- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Bypass/Disable Policy for destination address.
- LIVEcommunity
- Discussions
- General Topics
- Re: Bypass/Disable Policy for destination address.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-13-2020 02:52 AM
Hi @mandrake ,
Why don't you add a policy/rule with the certain destination IP before the current policy/rule ?
Or am I missing the point ?
Cheers,
-Kiwi
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-13-2020 03:58 AM
You are right
But I already try it, but works only on personal IP address (PC client IP) and not to if i configure a destination address.
I've a pool of some destination public address that I want to reach without any filter / policy that are now on the firewall.
Just for convenience panos 8.1.x
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-13-2020 09:49 AM
Hello,
Should just be setting the source IP's to any and destination IP's to your group of specific IP's. You can also use User-ID if you have that setup so those destination IP's are accessible only by the Users you specify, or AD group.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-13-2020 11:23 PM
I try but doesn't work. Checking for unused rules it evidence this rule, and I don't want add continuosly source ip addres, but use only the destination addesses.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-14-2020 12:44 AM
Hi @mandrake ,
This should be straightforward to configure.
Are you able to send how you configured it exactly + show us how the session/traffic is actually being identified by the firewall ? This could clarify why it's not hitting your rule.
Cheers,
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-14-2020 05:16 AM
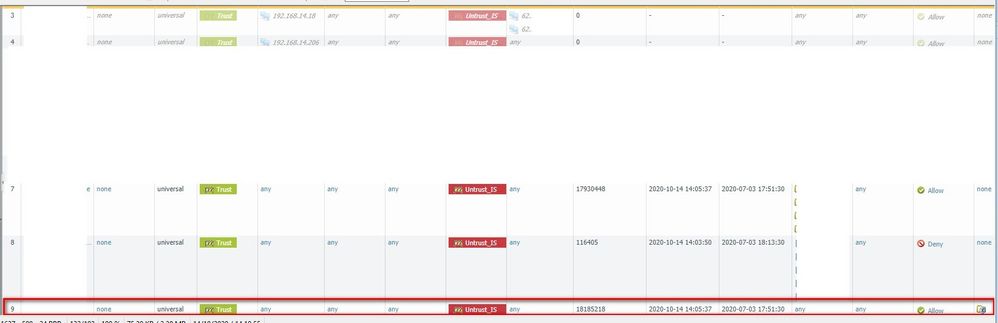
OK, as you can see in this image: rule 9 is the principal rule to go to internet.
If I put the client PC address in rule 4 it works but can reach any IP without security rules
If I put the client PC address and destination IP in rule 3 doesn't works. Also doesn't works using only destination addess.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-14-2020 07:36 AM
Hello,
That is because your rule 4 has the destination IP's set to any. If you put in the destination IP's that you only want to get to, it will then be restricted to only those IP's.
Hope that makes sense.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-14-2020 08:30 AM
You wrong, because I wrote: If I put the client PC address and destination IP in rule 3 doesn't works. Also doesn't works using only destination addess.
Rule number 4 insted of 3 works, but for all DESTINATION ADDRESS.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-14-2020 08:34 AM
Hello,
Please look at your policies. Rule 3 and 4 have different source IP's. Please keep in mind the following:
The firewall reads rules top to bottom and left to right and all set conditions must match. If you provide me the current IP of the workstation and the external destination IP's I can help you write the correct policy.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-14-2020 08:48 AM
Of course there are different IPs I'm trying different configuration from different PC.
But no result with rule 3 or 4 as I expect.
The rule 3 is as you describe before, (source address and destination address) but if try no works, or I check with "highligt unused rules" it marks the rule.
So source IP can be any in the Lan basically 192.168.14.0/24 destination ip can be something else 62.100.200.100; but my goal is not to set the client IP on the rule, but only the destination IP if them change; if possibile, of course.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-14-2020 08:54 AM
Hello,
Try the following:
Source Zone = trust
Source IP = any
Destination zone = Untrust_IS
Destination IP's = 62.100.200.100 (or group or IP/s subnets etc.
Also make sure to enable the rule as they appear to be disabled, all italics, at the moment.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-14-2020 11:28 PM
It was my first try before write in this blog, but doesn't work.
Next I try adding the source IP also and doesn't work too (see rule 3).
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2020 07:05 AM
Hello,
Not sure what is happening incorrectly. However these policies should work correctly. Please make sure that the policies have the proper fields filled in, the policy is enabled, and the configuration is commited.
If this still doesnt work, I say contact support.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2020 07:21 AM
OK so, I need to contact support.
Thanks for your help.
- 44091 Views
- 14 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- XSOAR Upgradtion Issue in Cortex XSOAR Discussions
- NAT mapping public to private IP in General Topics
- Panorama REST API policy creation error with ' 'message': 'Invalid Body', in Panorama Discussions
- XSOAR Upgradtion Query in Cortex XDR Discussions
- Not able to login into URL from behind the palo alto in Next-Generation Firewall Discussions