- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Application and services in security policy rules
- LIVEcommunity
- Discussions
- General Topics
- Re: Application and services in security policy rules
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Application and services in security policy rules
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-08-2022 05:34 PM - edited 06-08-2022 05:48 PM
Hi I have a question,
Following rule,
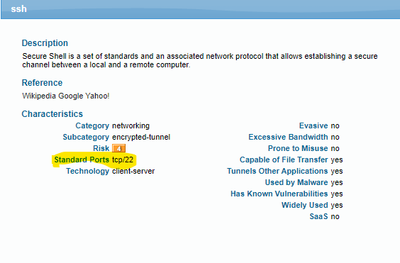
Application allowed- DNS,SSL,WEB-Browsing
Service allowed - TCP port 22
I understand DNS, SSL and Web-browsing would be allowed on port 22, but my question is SSH traffic would be allowed by this rule as I am allowing port-22 via service.?
Also My second question, would DNS traffic be allowed on its standard port 53 via this rule?
My understanding is Palo matches Both Services and Application together, hence SSH traffic would be blocked in this case and DNS traffic on port 53 would also be blocked?
Referring this article - https://live.paloaltonetworks.com/t5/blogs/what-are-applications-and-services/ba-p/342508
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-09-2022 01:49 AM
The service configuration limits which ports the applications are allowed to use
Setting tcp-22 in the services limits ALL applications to only be allowed through tcp:22 (so DNS will need to use TCP 22 instead of UDP 53)
if DNS needs to be allowed too, you'll need to add udp53 to the services
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-09-2022 07:59 AM
Hello,
While there maybe a reason for restricting the application traffic, I would break these out into their own separate policies. This way you have tighter control over applications and which ports they can/should use.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-09-2022 04:09 PM
Hi Reaper,
That makes sense but just confirming SSH traffic will also be blocked in the case as I have not allowed SSH in application section?
Please confirm
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2022 05:21 AM
break application out into their own separate security policies and define whatever port you desire to use except you want all the app on the same port 22 and also define udp port.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2022 10:22 AM
Hello,
Correct, you will need to have ssh in the application field to allow the traffic. You will not need a 'service'/port since that is implied in the application.
https://applipedia.paloaltonetworks.com/
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2022 01:11 PM
It would be nice if you could get away with an "and" for app default- AND any port you specify in the rule.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2022 01:14 PM
Hello,
You absolutely can. However the point with the applications is that you dont have to. So instead of a policy that is like:
application = ssh and service = 22/tcp, you can just put in application = ssh.
Thats really it. The firewall knows and can see ssh and knows its only allowed on port 22/tcp by default.
Hope that helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2022 01:31 PM - edited 06-10-2022 01:32 PM
I was under the impression that one rule was either app-default OR you pick the service.
Like
app=ssh
service
app-default OR tcp/22
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2022 01:45 PM
So that means.
Lets says I allowed 5 applications in my rule 1 with "application-default"
The traffic from that rule would be allowed on all standard ports.
Now I have another non standard port to allow.
So I have to make another rule and allow ALL apps on that TCP- NON-STANDARD port.
Does'it not open up all application traffic on that port.
Would'nt it be better if I use the non standard port in same rule 1 and somehow palo allows my 5 applications on their standard ports and also the non standard I added in services section.
That way I can have the traffic going to non standard port allowed and also applications to standard ports allowed in same rule.
That poses less secuirty risk rather than allowing all apps on that non standard port in a new rule?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2022 01:52 PM
Hello,
Let me try this: Lets say you want to allow the following applications:
ssl, web-browsing, and dns and dont put in any service/ports. The firewall will allow traffic that is sees as DNS only on port 53, web-browsing only on port 80 and ssl only on port 443. If DNS tries to use any other port, it will be blocked.
if you put in a policy that allows applications: ssl, web-browsing, and dns and ports 53, 80, 443. Then the firewall will allow any of those applications over any of those ports, ie DNS over 443, 80, 53.
So by not using a specific service/port, you are making your security policy that much stronger. If you want to allow an application say DNS over port 443, you will need to have a special policy that allows that. The firewall reads policies top down, left to right. Once it finds a match, thats what it will use.
Hope that makes sense.
- 11357 Views
- 10 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- VirusTotal Verdict Change Request for False Positive in VirusTotal
- Migrating Cisco multi-contexts into one vsys Palo Alto firewall in General Topics
- Avaya ports Blocking in General Topics
- Best practices for Palo Alto security policy when destination IP/FQDN is dynamic or unknown in Next-Generation Firewall Discussions
- Regarding ADNSR Licensing and Region Support in Advanced DNS Security Discussions