- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Avoid Attack from outise in PA
- LIVEcommunity
- Discussions
- General Topics
- Avoid Attack from outise in PA
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Avoid Attack from outise in PA
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2019 02:27 AM - edited 06-24-2019 02:57 AM
HI,
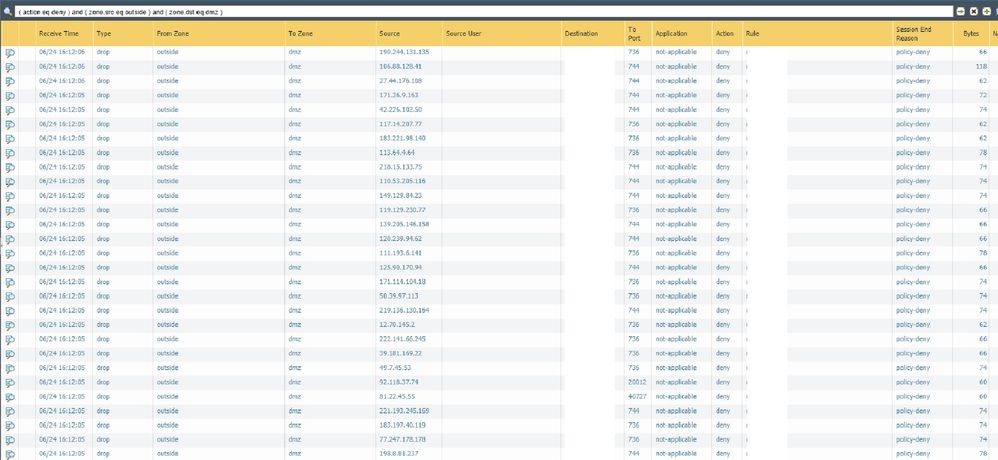
We are having attacks from outside to DMZ. Many diffrents ips are attacking our public range. These attacks are causing packet buffer 100% and CPU 100%, doing an outage in our network. So in traffic logs we can see all sesiones being denied for policy deny. Is there any way to avoid that FW proccess these sessions and not increasing CPU?? what actions can be taken in FW?
thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2019 06:46 AM - edited 06-24-2019 06:48 AM
Zone Protection profile and DoS Protection. Any details on the type of traffic?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2019 07:18 AM
Yes, i enabled but i think with the default paramethers is not helping a lot.
I attach a screenshot where you can see the sessions. Many sessions from differents ipsin the same second.The most of sessions are using the ports 744 and 736.
Any idea for not proccessing these sessions? to avoid impact in CPU
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2019 08:18 AM
I cannot think of anything else to do but to shut down the interface until the attack is over. Let me know if you find an answer as it is an interesting topic. Sorry I cannot help more. If attack is not intended directly to you then it should not last too long. Good luck.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2019 08:31 AM
Which appliance do you have? What is the normal dp load on the firewall while it is not under attack?
You may want to not logging those policy-deny, because it is consuming CPU..
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2019 08:57 AM
PA 3050- normal DP is around 8-10%
sessions count 84564/543435
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2019 09:43 AM
Hello,
You have to tune the Zone Protection and DoS protection limits to your environment. I started by using the default values then halving then and waiting until I found a number that was comfortable.
Sorry there is not a more specific answer. But dropping the traffic at the Zone Protection profile will utilize the least amount of CPU. Also if its from the same IP's over and over you can just put in a block policy at the top and let it drop the traffic that way or contact your ISP and have them block them for you?
Also enable the External Dynamic Lists and have them drop the traffic. If its detected as a vulnerability, anti-spyware, or even Zone Protection, you can block the IP for up to an Hour automatically.
Might be worth a look.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2019 11:37 AM
As @OtakarKlier already mentioned, Zone Protection and DoS Policies aren't something that can simply be enabled with default values and function correctly.
Do you have anything in front of the Firewall that can actually drop traffic, such as a router? If so, you could either start null routing traffic you identify with the firewall logs until you reach substainable levels or create a signature to drop the traffic directly on the router so your firewall can continue to function properly. Outside of that there isn't a quick fix that will really work.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2019 01:40 PM
Perhaps a suggestion to slow/limit may be to take a look at a document I created
It uses a Dynamic Address Group, along with a (somewhat simple auto-tagging from the Log Forwarding Profile) to tag "Bad Ppl", so that when this Address Group hits my DoS Policy, they are immediately dropped.
Not a lot of fine tuning required.
Thanks
Steve
- 7619 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!