- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Certificate import issues
- LIVEcommunity
- Discussions
- General Topics
- Re: Certificate import issues
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2012 12:35 AM
I'm having terrible problems importing a trusted certificate into my PA.
I've followed the following guide - https://live.paloaltonetworks.com/docs/DOC-3502
I can create the key ok
I can create the CSR ok
I then submit the CSR to Thawte which then gets authorised and released
If I then try and follow the last command from the URL link above (openssl pkcs12 -export -in my.cer -inkey my.key -out mycert.pfx) i get the error message 'unable to load certificates' and a pfx file is created with 0 bytes
If I then try and import the certificate and key into my PA using Base64 I get the error message 'Import of (cert) failed. Failed to extract certificate'
Please can someone shed some light on where i'm going wrong?
Thanks
Rod
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-15-2012 03:30 AM
Update. This problem has been resolved.
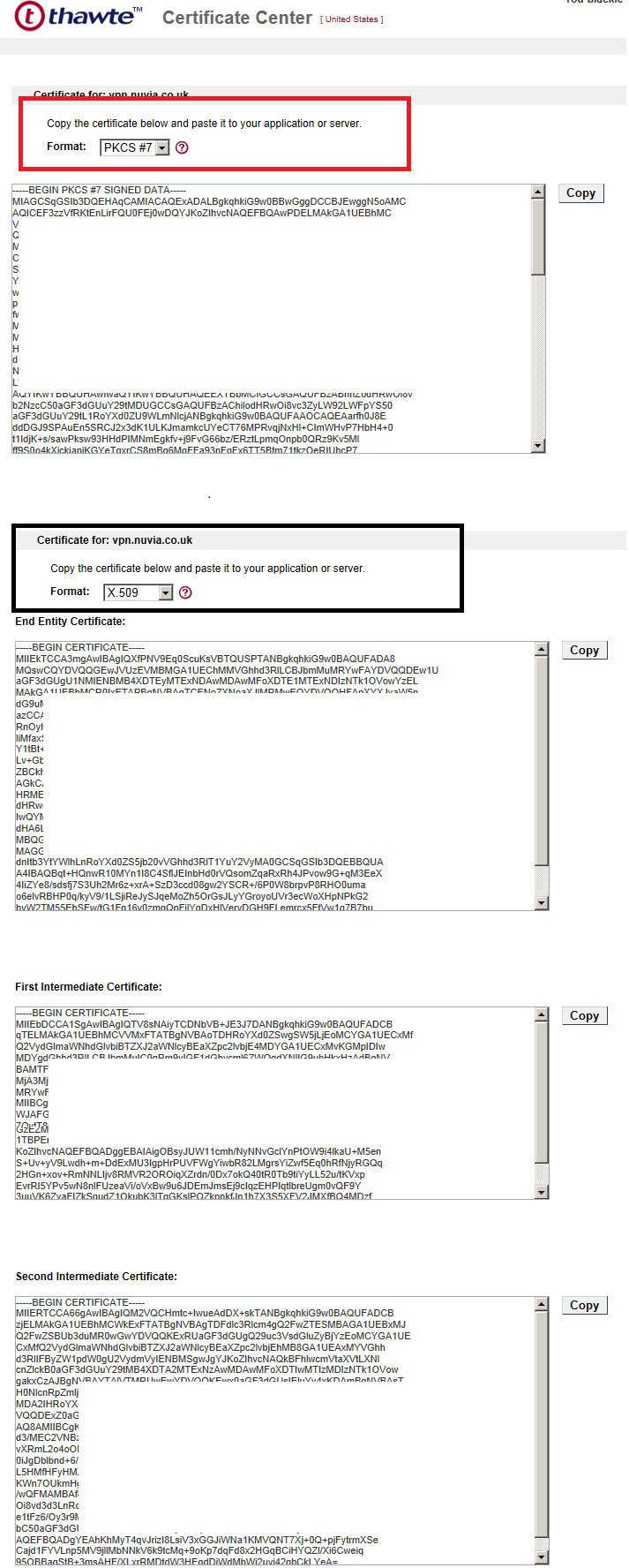
If you look at the X509 certificate image from Thawte that I've included above you will notice that the top box is labelled End Entity, the second box is labelled First Intermediate Certificate and the last box is labelled Second Intermediate Certificate.
Logic would tell you to copy the first, then second and then end certificates into notepad and then go and create your pfx file via openssl. This is where my problems lied.
The correct way to do it is to copy end, first and finally second into notepad. Anyone using Thawte please be aware of this outrageous naming convention.
Rod
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2012 12:47 AM
Verify how the file you got in return from Thawte looks like.
If im not mistaken you should include any intermediate ca-certs in there aswell so the contents of the file from Thawte should look something like (I dont exactly recall the text so this is more of an example) unless im confusing this with something else:
-----BEGIN PUBLIC CERT-----
base64stuff of CA-cert
-----END PUBLIC CERT-----
-----BEGIN PUBLIC CERT-----
base64stuff of any intermediate CA-cert
-----END PUBLIC CERT-----
-----BEGIN PUBLIC CERT-----
base64stuff of Thawtes signing of your key
-----END PUBLIC CERT-----
Which gives if there are more intermediate certs like Thawte Root -> Intermediate 1 -> Intermediate 2 -> Your cert the content should be:
-----BEGIN PUBLIC CERT-----
base64stuff of CA-cert
-----END PUBLIC CERT-----
-----BEGIN PUBLIC CERT-----
base64stuff of any intermediate CA-cert 1
-----END PUBLIC CERT-----
-----BEGIN PUBLIC CERT-----
base64stuff of any intermediate CA-cert 2
-----END PUBLIC CERT-----
-----BEGIN PUBLIC CERT-----
base64stuff of Thawtes signing of your key
-----END PUBLIC CERT-----
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2012 01:22 AM
HI mikand,
Thanks for the reply.
See attached. you get two options from Thawte. Option 1 is a PKCS #7 format that only contains one certificate. Then you get a X.509 option. This contains 3 certificates - End Entity, First Intermediate and second Intermediate.
From your post are you saying I should copy the 3 X.509 options and past them into notepad and save it as a .pem file? if this is try should I follow logic and import the order of the certificates from thawte into my notepad following the format - first, second and then end? or should i follow the top down approach as it's layed out in the image - end, first and second?
When I save it as a pem and import it into the PA do I then select the trusted root CA option? or do I leave all certificate options blank?
Thanks
Rod
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2012 01:57 AM
Yes, I think X509 is the way to go.
And yes I was wrong about the order - it seems that it should be with the most specific cert first like so:
-----BEGIN PUBLIC CERT-----
base64stuff of Thawtes signing of your key
-----END PUBLIC CERT-----
-----BEGIN PUBLIC CERT-----
base64stuff of any intermediate CA-cert
-----END PUBLIC CERT-----
-----BEGIN PUBLIC CERT-----
base64stuff of CA-cert
-----END PUBLIC CERT-----
have a better description of the intermediate problem.
Then on the client side im not sure if its sufficient to just import this as trusted CA (in the client browser):
-----BEGIN PUBLIC CERT-----
base64stuff of Thawtes signing of your key
-----END PUBLIC CERT-----
or if you need to have the intermediates included in the same pem file.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2012 09:59 AM
Did you convert the certificate file from .pfx to .pem?
The key and certificate can be imported separately.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-15-2012 03:30 AM
Update. This problem has been resolved.
If you look at the X509 certificate image from Thawte that I've included above you will notice that the top box is labelled End Entity, the second box is labelled First Intermediate Certificate and the last box is labelled Second Intermediate Certificate.
Logic would tell you to copy the first, then second and then end certificates into notepad and then go and create your pfx file via openssl. This is where my problems lied.
The correct way to do it is to copy end, first and finally second into notepad. Anyone using Thawte please be aware of this outrageous naming convention.
Rod
- 1 accepted solution
- 17487 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- SSL certificate has expired end date after PA decryption in General Topics
- Multi-VSYS 11.2.8 - How to assign a dedicated Forward Trust Certificate per VSYS for SSL Decryption in Next-Generation Firewall Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- Decryption policies and Short-Lived Certificates in Next-Generation Firewall Discussions
- Import Certificate using new Cloud Option in General Topics




