- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
communication between 2 segments in 2 zones diferents
- LIVEcommunity
- Discussions
- General Topics
- communication between 2 segments in 2 zones diferents
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-17-2023 12:43 PM
I have a problem to be able to communicate internally my different segments which are declared in two different interfaces and in different zones.
I dont use vlan's
Eth 1/6= WAN 141.201.78.43/27
Eth 1/8= LAN
10.144.3.19/26
10.144.3.64/26
Eth 1/4= LAN2
192.168.200.254/24
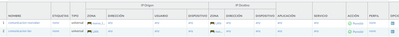
Interfaces
Routes static
policies
I dont use vlan's
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-17-2023 04:51 PM - edited 03-17-2023 04:52 PM
By default, Zone to Zone communication is blocked by the interzone-default Security Policy. So if you want to allow LAN to talk with nueva_LAN you need to create a security rule to allow the interzone traffic. I.e.
Name = Allow LAN to nueva_LAN
Src.Zone = LAN
Src.Address = 10.0.0.0/8
Dst.Zone = nueva_LAN
Dst.Address = 192.168.200.254/24
Action = Allow
Name = Allow nueva_LAN to LAN
Src.Zone = nueva_LAN
Src.Address = 192.168.200.254/24
Dst.Zone = LAN
Dst.Address = 10.0.0.0/8
Action = Allow
Update the above Security Policies to allow what you want based on your internal security requirements. You will also want to modify your Security and NAT Policies for Internet access from the new VLAN:
Name = Allow traffic to Internet
Src.Zone = LAN, nueva_LAN
Src.Address = 10.0.0.0/8, 192.168.200.254/24
Dst.Zone = INTERNET
Dst.Address = any
Action = Allow
You do not need to add anything to the routing table unless you have created multiple routing tables and put the nueva_LAN interface in a different table.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-17-2023 04:51 PM - edited 03-17-2023 04:52 PM
By default, Zone to Zone communication is blocked by the interzone-default Security Policy. So if you want to allow LAN to talk with nueva_LAN you need to create a security rule to allow the interzone traffic. I.e.
Name = Allow LAN to nueva_LAN
Src.Zone = LAN
Src.Address = 10.0.0.0/8
Dst.Zone = nueva_LAN
Dst.Address = 192.168.200.254/24
Action = Allow
Name = Allow nueva_LAN to LAN
Src.Zone = nueva_LAN
Src.Address = 192.168.200.254/24
Dst.Zone = LAN
Dst.Address = 10.0.0.0/8
Action = Allow
Update the above Security Policies to allow what you want based on your internal security requirements. You will also want to modify your Security and NAT Policies for Internet access from the new VLAN:
Name = Allow traffic to Internet
Src.Zone = LAN, nueva_LAN
Src.Address = 10.0.0.0/8, 192.168.200.254/24
Dst.Zone = INTERNET
Dst.Address = any
Action = Allow
You do not need to add anything to the routing table unless you have created multiple routing tables and put the nueva_LAN interface in a different table.
- 1 accepted solution
- 3131 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!