DNS Queries Are Not Redirected by PBF Rule if DNS-Proxy is Used
Resolution
Overview
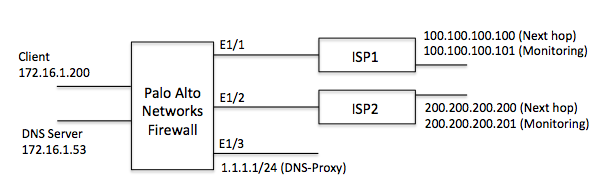
Referring to the sample diagram below. DNS-Proxy is configured on the Palo Alto Networks firewall and PBF rule is applied. The PBF rule is configured so that traffic is redirected to Internet #2 if Internet#1 is down.
Issue
If Internet #1 goes down in this scenario, DNS queries will still go through Internet #1 even though the PBF rule is redirecting traffic to Internet #2.
test@PA-500> show pbf rule all
Rule ID Rule State Action EgreIF NextHop NextHop Status
PBF-rule1-Int#1 1 Disabled Forward eth1/1 100.100.100.100 DOWN
PBF-rule2-int#2 3 Active Forward eth1/2 200.200.200.200 UP
Except from the pan_packet_diag.log file:
== Nov 13 14:08:55 ==
Packet received at slowpath stage
Packet info: len 83 port 23 interface 23 vsys 1
wqe index 229369 packet 0x0x8000000416ff60c6
Packet decoded dump:
L2: 00:1b:17:05:69:17->00:70:76:69:66:00, type 0x0800
IP: 1.1.1.1->8.8.8.8, protocol 17
version 4, ihl 5, tos 0x00, len 69,
id 0, frag_off 0x4000, ttl 64, checksum 48276
UDP: sport 52062, dport 53, len 49, checksum 55414
Session setup: vsys 1
Nov 13 14:08:55 pan_appid_simple_cache_find(pan_appid_cache.c:318): [CACHE] notfound daddr 0-ffff08080808(53, 17)
Nov 13 14:08:55 pan_appid_cache_find(pan_appid_cache.c:475): [CACHE] not foundappid 0-ffff0a006404(52062) -> 0-ffff08080808(52062)
Session setup: ingress interface ethernet1/3 egress interface ethernet1/1 (zone3)
Nov 13 14:08:55 pan_policy_lookup(pan_policy.c:1169): Time required: 9677 ticks
NAT policy lookup, matched rule index 0
Nov 13 14:08:55 pan_policy_lookup(pan_policy.c:1169): Time required: 5789 ticks
Policy lookup, matched rule index 0
DP0 is selected to process this session.
Allocated new session 80.
Packet matched vsys 1 NAT rule 'PBF-rule1-Int#1 (index 1), <--- DNS query from DNS-Proxy still go through downed "PBF-rule1-Int#1" PBF rule.
source translation 1.1.1.1/52062 => xx.xx.xx.xx/38456
Created session, enqueue to install
Resolution
The Palo Alto Networks firewall considers DNS proxy traffic as host traffic, and all host traffic always bypasses PBF rules.
Possible solutions are:
- Avoid using DNS proxy and PBF rules at same time.
- Route DNS proxy traffic to an internal DNS (for example, 172.16.1.53 in the above network diagram) first. Then let it pass through firewall again as "through traffic" so that the PBF rules apply.
owner: kkondo