- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
excluding threats from TAP allerting?
- LIVEcommunity
- Discussions
- General Topics
- Re: excluding threats from TAP allerting?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-24-2018 12:54 AM
We have a TAP interface listening to a number of vlans (internal and external)
We get a lot of noise in our allerts from threats we would prefer not to get alerted on.
For example, presently "SipVicious" scans are occuring all the time to what are actually unused IP addresses on one VLAN.
How can we dial these out???
Thanks
Rob
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 06:15 AM
In this exception you have action 'drop'. That will always be logged. Change to allow in exception.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-24-2018 09:01 AM
I imagine if you are using a TAP interface you are just in the process of actually getting all of this setup, and therefore likely using the default profiles. This will by default cause an alert to be generated, but if you use a profile other than the default you can actually build out an exclusion within the profile to ignore certain threats.
I would be slightly more concerned however that you are getting alerts for scans taking place on the tap interface. Have you properly investigated these and verified that there aren't actually scans taking place across your network for some reason? If it's a false positive then I would look at adding an exclusion into the profile if you truly want to just get rid of the alerts that are being generated.
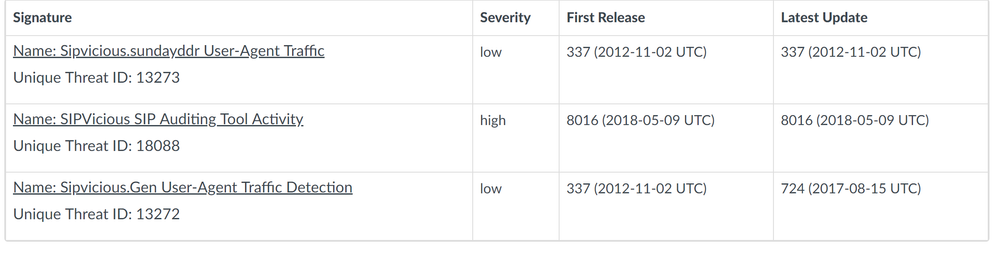
Here's all of the IDs that you would need to exclude from a Spyware profile.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-25-2018 01:27 AM
I do have Specific profiles for the Tap for (AV/AS/VP)
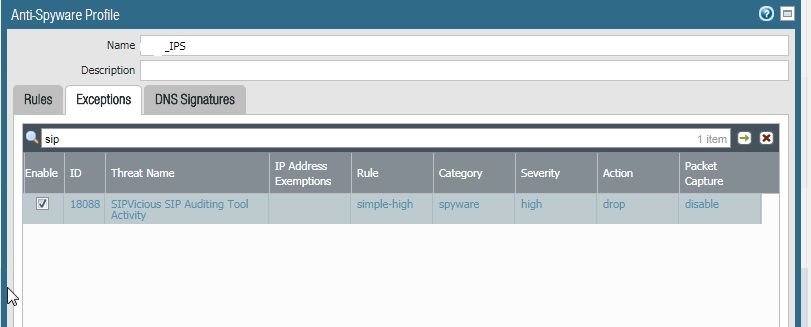
And on the AS profile where SIPVicious can be found I have added an exclusion,
So "SIPVicious" is on the Anti-Spyware profile, I have a exclusion for the "Audit-Tool" as that's the only one we see.
But the alerts still come though.
This particular traffic is on the outside of the network, it's being picked up as there is an un-routed "VLAN" on one of the monitored switch ports.
But we also get a lot of alerts generated because we run our own internal vulnerability scanner, so we generate our own false positive results.
Rob
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 06:15 AM
In this exception you have action 'drop'. That will always be logged. Change to allow in exception.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 08:48 AM
Ah right, will give that a go, althought the scans for that particular threat appear to have stopped now anyway.
Cheers
Rob
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-01-2018 02:17 AM
Thanks,
I am now not getting bombarded by unwanted alerts.
Rob
- 1 accepted solution
- 3604 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!