- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
security policy between layer 2 zones
- LIVEcommunity
- Discussions
- General Topics
- security policy between layer 2 zones
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-10-2019 07:21 AM
Hi, I am new to Palo Alto, so this might be a dumb question, below is the setup I have been trying to get it to work -
- two layer2 zones; Zone1 and Zone2
- three PCs, PC1; PC2 and PC3
- PC1 in Zone1
- PC2 and PC3 are in Zone2
- all three PCs are on the same subnet
question: I am trying to create a security policy to only allow PC1 to talk to PC2, and deny everything else
is it doable?
Thanks
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-12-2019 01:19 PM
Hello.
Making progress though right? 😛 Not really.
I think I realized that I isolated you now, with vlan10 and vlan20 not being able forward arp/broadcast traffic.
So... back to original idea of 2 ports in a single L2 vlan on the FW.
So if PC1 is on port1 and PC2 is on port2 (both ports in same vlan on FW) then the following should happen.
PC1 attempts to ping PC2.
Not knowing his L2 mac address, he will arp out (broadcast)
Traffic ingress switch, egresses out the trunk port.
Aggregation switch should fwd (untagged tag) packet to port1 of FW.
FW will/should allow broadcast to go out port2 and reverse down trunk to PC2.
Once arp resolution is determined, then security policy should be something like like
SZ (fw_vlan) SA (PC1) ==> to DZ (fw_vlan) DA (PC2) ==> app of ping ==> application-default a ==> ALLOW
next rule is
SZ (fw_vlan) SA (PC1) ==> to DZ (fw_vlan) DA (ANY) ==> ANY ==> ANY ==> DENY
If you missed this rule, then the intrazone rule is what you hit and allowed you to ping PC3
This may be exactly what you had (and I would apologize for going down a rabbit hole... 😛
You would need to look at your traffic log to see/confirm that the traffic from PC1 is hitting PC2 and also confirm.if traffic is passing and then denying for PC1 to PC3 traffic.
Let us know.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-10-2019 08:23 AM
Not a dumb question at all... let's review some info, and set expectations.
PC1 is in Zone1.
PC2 is in Zone2
You did not mention at what layer (VWire, Layer2, or Layer3 interface) you are doing your routing (if any)
If all PCs are plugged into a switch (downstream from FW), then the switch will intercept the arps and the FW will not be an inspection point.
You can plug PC1 physically into a port assigned to Zone1 (and do the same for PC2, assigned to Zone2) and now, the firewall would inspect traffic between both PCs.
Ideally... PC1 in Zone1, should be a different subnet than PC2/PC3, so that the FW is the default gateway (at L3) to route and inspect/allow traffic to PC2 and deny traffic to PC3.
To summarize, the FW must see the traffic ingressing to the Zone1.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2019 12:48 AM
Hi Steve, thanks for you reply, we cant change the IP addresses of the devices hence we have to use layer2 ...
There are two Cisco switches:
Switch 1, where all PCs are connected to, two VLANs created on this switch: -
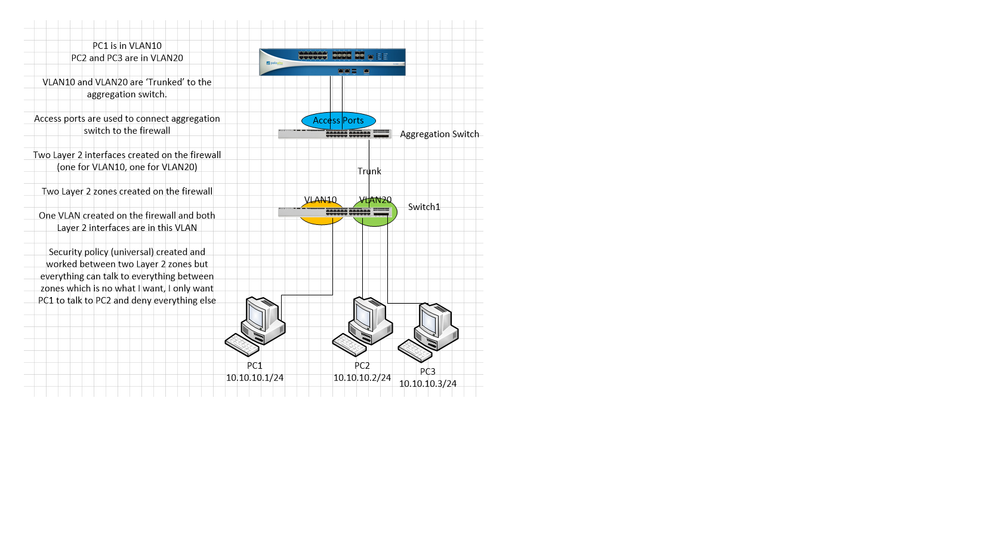
PC1 is in VLAN10
PC2 and PC3 are in VLAN20
Aggregation Switch
VLAN10 and VLAN20 are ‘Trunked’ to the aggregation switch.
Access ports are used to connect aggregation switch to the firewall
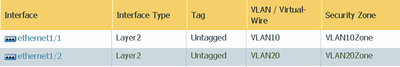
Two Layer 2 interfaces created on the firewall (one for VLAN10, one for VLAN20)
Two Layer 2 zones created on the firewall
One VLAN created on the firewall and both Layer 2 interfaces are in this VLAN
Security policy (universal) created and worked between two Layer 2 zones but everything can talk to everything between zones which is no what I want, I only want PC1 to talk to PC2 and deny everything else
i
Please find attach image for reference.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2019 10:53 AM
Hello
Your issue is that you created a single vlan on the FW, and associated both interfaces to that vlan.
The put the zones into the same vlan.
You should create 2 vlans on the FW and put vlan10 in PC1 zone, and vlan20 onto PC2
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-12-2019 12:17 AM
Hi Steve, I have created two VLANs and a layer 2 security policy on the firewall, now they cant ping each other ...
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-12-2019 01:19 PM
Hello.
Making progress though right? 😛 Not really.
I think I realized that I isolated you now, with vlan10 and vlan20 not being able forward arp/broadcast traffic.
So... back to original idea of 2 ports in a single L2 vlan on the FW.
So if PC1 is on port1 and PC2 is on port2 (both ports in same vlan on FW) then the following should happen.
PC1 attempts to ping PC2.
Not knowing his L2 mac address, he will arp out (broadcast)
Traffic ingress switch, egresses out the trunk port.
Aggregation switch should fwd (untagged tag) packet to port1 of FW.
FW will/should allow broadcast to go out port2 and reverse down trunk to PC2.
Once arp resolution is determined, then security policy should be something like like
SZ (fw_vlan) SA (PC1) ==> to DZ (fw_vlan) DA (PC2) ==> app of ping ==> application-default a ==> ALLOW
next rule is
SZ (fw_vlan) SA (PC1) ==> to DZ (fw_vlan) DA (ANY) ==> ANY ==> ANY ==> DENY
If you missed this rule, then the intrazone rule is what you hit and allowed you to ping PC3
This may be exactly what you had (and I would apologize for going down a rabbit hole... 😛
You would need to look at your traffic log to see/confirm that the traffic from PC1 is hitting PC2 and also confirm.if traffic is passing and then denying for PC1 to PC3 traffic.
Let us know.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-13-2019 12:55 AM
Thanks again for you reply Steve, that makes lot of sense.
with your help, i have managed to get it sorted, i created the rules as you suggested and also created three 'objects', however i messed up with the mask when creating the network object (instead of 10.10.10.1/32 I put it down as 10.10.10.1/24 (whole subnet...), school boy error I know)
Thanks
- 1 accepted solution
- 5611 Views
- 6 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Policy Recommendations on Panorama for NGFW in different CSP in Next-Generation CASB Discussions
- IOT security is identifying devices in a wrong way in IoT Security Discussions
- Failed to install licenses. Web proxy license is not supported for this platform. in Next-Generation Firewall Discussions
- SSL Inspection issues with GlobalProtect users in General Topics
- FW Outbound policy in Next-Generation Firewall Discussions