- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Static NAT in Microsoft Azure
- LIVEcommunity
- Discussions
- Network Security
- VM-Series in the Public Cloud
- Re: Static NAT in Microsoft Azure
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Static NAT in Microsoft Azure
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-16-2017 05:35 AM
Need to Map internal server with Public IP (Static NAT ) with specfic ports exposed to the internet.
I belive the public IP needs to be associated with Azure load balancer .
Request some one to share the config of azure as well the Palo alto config .
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-29-2017 12:59 PM
Hi Amaresh,
The internal server may not need a public IP as it could be access from By Internet users through NAT.
These are the steps to follow:
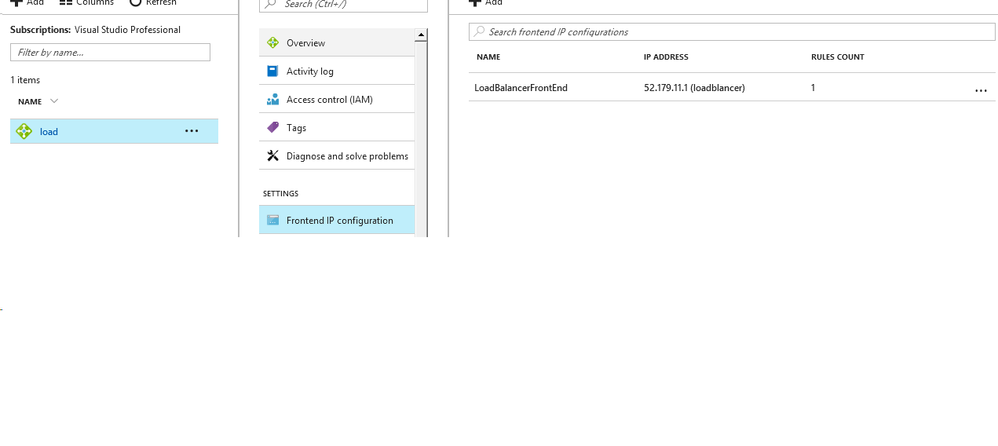
1. assigned a public IP to the public load balancer that front-end the VM-Series FWs
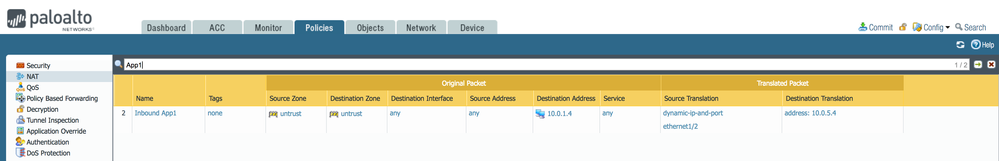
2. add a NAT policy to all the FWs behind the public LB. The policy, I call it "Inbound DNAT". In the original packet section use Untrust in the src and dst zones, and add the IP address of the eth1 FW interface. In the Translater packet section use Dynamic IP and Port as Translation Type, Interface Address as Address Type and ethernet1/2 as Interface (leave IP address as None). Select the Destination Address Translatation and type either the IP address load balancer that front ends the internal server farm or the IP address of the internal server (private IP - make sure is static so if you reboot it does not change)
You also need to configure routing on the VM-Series and routing entry in the UDR to direct traffic in the internal server subnet through the VM-Series.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-30-2017 02:09 AM
Does it require to configure NAT Inbound rule on Azure ?
Consider the scenario as mentioned below
Public IP (Load balancer ) Front end- 13.182.82.10
Unrust Interface - 10.0.1.4
Trust Interface - 10.0.2.4
Internal server -10.0.5.4
Port to be exposed - RDP and 443
Could you help me with the NAT rule on palo alto firewall.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-30-2017 05:54 AM
Hi Amaresh, there are 2 ways you can do this:
1. Create a NAT policy that doesn't filter for inbound port so that you can account for both RDP (3389) and 443 coming into the same host. Then rely on your security policy to allow only the applications/ports you wish.
2. Create 2 separate NAT policies, one that filters specifically for port 3389 and one that filters for 443.
I've provided an example below of #1
You will also need a corresponding Security Policy with the source zone of Untrust and the Destination zone of Trust, for the appropriate applictions that you want to allow access to. The Destination IP would be 10.0.1.4 in this case. You can leave the destionation IP set to any if you prefer to see the destination IP show up in the traffic log, and adjust the Security Policy after the fact.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-04-2017 06:28 AM
Thanks for the reply
Still am not able to access the server with static nat config.
Kindly find the config
On Azure
Note - From machine 10.0.3.5 able to acces internet . But static nat is not working
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-04-2017 07:32 AM
Hi Amarash, have you created all of the necessary load balancing rules, probes, etc.? It might be worth contacting your Palo Alto Networks sales team who may be able to assist and get you up and running.
You need:
Front Side IP Address
Backend Pool
Health Probe
Load Balancing Rules
Corresponding port open on the firewall or wherever your health probe is going to
Corresponding security rules to allow the health probe to pass
The correct routes on your VM Series to account for the health probe(s)
- 10535 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Upgrading 10.1.11-h5 to 11.1.2 directly ? in Panorama Discussions
- After Endpoint Traffic Policy Enforcement, client can not be access microsoft login portal for smal auth. in GlobalProtect Discussions
- Palo Alto with Azure SAML issue in GlobalProtect Discussions
- Unable to access the web end point when the VM series is deployed in Azure availibility zones in VM-Series in the Public Cloud
- Configuration demonstration of this procedure in VM-Series in the Public Cloud