- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
About traffic-stop-on-logdb-full feature
- LIVEcommunity
- Discussions
- General Topics
- About traffic-stop-on-logdb-full feature
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
About traffic-stop-on-logdb-full feature
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-26-2017 12:56 PM
We're receiving multiple alerts "SYSTEM ALERT : critical : Traffic and logging are resumed since traffic-stop-on-logdb-full feature has been disabled ." for one fo the device, what needs to be done ? Please advise.
Thank you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-28-2017 12:18 AM
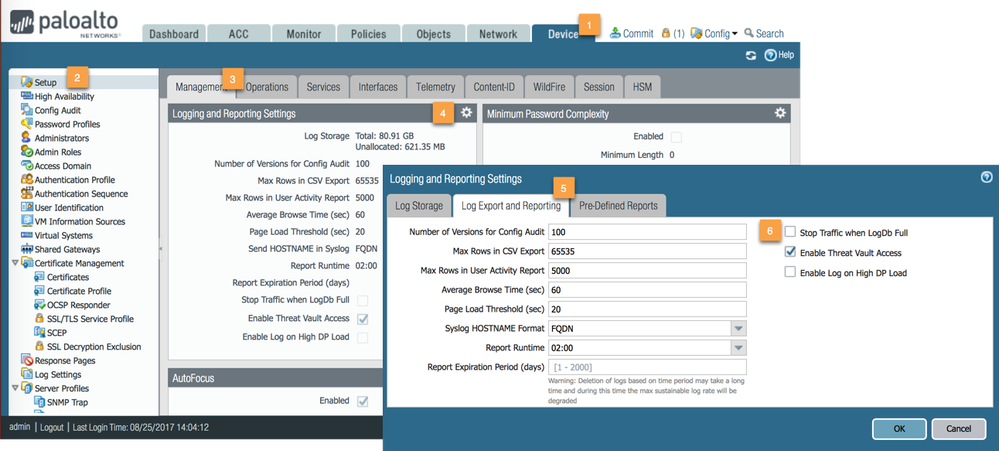
you'll want to verify the stop traffic on log full setting as displayed below
what version of PAN-OS are you running?
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 07:46 AM
@reaper other option on this screenshot "Enable Log on High DP load" is one of most badly worded option in Palo GUI.
Can you suggest internally to rename it. For example "Log High DP load".
Currently it seems that logging will be stopped when DP is high but actually System log is written.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-11-2017 12:19 PM
Today I also experienced this critical system log entries. The firewall is running PAN-OS 8.0.2 and the setting "Stop Traffic when LogDB Full" is NOT enabled. The log entries were flooding the system log with up to 400 logs / second. Unfortunately I was not able to resolve the issue and suddenly the firewall stopped processing connections completely. I then had to shut down ALL ports (dataplane interfaces were not enough to trigger a failover) because ssh, https and panorama context switch wasn't possible anymore ... was really fun today 😛
Any advice regarding this situation?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-11-2017 12:56 PM
@Remo whoa that doesn't sound good
I hope you got a techsupport file while it was in this state or were able to reach support
It sounds like something completely different was going on as the stop traffic option leaves your firewall in a rather 'relaxed' management state since its only blocking traffic from that point on (i never really understood this option but I guess there's a business need)
This sounds like the whole system was affected including several auxiliary daemons
There's not a lot of advice i can give for such a situation: the best thing is to contact TAC and resist the urge to reboot your firewall while they collect debug data
Too many times I've had cases linger for a long time because the firewall was rebooted, prior to contacting support, and was in a healthy state with nomore indication of what happened
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-11-2017 02:16 PM - edited 09-11-2017 02:21 PM
Ok, these problems probably aren't related in any way. It's just bad luck.
After a few hours I decided to enable ONLY the managment port again --> complete cluster was down again ... I am going to contact support now as I did not reboot till now ... the problem is that the generating a tech support from the console also fails ... so there is definately something wrong here 😛
EDIT: up to 1000 logdb-full system logs / second
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-26-2017 06:40 PM - edited 10-27-2017 12:43 AM
I have a customer running PAN-OS 8.0.4 on a PA-5050 and their firewall is generating thousands of these very same System Critical Log Messages, "Traffic and logging are resumed since traffic-stop-on-logdb-full feature has been disabled" daily (dozens by the second continually). And the setting within your screenshot is NOT checked (Stop Traffic when LogDB Full). However, I believe this is a known issue and is being addressed.
Palo Alto Networks® | 3000 Tannery Way | Santa Clara, CA. 95054 | Mobile: +1-650-743-6232
- 7224 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- IoT Devices in Panorama in Panorama Discussions
- Release notes Prisma Browser in Prisma Access Browser (PAB) Discussions
- Intelligence Stream 504 Error, PCC v.33 in Prisma Cloud Discussions
- why PAN‑OS version 12 is often considered not recommended in General Topics
- Ingest GlobalProtect logs to Cortex in Cortex XDR Discussions