- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect: User/Device Context and Compliance
- LIVEcommunity
- Products
- Network Security
- GlobalProtect
- GlobalProtect Articles
- GlobalProtect: User/Device Context and Compliance
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 04-10-2020 12:06 PM - edited on 07-11-2022 08:30 AM by jennaqualls

In my previous article, "GlobalProtect: Expanded Setup," we covered the expanded setup of GlobalProtect, which included multiple authentication types, as well as the creation of an internal gateway.
In this post, we are going to modify security policy matching based on user identity and device context provided via the GlobalProtect app. We will also enable notifications to the end user based on compliance of the endpoint. You can see a diagram of the environment here.
The value in leveraging user identity and device context in security policy along with end user notifications allow for greater visibility as well as more granular control over what users can access. This same methodology is applicable regardless of user location, and best practices dictate that they should be leveraged wherever possible. If a user is outside of what is required in order to access resources, they can be notified or mapped to a different rule to provide the minimum level of access required in order to become compliant.
NOTE: This article assumes that you have already followed the previous articles in this series.
Part III - User/Device Context and Compliance
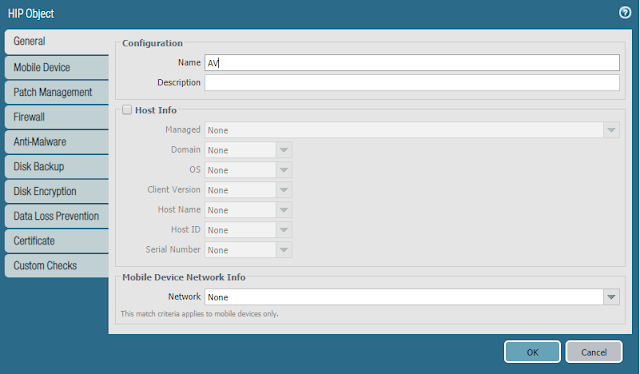
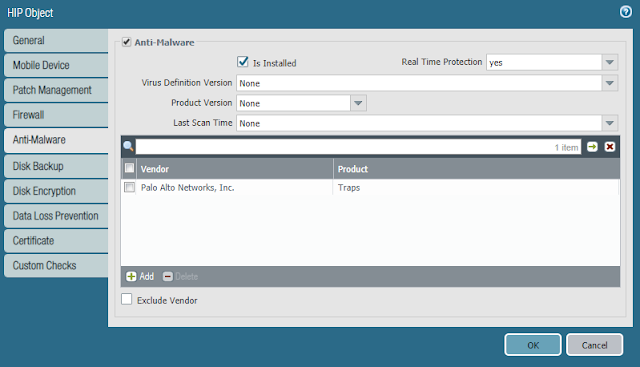
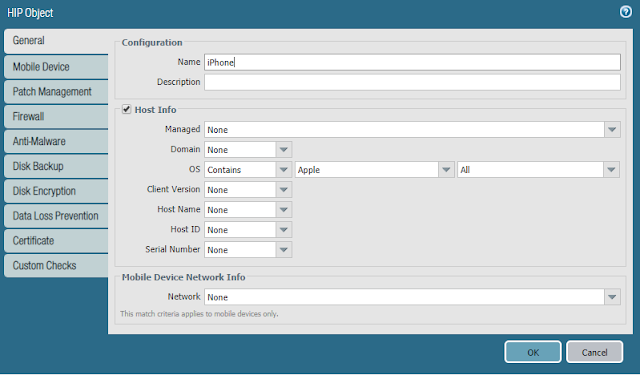
- Navigate to Objects > GlobalProtect > HIP Objects > Add to create one or more test objects that are applicable to your environment
- Name the HIP Object and enable, checking for something specific to your environment. In my case, I run Cortex XDR Prevent on my workstations, and I will be also testing via an iPhone, so I will create two objects called AV and iPhone.
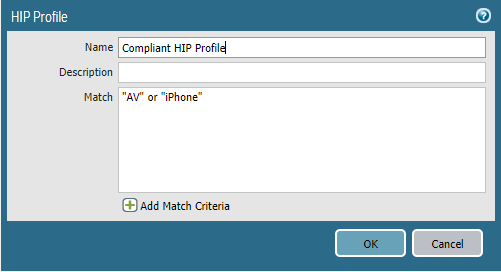
- Navigate to Objects > GlobalProtect > HIP Profiles > Add to create a profile that references both of the previously created objects
- NOTE: In the screenshot below, the profile will match based on either of the previously created objects
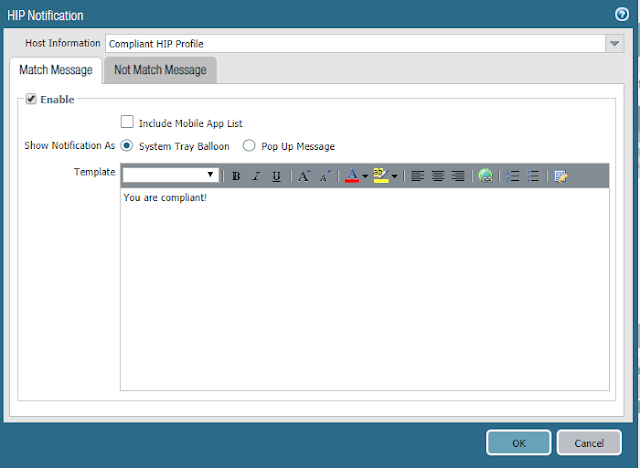
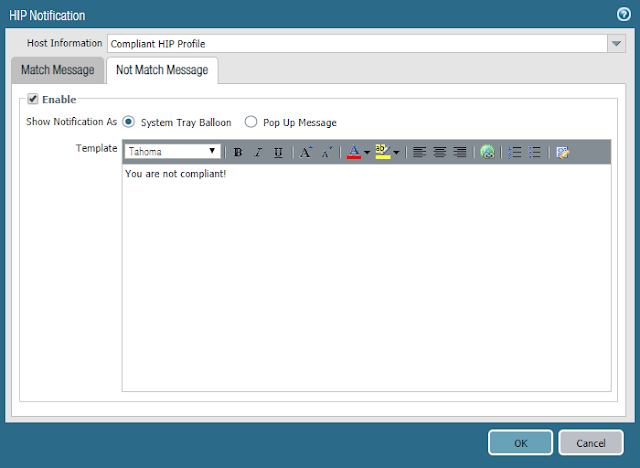
- Navigate to Network > GlobalProtect > Gateways > open each of the existing gateways > Agent > HIP Notification > Add
- Select the Host Information profile that was previously created
- On the Match Message tab
- Check the Enable box
- Enter a message
- On the Not Match Message tab
- Check the Enable box
- Enter a message
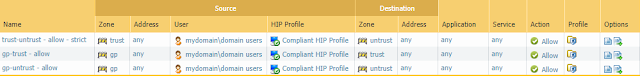
- Navigate to Policies > Security to create rules based on user group and device context
- As shown below, we are adding a user group and HIP profile as match criteria
- Commit the configuration
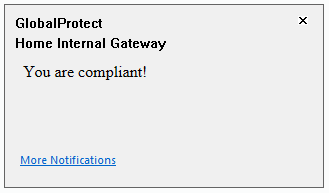 GlobalProtect - Home Internal Gateway Compliant
GlobalProtect - Home Internal Gateway CompliantYou should also be able to see rule matches via the Traffic logs.
In my next article, "GlobalProtect: Authentication Policy with MFA," we will configure authentication policy with MFA for both HTTP and non-HTTP access to sensitive resources.
- 8140 Views
- 0 comments
- 0 Likes
- GlobalProtect Portal Internal Gateway Not Filtering by Source IP Address in GlobalProtect Articles
- Updates on Certificates for GlobalProtect App Log Collection Feature in GlobalProtect Articles
- New Feature (Disable Local Subnet Access) for Linux Clients in GlobalProtect Articles
- Seamless Login With GlobalProtect (Client Certificate Authentication) in GlobalProtect Articles
- GlobalProtect App Log Collection and Troubleshooting FAQ in GlobalProtect Articles




