-Generation Firewall Discussions