- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to Generate New MineMeld HTTPS Cert
- LIVEcommunity
- Articles
- General Articles
- How to Generate New MineMeld HTTPS Cert
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 08-17-2016 11:59 AM - edited on 01-26-2021 01:15 PM by jdelio
If you are using your Palo Alto Networks firewall as a trusted root CA, you can generate a web server certificate for MineMeld to replace the self-signed one.
Start Inside WebGUI
Steps:
- Go to your Palo Alto Network Firewall or Panorama WebGUI
- Device > Certificate Management > Certificate
- At the bottom of the screen, click Generate, to create a new certificate. Ensure that it is signed by the firewall by clicking "Certificate Authority".
- Export the pem file with the private key by clicking the certificate you want to export and clicking Export at the bottom of the screen. Then use "Base64 Encoded Certificate (PEM)" and also select "Export private key" and click OK.
Now to the CLI
Steps:
- Now copy the cert to minemeld with the command:
> scp cert_minemeld.pem ubuntu@<minemeldIP>
- Now, log into MineMeld via ssh with the command:
ssh ubuntu@<minemeldIP>
- Now backup the current certificates in case you need to revert back to them if something goes wrong
[minemeld ~]$ sudo mv /etc/nginx/minemeld.cer /etc/nginx/minemeld.cer-orig
[minemeld ~]$ sudo mv /etc/nginx/minemeld.pem /etc/nginx/minemeld.pem-orig - The pem file that you generated will have both the private and public key so you need to split the two. This is how I did it, you may have a better way. The file is readable so you can copy and paste the sections into two different files or use the CLI commands:
NOTE: Please note that there might be a error with sudoing the refers to missing entries in the /etc/hosts file, as the hostname is not automatically added to this file
[minemeld ~]$ cat cert_minemeld.pem | awk 'split_after==1{n++;split_after=0} /-----END CERTIFICATE-----/
{split_after=1} {print > "minemeld" n ".cer"}' [minemeld ~]$ sudo cp minemeld.cer /etc/nginx/minemeld.cer
[minemeld ~]$ sudo openssl rsa -in minemeld1.cer -out -out /etc/nginx/minemeld.pem
[minemeld ~]$ sudo service nginx restart - Now restart the browser session and you should not receive an untrusted error, if the root CA that signed the certificate is installed correctly on your machine.
Some of you might have a Lab-In-A-Box environment and/or want to use the local windows server for certificate maintenance like I do. Nearly all of my certs are certified by the windows domain CA, even if I have a registration authority (RA) on my PAN firewall - I only use it for local services like GP and others.
While I want (and with Rome [8.0] I have) to use a trusted certificate with the nginx webserver (on the minemeld box), I want additional DNS entries and an IP address in the subject - for convenience and to fulfill some dependencies of Rome. Think about CNAME and "domain search". Don't you want to use "https://minemeld" instead of "https://minemeld.servers.yourdomain.local" and have a valid connection with a valid certificate?
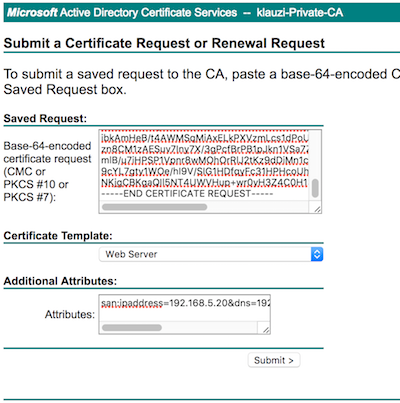
I use to answer cert-requests via the web-GUI on my AD server (https://my-server.mydomain.local/certsrv). But setting up the server is a completely other beast!
Your Windows CA server (2012 in my case) has to support alternative DNS-entries. Prepare your Windows Authority to support certificates with alternative names:
certutil -setreg policy\EditFlags +EDITF_ATTRIBUTESUBJECTALTNAME2
$ su -Create a private key:
or $ sudo bash
# openssl genrsa -aes256 -out minemeld.key 2048 - Enter your passphraseCreate a CSR (certificate signing request) - of course you will replace the values with your own:
# openssl req -new -key minemeld.key -sha256 -nodes -subj '/C=DE/ST=NRW/L=Duesseldorf/O=Klauzi Private/OU=Admin Team/CN=minemeld.servers.klauzi.local/emailAddress=admin@klauzi.local' > minemeld.csr - Enter your pass phrase for the private key (minemeld.key) # cat minemeld.csr -----BEGIN CERTIFICATE REQUEST----- MIIC6zCCAdMCAQAwgaUxCzAJBgNVBAYTAkRFMQwwCgYDVQQIDANOUlcxEDAOBgNV BAcMB0hvZXh0ZXIxFjAUBgNVBAoMDUtsYXVzIFByaXZhdGUxEzARBgNVBAsMCkFk bWluIFRlYW0xJjAkBgNVBAMMHW1pbmVtZWxkLnNlcnZlcnMua2xhdXppLmxvY2Fs MSEwHwYJKoZIhvcNAQkBFhJhZG1pbkBrbGF1emkubG9jYWwwggEiMA0GCSqGSIb3 DQEBAQUAA4IBDwAwggEKAoIBAQCsY+cka1aODaNJIZ9ft4DcGUZCQXQjXdG9U+C2 pisXaXHdYHkdpmOSWqWmxIAlIIDjVITjvnviO/g7yEIaY6HR4EBdFKcZU7Tqh0Ze ojFoCiZVy+MQiXFfxhM1GhIeN4mIm1CxNig5aKkj5uitmyqtb/bMK1QDCxA5kUUG /PLV1okaMCB8hboV4q/4UrjO99OkFEdWGn7z1p+GJ5G7Tkpp2ml4Rw6ltT4iCmrZ 0nLFz7fGaFNz8fCZ4/NMVkiJxqaJfjrBtHnnpBXXpx5BYhBXOgUOGzIh/D9Dpfol BW1I3yfNuN1vwnSq+AfFgixf2mYdzTUHsCtMk++9v3kUKeCzAgMBAAGgADANBgkq hkiG9w0BAQsFAAOCAQEAZWkORNHiNu7rkQ/tJ6yvbsZ5f6lom360KuT1IgZoKgcq ibkumHeB/t4AWMSqMiAxELkPXVzmLcs1dPoUQp72iacCCRoE8Ch/XjXXF0bOM0Pg zn8CM1zAESuv7Iny7X/3gPcfBrPB1pJkn1VSa7Zxl0egQbCmLxbYqRcTxY9oJjjt mlB/u7iHPSP1Vpnr8wMOhOrRlJ2tKz9dDiMn1cxbz7CABmon/4Ocl+IDO1bb6x3B 9cYL7gty1WOe/hI9V/SIG1HDfqyFc31HPHcoUh+KzUoRGMuaCYHrqSAxTgre95XY NKjgCBKgaQIl5NT4UWVHup+wr0yH5Z4C0H13Go5geA== -----END CERTIFICATE REQUEST-----
san:ipaddress=192.168.5.20&dns=192.168.5.20&dns=minemeld.klauzi.local&dns=minemeld
Submit and chose "(x) Base 64 encoded" in the next screen before "Download certificate". Save it as minemeld.cer"
Install your certificate on your minemeld box:
Copy the file "minemeld.cer" to your minemeld box via "scp" (or other tool) to your ubuntu account:
$ scp minemeld.cer ubuntu@<ip.add.re.ss>:
On your minemeld box you should now have three minemeld.* files:
- minemeld.key
- minemeld.csr
- minemeld.cer
Next steps are creating a .pem file and copy the files to the nginx config directory and restart the server:
Create .pem file:
# openssl rsa -in minemeld.cer -in minemeld.key -out minemeld.pem - Enter your pass phrase
Backup your files:
# cp /etc/ngnix/minemeld.cer /etc/nginx/minemeld.cer.orig
# cp /etc/nginx/minemeld.pem /etc/nginx/minemeld.pem.orig
Copy the new files to "/etc/nginx/": # cp minemeld.pem minemeld.cer /etc/nginx/ Restart nginx server: # /etc/init.d/nginx restart
That should make it!
Hi @Angelo, you have a small typo in the second path for nginx:
[minemeld ~]$ sudo mv /etc/nginx/minemeld.cer /etc/ngnix/minemeld.cer-orig
[minemeld ~]$ sudo mv /etc/ngnix/minemeld.pem /etc/ngnix/minemeld.pem-orig
Should instead be:
[minemeld ~]$ sudo mv /etc/nginx/minemeld.cer /etc/nginx/minemeld.cer-orig
[minemeld ~]$ sudo mv /etc/ngnix/minemeld.pem /etc/nginx/minemeld.pem-orig
Thank you for this post.
I didn't really see the need for transfering the pem/pfx over scp.
1) My base64 private key was encrypted (I generated it from a Palo Alto Firewall). Use the command below to decrypt it:
openssl rsa -in ssl.key.secure -out ssl.key
2) Copy then edit existing certificate and private over SSH using VIM or nano.
sudo vim minemeld.pem
3) Restart Nginx:
sudo /etc/init.d/nginx restart
@iThreatHunt: Could you, please, elaborate a bit more your question? Are you looking for a step-by-step guide on how to use PANOS/Panorama as a PKI to generate certificates?
My Palo cannot access to Minemeld. It show URL access error. I think that the certificate may be wrong and No log in access.log (Minemeld)
@iThreatHunt : Would you, please, take a look at the "Step 5" in the article Using MineMeld to generate IP lists from wildcards . I captured some screenshots of that process.
Is it possible to generate a certificate without a passphrase for the minemeld server? The PA cert requires a passphrase, and when I install it on minemeld, nginx comes up and shows the new cert in my browser but still says it's invalid, I think because nginx does not have the passphrase when starting.
I found the answer on Digicert. It's fairly simple one liner to remove the key from the passphrase.
#openssl rsa -in minemeld.key -out minemeldinsecure.key
- Enter your passphrase
It will prompt you for the original passphrase then create the new file without one.
- 53314 Views
- 10 comments
- 3 Likes
- Nominated Discussion: Move Firewall to new Panorama in General Articles
- Nominated Discussion: Web-Gui Access With No Secure Certificate in General Articles
- Running MineMeld using Docker in General Articles
- Evaluation 8.x Configuration Guide Baseline Prevention Mode in General Articles
- Send IOCs to Microsoft Graph API With MineMeld in General Articles
-
"Address Objects"
1 -
10.0
2 -
10.1
2 -
10.2
3 -
8.1
1 -
9.0
1 -
9.1
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
administration
6 -
Administrator Profile
1 -
Advanced URL Filtering
2 -
Alibaba
2 -
Alibaba Cloud
3 -
Ansible
1 -
antivirus
1 -
API
2 -
applications
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
3 -
AWS
6 -
Azure
1 -
Basic Configuration
4 -
Beacon
2 -
Beacon2020
1 -
Best Practices
2 -
Block List
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
Chrome Search Extension
1 -
CLI
4 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
Cloud NGFW
1 -
Cloud Security
1 -
Commit Process
1 -
Community News
1 -
Configuration
9 -
Configure Next Generation Firewall
1 -
console
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
4 -
COVID-19
1 -
cyber elite
1 -
Cyberelite
11 -
dag
2 -
Debug
1 -
debugging
1 -
Default Policy
1 -
Deployment
1 -
discussions
1 -
EDL
3 -
Education
2 -
Education and Training
2 -
Education Services
2 -
Educational Services
1 -
Effective Routing
1 -
Endpoint
1 -
ESXi
1 -
events
1 -
expedition
1 -
export
1 -
failover
1 -
FAQ
1 -
Filtering
2 -
Firewall
2 -
Firewall VM-Series
2 -
gateway
1 -
Gateway Load Balancer
3 -
Gateway Loadbalancer
2 -
GCP
5 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
Github
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
8 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
3 -
google cloud platform
4 -
GWLB
3 -
Hardware
2 -
hash
1 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
ike
2 -
import
1 -
Installation & Upgrade
1 -
IoT
2 -
IoT Security
1 -
IPSec
2 -
kerberos
1 -
Kubernetes
1 -
Layer 2
2 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
log forwarding
1 -
Log4Shell
1 -
Logging
1 -
login
1 -
Logs
2 -
Malware
1 -
Management
8 -
Management & Administration
5 -
MFA
1 -
microsoft
2 -
Microsoft 365
1 -
minemeld
25 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
Network Security
37 -
network-security
1 -
Networking
1 -
New Apps
1 -
News
1 -
next-generation firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
4 -
NGFW
21 -
NGFW Configuration
10 -
Objects
2 -
Oracle Cloud
1 -
Oracle Cloud Infrastructure
1 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
17 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS 9.1
1 -
Panorama
7 -
Panorama 8.1
1 -
Panorama 9.1
1 -
Panorama Configuration
2 -
Panorama HA
1 -
PBF
1 -
PCNSA
2 -
PCNSE
2 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma
1 -
Prisma Access
5 -
Prisma SD-WAN
1 -
QRadar
1 -
Radius
1 -
Ransomware
1 -
region
1 -
Registration
1 -
Release Notes
1 -
reporting and logging
1 -
Routing
1 -
SAML
1 -
SASE
2 -
script
2 -
SD WAN
1 -
SD-WAN
1 -
SDWAN
1 -
Search
2 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Session Packet
1 -
Setup & Administration
7 -
Split Tunneling
1 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Logging Service
2 -
Support Guidance
1 -
syslog
1 -
Tag
2 -
Tags
2 -
Terraform
2 -
TGW
3 -
threat log
1 -
threat prevention
2 -
Threat Prevention License
1 -
Threat Prevention Services
1 -
Tips & Tricks
2 -
tls
1 -
traffic_log
1 -
Transit Gateway
1 -
Traps
1 -
Troubleshoot
1 -
Troubleshooting
3 -
tunnel
1 -
Tutorial
2 -
Ubuntu 16.04
1 -
Unified Monitoring
1 -
upgrade
2 -
upgrade-downgrade
3 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
15 -
VM-Series on AWS
6 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
2 -
VPNs
3 -
Webinar
1 -
WildFire
2 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2
- Previous
- Next