- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Block known bad TLDs?
- LIVEcommunity
- Discussions
- General Topics
- Block known bad TLDs?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-02-2015 06:22 AM
My CISO want's to block known bad TLDs (such as .zip or .review) in our Palo. I know how to block specific url(s), but is there any way to block an entire TLD?
I'm running into issues blocking *.zip since it will also block legitimate URL traffic that has *.zip* in its URL.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-02-2015 11:06 AM
Hi Grumpycat, welcome,
did you try blocking *.zip/ with the slash at the end? If that does not work, you might as well either accept false positives (and act upon them manually by allowing custom URLs reported to you in a separate whitelist) or trust to the other defensive mechanisms of firewall (vulnerabilities and threats protection, etc) and create separate custom category for any *.zip and set action to it as "continue", with fair warning to the users that they might be visiting malicious domain and to take extra caution...
Or, to alter suggestion by mvidic, try to play with regex, apps and custom signatures and try to allow certain longer urls that contain .zip in the URL (downloads of zip files...?) but I can't wrap my head around the fact that you want to block .zip but don't want to block it at the same time, can you share offending urls as examples so we can take a look at them perhaps?
Regards
Luciano
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-02-2015 06:49 AM
You could try to define custom applications using regex signatures for http GET requests and block those applications in the security rulebase.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-02-2015 11:06 AM
Hi Grumpycat, welcome,
did you try blocking *.zip/ with the slash at the end? If that does not work, you might as well either accept false positives (and act upon them manually by allowing custom URLs reported to you in a separate whitelist) or trust to the other defensive mechanisms of firewall (vulnerabilities and threats protection, etc) and create separate custom category for any *.zip and set action to it as "continue", with fair warning to the users that they might be visiting malicious domain and to take extra caution...
Or, to alter suggestion by mvidic, try to play with regex, apps and custom signatures and try to allow certain longer urls that contain .zip in the URL (downloads of zip files...?) but I can't wrap my head around the fact that you want to block .zip but don't want to block it at the same time, can you share offending urls as examples so we can take a look at them perhaps?
Regards
Luciano
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-02-2015 11:32 AM - edited 09-02-2015 11:33 AM
Hi,
I just tried with the ".how" TLD and it blocks correctly with the filter "*.how/".
Benjamin
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-02-2015 11:37 AM - edited 09-02-2015 11:38 AM
Hi Benjamin,
FWIW - I think OPs problem was that *.zip filter caught more than they bargained for (it was also blocking any zip file download, I assume) 🙂 I am not sure how their specific .zip download URL was looking like.... all those download links are doing weird things with redirections and stuff, just to force-feed you more ads, maybe it was http://whatever.domain/some_file.zip/than_page_with_ads/something.html 🙂
Thanks for the quick test, tho, everyone appreciates some concrete and quick help.
Regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-02-2015 12:02 PM
Actually, I tried the URL "http://www.howstuffworks.com/a.how" and the firewall doesn't block the request, so the filter seems to do what the OP wanted.
Regards,
Benjamin
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-03-2015 10:17 AM
I have not, but I will definitely try. Thanks for the suggestion!
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-03-2015 10:30 AM
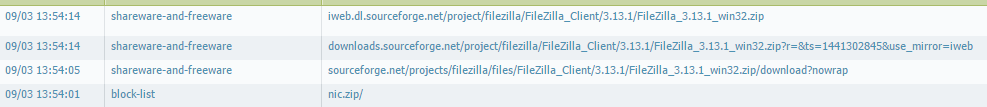
Exactly. Here's a good example of the situation that I ran into when I tried to block ".zip/".
I tested downloading FileZilla at 'sourceforge.net/projects/filezilla/files/FileZilla_Client/3.13.1/FileZilla_3.13.1_win32.zip/download?nowrap'
Looking in my Palo, this URL was blocked. I've also opened up a Palo support case to see if an engineer has any recommendations. Who knows, this may end up as a feature request. 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-03-2015 10:57 AM
Which version of Pan-OS are you using? It works properly on my firewall (v6.1.6) :
Benjamin
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-03-2015 11:03 AM
I'm running 6.1.4. I guess it could be a versioning issue. Let me do some more testing to make sure I didn't flub up on something. I appreciate your ongoing help.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-03-2015 11:54 PM
Hi,
I am not sure how are you going to distinguish between 'something.zip/download?nowrap' and 'sourceforge.net/projects/filezilla/files/FileZilla_Client/3.13.1/FileZilla_3.13.1_win32.zip/download?nowrap'? .... and even something.zip can have subdomains and sub-subdomains, so you can't work around http:// neither....I think that your best guess is still to go with "continue" for this special category, if that matching of .zip/ does not work out 🙂
regards
- 1 accepted solution
- 8117 Views
- 10 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Need clarification on URL Filtering logs in Next-Generation Firewall Discussions
- GitHub Pages Blocked but Accessible on Vercel: Seeking Help in Prisma Access Discussions
- TID 95187 is not on my signature list in Threat & Vulnerability Discussions
- WebEx.exe started being blocked and markete as malware. in Cortex XDR Discussions
- Security settings on NGFW to block dangerous user agent in Next-Generation Firewall Discussions