- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Automate Block IP
- LIVEcommunity
- Discussions
- General Topics
- Re: Automate Block IP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Automate Block IP
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-20-2015 08:46 PM
I know there is like brute-force category, where some may have it automatically block the IP for some duration.
I was wondering if there is a way to block IP for x duration if they were doing like a scan against your system, trying multiple vulnerabilities, sometimes the same ones, sometimes moving down the list depending the type of scan.
Like for example, bash vulnerability x5 attempts, I would like to auto ban this guy for 24 hours or something. But if they do it only 3 times, then try like http, cross scripting, ini files, etc, going down their list, how do I auto block those?
Obviously if they trigger like 5 of them in x time period, they are malicious.
Would DoS and Zone protection play into this somehow or something else?
Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2015 01:26 AM
Hi googol
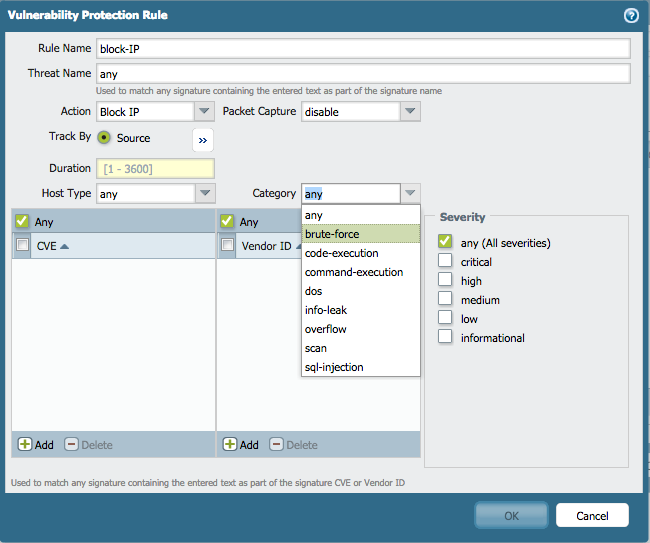
You could combine zone and dos protection to protect against network based attacks, like host sweeps and port scans, with the more granular protection of a Vulnerability Protection profile where you can opt to block an ip for a duration based on the vulnerability category and severity:
hope this helps
Tom
PANgurus - Strata specialist; config reviews, policy optimization
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2015 07:26 AM
What I am hoping to do is not do it for any specific category, but if that IP did it using all different sorts of categories in lets say a 30 second span, I want that IP blocked.
I do not want it to be done just for one, or two, but obviously someone with malicious intent and scanning the system or trying something more than what they should be doing.
That way in case there is a false positive vulnerability, I am not accidentally blocking legitimate traffic coming from that IP or going to that IP. By having it pass some threshold of lets say 5 in 30 secs, there is less of a false positive chance and is mitigated.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2015 02:02 PM
Hello, You might need a correlation logic, especially that you mentioned malicious behaviour on different layers (network, application), being able to investigate an extended time interval. Usually this correlation logic is implemented in a distinct product, SIEM like, with huge processing demand for running queries on logs and flows to get a security meaning from disparate events - the firewall's goal is mainly to prevent atomic attempts and the time-related features are compound signatures operating at application level, with session & transaction visibility, zone protection profiles and DoS protection profiles. There are rudiments of correlation logic in PANOS - Botnet report and the correlation objects recently introduced in 7.0, which are looking for indicators of compromise, but maybe it will be easier to rely on a SIEM product to correlate network and threat events during an extended timespan (how many network scans are passing under detection because they occur at large intervals - seconds) and to trigger blocking via scripting (dynamic groups or dynamic block lists used in firewall policies) - implementing the duration of temporary blocking might be a challenge too. Sorry for not providing an opinion with more practical value.
- 3501 Views
- 3 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Automation rule to add IP address to EDL in Cortex XDR Discussions
- SSL Inspection issues with GlobalProtect users in General Topics
- Need to allow dropbox sharable url and rest of everything block in Next-Generation Firewall Discussions
- Should we block HTTP range requests? in Next-Generation Firewall Discussions
- Best way to restrict software by digital signer in Cortex XDR Discussions



