- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Questioning about unsupported cipher suite for SSL Decryption
- LIVEcommunity
- Discussions
- General Topics
- Questioning about unsupported cipher suite for SSL Decryption
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-03-2014 05:37 PM
Hello guys.
I have installed SSL decryption policy, which is forward proxy, for particular users. It's working fine but some problem occurred. Korean messenger application called kakao-talk for PC is not being able to login during forward-proxy SSL decryption policy applied. So I tried to capture the PCAPs for kakao-talk login function and they were using that TLS version 1.1 and Ciper Suite : TLS_RSA_WITH_AES_256_CBC_SHA (0x0035).
I could not find that any document for unsupported cipher suite for forward proxy (outbound SSL decryption). My question is PAN could not support cipher suite, TLS_RSA_WITH_AES_256_CBC_SHA? How do I bypass for the unsupported cipher suite for outbound SSL decryption? I tried to create a decryption profile that not to enable any block policy but it could not be bypassed and kakao-talk was not able to login.
Please let me know what is unsupported cipher suite for outbound SSL decryption and how can I bypass for unsupported outbound SSL decryption traffic.
Thanks in advance.
Regards,
Roh
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-03-2014 06:40 PM
Hello Roh,
First of all, we can't decrypt where diffie hellman is used in the key establishment. SSL traffic will be encrypted, so we can not see the original URL on the URL logs. URL logs will give us the certificate name. If you have that Destination IP address, you can create a No-Decryption policy for that specific destination ( top of the policy table).
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-03-2014 05:51 PM
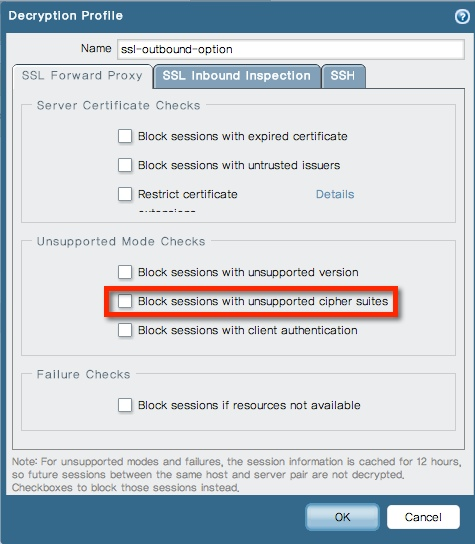
Do you have decryption profile assigned to the decryption policy ( Options Tab in the policy ) . If so, can you verify if the "Block sessions with unsupported cipher suites" is selected and disable it and try again ? You can define what should be blocked or not blocked for the Unsupported Modes in the decryption profile
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-03-2014 06:06 PM
Hello knarra,
Thanks for interesting my question.
Yes, The decryption profile assigned to the decryption policy and I disabled the option "Block sessions with unsupported cipher suites" but it's not working to login for kakao-talk application.
Thanks again.
Regards,
Roh
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-03-2014 06:10 PM
Hello Sir,
For SSL decryption, we only support SSLv3, TLSv1.0, and TLSv1.1 (TLSv1.2 will be downgraded in forward-proxy mode as of 4.1.9 and 5.0.0)
Supported cipher suits:
RSA-AES256-CBC-SHA
RSA-AES128-CBC-SHA
RSA-3DES-EDE-CBC-SHA
RSA-RC4-128-MD5
RSA-RC4-128-SHA
Hope this helps.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-03-2014 06:16 PM
Hello HULK,
Thanks for giving information ![]() . It's a strongly needed information.
. It's a strongly needed information.
But I have question remaining is how do I bypass the unsupported SSL traffic such as a SSL with using unsupported cipher-suite.
Should I not assign the SSL decryption profile that makes bypass the unsupported SSL traffic? or how?
I tried to find that URL for SSL handshaking but could not find. I believe that Ciper Suite : TLS_RSA_WITH_AES_256_CBC_SHA makes hiding URL for SSL handshaking, right? I am not sure.
If I found that URL for SSL handshaking and recognizing URLs of SSL by PAN, I could make a no-decrypt rule but now I cannot do.
Thanks.
Regards,
Roh
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-03-2014 06:40 PM
Hello Roh,
First of all, we can't decrypt where diffie hellman is used in the key establishment. SSL traffic will be encrypted, so we can not see the original URL on the URL logs. URL logs will give us the certificate name. If you have that Destination IP address, you can create a No-Decryption policy for that specific destination ( top of the policy table).
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-03-2014 07:27 PM
Hello HULK,
Thanks for giving a information. Finally I created a no-decrypted rule with destination address and it's working fine.
Have a nice day.
Regards,
Roh
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2021 11:25 PM
Hi,
I have recently found this topic, but I have the same problem. We have PAN OS 9.1.7 which already have predefine ssl decryption exclude list contain *.kakao.com, even I have added more kakao.com domain into the exclude list or add the url category or destination with kakao IP address in the no decryption policy, while other traffic like web-browsing and ssl will decrypt. It is still failed to login Kakao talk when ssl decryption in place.
The only way to make Kakao talk work is to NOT decrypt everything, with the no decrypt rule place at first in the decryption policy pool.
Would anyone please help to suggest, my aim is to make the Kakao talk works and we can still decrypt normal http/https traffic.
Thank you
- 1 accepted solution
- 8163 Views
- 7 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Questions about the decryption performance of pa-5200 series in Next-Generation Firewall Discussions
- Question regarding random Decryption when using Cortex XDR in Cortex XDR Discussions
- decrypt-unsupport-param error with no decryption in General Topics
- Unsupported cipher. Supported client cipher bitmask: 0x00000000 in General Topics
- decrypt-error/decrypt-unsupport-param inbound ssl in General Topics



