- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Do I need a NAT for traffic to pass??
- LIVEcommunity
- Discussions
- General Topics
- Do I need a NAT for traffic to pass??
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Do I need a NAT for traffic to pass??
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-27-2019 02:08 PM
I have an SD-WAN device at my internet edge that will be doing the NATing for the network. This is so that the device can decide which of 3 ISPs to use to forward traffic. My Palo Altos sit behind this device and will do the firewalling and URL filtering. I did not deploy in vwire mode, I cant seem to get traffic to pass through so my quesiton is do I need a nat statement or something regardless of what my SD-WAN device is doing?
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-28-2019 03:10 AM - edited 05-28-2019 03:12 AM
Hi @Stevenjwilliams83 ,
Is it a L3 setup ?
NAT shouldn't be required if you're just passing through the Palo Alto Networks device and you're performing NAT on another device although some additional info on your setup could be useful.
Do you see traffic ingressing and egressing the correct interface ? Are you seeing any return traffic ? Are you allowing the traffic and is your policy being hit ? Are you seeing any drops ?
Cheers !
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-28-2019 05:16 AM
Correct Layer 3 setup.
I see the traffic in the logs but I am only seeing "aged-out".
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-28-2019 07:58 AM
Hi @Stevenjwilliams83 ,
I'm suspecting asymmetric traffic. Is it possible that your return traffic is using a different route ?
Cheers !
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-28-2019 07:58 AM
Negative, only path in and one path out.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-28-2019 01:47 PM
What subnets do you have configured on your "WAN" port (connected to the SD-WAN device) and your "LAN" port? Are they different? Do you have the SD-WAN device set as the next hop in the Virtual Router for the default route (0.0.0.0/0)?
For a strictly L3 routing setup, you don't need NAT rules. But you do need to have your VR setup correctly to route traffic between the WAN subnet and the LAN subnet. And you need your Zones setup, and your Security Policy using the correct Zones.
So, we'd need to see a lot more info than you've given so far.
LAN interface has an IP/subnet that matches clients.
WAN interface has an IP/subnet that matches the private side of the SD-WAN device.
LAN devices --> default route points to LAN interface on the PA.
Virtual Router on the PA includes the two interfaces, has static routes that point to LAN subnet and WAN subnet via their respective physical interfaces, and has a default route that points to the SD-WAN device.
Security Policies allow traffic from "LAN" Zone to "WAN" Zone.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-29-2019 05:56 AM - edited 05-29-2019 06:00 AM
So lets assume I am network engineer and I understand routing, because I do.
Eth1/1 - Zone Untrust IP:10.153.1.6/29
AE1 - Zone Trust IP:10.153.0.1/29
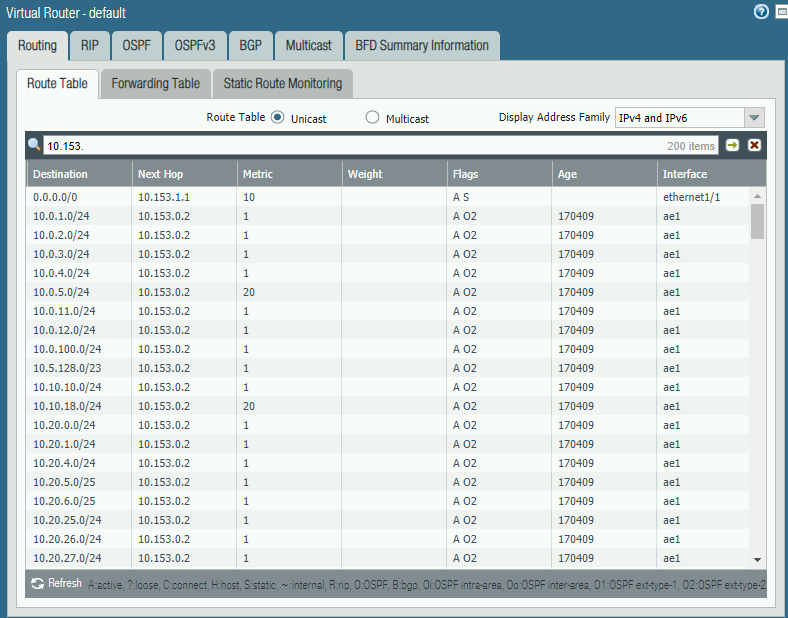
Vrouter - default
- Static route - 0.0.0.0/0 next hop 10.153.1.1/29 (CloudGenix SD-WAN)
AE1 connected to Layer 3 Cisco 3650. Ports connected to AE1 Interfaces on vlan 3101. Cisco Switch has interface vlan 3101 IP:10.153.0.2. Default route on Cisco switch 0.0.0.0 0.0.0.0 10.153.0.1
Palo Alto Vrouter peering OSPF with Cisco layer 3 switch for all internal networks.
Eth1/1 is connected to a switch that is bridging the active/passive PAs with the CloudGenix SD-WAN device (all on vlan 3000) I created an SVI on this switch: interface vlan 3000 IP: 10.153.1.2.
From firewall CLI:
admin@CEN-EDGE-PA-01(active)> ping source 10.153.1.6 host 10.153.1.2
PING 10.153.1.2 (10.153.1.2) from 10.153.1.6 : 56(84) bytes of data.
--- 10.153.1.2 ping statistics ---
30 packets transmitted, 0 received, 100% packet loss, time 29015ms
So this is telling me the outside interface of palos cannot even get to the connected switch.....
Interfaces have Mgmt profile that is allowing network services SNMP and Ping
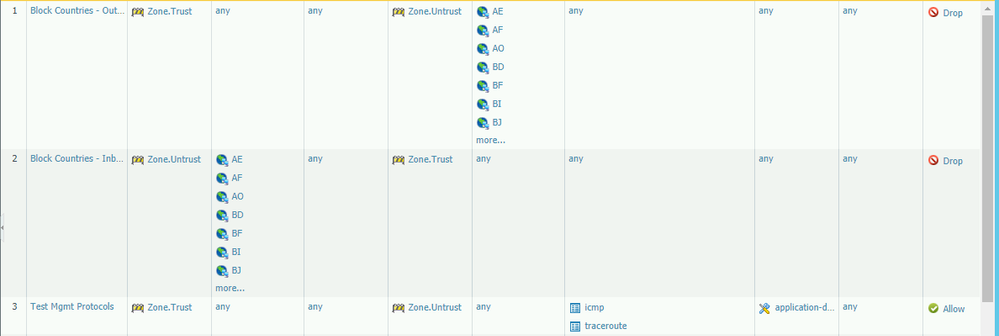
Policy allows ICMP and traceroute.
Routing says default route to SD-WAN device, routes to internal subnets are 10.153.0.2 which is SVI on cisco 3650 connected to AE1 interfaces on Palo.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2019 09:05 AM
Does you rpolicy also allow the ping application, which is separate from ICMP (in Palo Alto terms)? If not, then ping packets won't pass through the firewall.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-01-2019 08:06 AM
The issue was an upstream issue with pretty much a Cisco Layer 2 switch between the firewall and the SDWAN device. It would appear that the palo alto MAC address timelimit is longer then a Cisco Switch and was causing issues with this scenario because production traffic wasnt passing regularly. If it was I would have never seen the issue.
- 9539 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PAC File for Prisma Access China in Prisma Access Discussions
- XQL - Hostfirewall events in Cortex XDR Discussions
- Palo Windows ARP Issue - Windows Hosts Not Installing ARP info in Next-Generation Firewall Discussions
- Jira integration errors in Cortex XDR Discussions
- Existing traffic stops suddenly, and changing of interface MTU resolved it. in General Topics