- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Certificate error on GP access
- LIVEcommunity
- Discussions
- General Topics
- Certificate error on GP access
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Certificate error on GP access
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2020 03:42 AM
Dear Team,
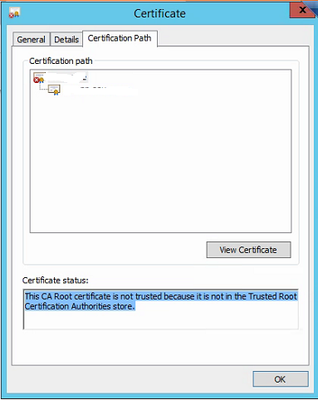
I am facing the issue certificate error while accessing the GP portal. below is the screenshot.
Below is the troubleshooting steps:-
Generated a new self-signed certificate and apply in SSL/TLS.
Same certificate export and configure in the machine as well as browser.
Can anyone help me on this?
Clear the
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2020 04:27 AM
You should generate a CA certificate and then create a new (second) certitfate signed by this CA that you can use for the portal/gateway.
Then export the CA certificate and import it into the trusted sroot signing certificates store of the user
PANgurus - Strata specialist; config reviews, policy optimization
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2020 04:29 AM
The same i have tried but still the issue is the same.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2020 05:11 AM
Please check if your SSL Certificate CN and portal URL/IP are matching? It should match.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2020 05:12 AM
You need to make sure that when you create certificate then certificate attributes has hostname field filled with FQDN.
As Chrome browser gives untrusted warning if hostname is not their in Certificates attribute.
Regards
Help the community: Like helpful comments and mark solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2020 05:50 AM
I have configured the URL for portal access it is matched.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2020 05:56 AM
I want to highlight some points here.
I have observed once i open the portal in edge and internet explorer it is working fine only for some machine.
When i open portal in chrome and firefox then i am getting error.
When i checked the certificate some time is showing certificate is OK.
When i click on root CA it is shwoing below error:-
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2020 08:18 AM
So it would appear that you have some clients that are successfully getting the root CA installed via whatever method you've chosen, but then other machines aren't. You need to look into why some of the machines don't trust the root CA certificate you are using and address that issue.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-06-2020 12:18 AM
Hi @Jafar_Hussain ,
As @BPry correctly pointed out it seems that the problematic machines doesn't have the root CA properly installed. Either it was not installed at all, or it was not installed under "Trusted Root Certificates". It is common mistake when the root CA was manually installed. During the cert installation wizard you can manually select under which section to install the certificate or let the wizard choose automatically for you. However for security reasons windows will never automatically put cert into trusted root certs.
Also have in mind that Chrome, Edge and IE are using Windows certificate store, but Firefox is using separate certificate store. So it is possible that all other browsers to work properly, but to receive cert warning from Firefox. In that case you need to install the root CA in Firefox cert store as well.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2020 02:31 AM
Thanks for your email. As i explain i have configure only root CA with common name IP address and the same certificate installed in client machine trusted root certificate store.
However again i am getting the warning. the same i have checked with child certificate but not able to resolve my issue.
As per my understanding, this is a self-sign certificate from the firewall that is sometimes not trusted by the client machine so i think i need to generate CSR and sign by 3rd party which is already trusted by the client machine. i will import this certificate in firewall. might be it will fix the issue.
Share your openion.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-19-2020 02:10 PM
Hi @Jafar_Hussain ,
Using certificated signed by public CA is probably the way to go (if you don't have internal PKI in your environment). So CSR signed by public CA will definitely solve your certificate warnings.
However the self-signed certificate should work, but the devil is in the details. I just noticed that the warning message from your original post is that the certificate common name is invalid, while you were looking at the CA (if the problem was with browser not trusting the self-signed CA, the warning would be "UNKNOWN_ISSUER". So it seem you probably have not one, but multiple issues.
There is no such think as "self-sign certificate from the firewall that is sometimes not trusted by the client machine" - it is either you have done something wrong, or you don't do something. If you still keen on understanding what is actually the problem:
1. Confirm your self-signed CA is installed in the trusted rot certificate authorities and certificate is listed as trusted when you view cert details
2. Confirm your both certs (GP and CA) are both with valid dates (start date is in the past and end date is in the future)
3. When opening the GP portal for address use what you have put in the certificate Common Name (CN). (common name invalid error could be caused by the fact that you are opening the page using the ip address in the browser, but the certificate to be configured with FQDN)
- 4214 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Can't import a certificate via XML API using C# in General Topics
- Device Certificate for managed device in Panorama Discussions
- failed download GlobalProtect client in General Topics
- Python Script isn't being executed completely in Cortex XDR in Cortex XDR Discussions
- EWS O365 Instance - Not allowed to access Non IPM folder. (85) in Cortex XSOAR Discussions