- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Discard UDP from Paloalto Session TImeout
- LIVEcommunity
- Discussions
- General Topics
- Discard UDP from Paloalto Session TImeout
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Discard UDP from Paloalto Session TImeout
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-11-2023 04:40 PM - edited 01-11-2023 04:53 PM
Hello all,
Recently, customers are experiencing a phenomenon that Syslog traffic coming into the same source port remains in the Discarded Deny Session.
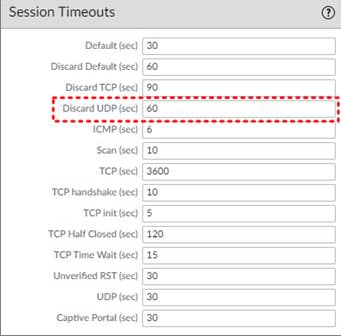
As a result of my checking, it was confirmed that it occurred while being constantly refreshed due to Discard UDP Timeout in Paloalto Session Timeout setting.
Discard UDP : Maximum length of time (in seconds) that a UDP session remains open after PAN-OS denies the session based on Security policy rules configured on the firewall (range is 1 to 15,999,999; default is 60).
Does anyone know why Discard UDP values are needed?
Thanks and regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-12-2023 10:06 AM
Hi @JoHyeonJae ,
This document is a good reference -> https://docs.paloaltonetworks.com/pan-os/10-1/pan-os-networking-admin/session-settings-and-timeouts/....
The Note box indicates that they are optimal values that can be modified "according to your network needs." The UDP protocol has no mechanism to end a session like TCP. Therefore, the NGFW does not know when a session ends based upon packet inspection. It relies on the session aging out. This is why the most common Session End Reason for UDP under Monitor > Logs > Traffic is aged-out.
Notice also that the doc says you can adjust the application-specific timers. If your traffic is identified as "syslog," it has a UDP timeout of 30 seconds that overrides the global timeout. If you are positive it is a timeout issue, you can increase the App-ID timeout. Increasing the global timeouts will result in more active sessions on the NGFW.
This is a great article on session states -> https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClVECA0. Typically discard identifies a security policy or threat detection drop.
I am curious why the NGFW does not create a new UDP session if the old session timed out. As mentioned earlier, UDP is not like TCP with session setup and teardown.
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-12-2023 04:21 PM
@TomYoung
Thank you for your kind explanation.
The cause that NGFW is not creating a new UDP session is still under analysis.
Could you please explain more what are the benefits of setting up Discard UDP timeout?
Thanks,
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-12-2023 05:00 PM
Hi @JoHyeonJae ,
The main value of adjusting the protocol timeouts is so that return traffic will be allowed through the NGFW based upon the session. Most syslog traffic is unidirectional. So, it should not be needed. Are you sure the syslog drops are caused by the UDP timeout value?
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-12-2023 05:04 PM - edited 01-12-2023 05:09 PM
@TomYoung
Yes, a Syslog failure has occurred and I have cleared all the discarded sessions, and syslog Issue has been resolved.
This is the reason why the customer asked me why Discard UDP is needed.
- 7011 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Rollout Strategy: GlobalProtect Disconnect Comments + 12-Hour Auto-Reconnect in GlobalProtect Discussions
- Why do the same Windows Server data collected using XDRC and WEC agents show different statuses in the following fields? in Cortex XSIAM Discussions
- DHCP Relay over SDWAN issue in Advanced SD-WAN for NGFW Discussions
- High Data Plane Utilization During Business Hours in Next-Generation Firewall Discussions
- LGTV and Netflix bugs out when going through Palo Alto in General Topics