- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Failed to renew device certificate
- LIVEcommunity
- Discussions
- General Topics
- Re: Failed to renew device certificate
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Failed to renew device certificate
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-17-2021 04:37 AM
Hi
the device certificate is going to expire end of march.
My PA trys to renew it and comes up with the following error:
Failed to renew device certificate.Failed to send request to CSP server.Error: No OCSP response received(dest => 35.238.43.180)
I have no telemetry enabled.
Just activated the certificate with OTP on 2020/12/29 after upgrading to PanOS 9.1.7.
Now it´s the first try of my PA to renew it.
The only thing i found relates to PanOS 9.1.8 wich seems to fix another error with device certificate:
Fixed an issue where the firewall returned the following error message when attempting to request a device certificate using a one-time password (OTP):
Any ideas where to look for?
TIA
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-17-2021 07:46 AM - edited 03-17-2021 08:04 AM
Last traffic to ( url eq 'certificate.paloaltonetworks.com' ) was on 12/29 when the certificate was installed the first time.
No block / deny or other traffic to this url or ip since then.
Seems the PA ist trying to connect to 35.238.43.180 and there is no deny for it.
The mgmt interface has an allow rule but the renew is not working.
This was the traffic from the last 2 days to https://certificatetrusted.paloaltonetworks.com/
The Root CA Palo Alto Networks Inc.-Root-CA G1 that signed the cert for certificatetrusted.paloaltonetworks.com
is not trusted if you browse to the url. But that should not be the problem.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2021 03:12 AM
I have exactly same problem on many devices in different configurations. Nothing is blocked, DNS resolves OK.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2021 04:15 AM
Today i requested a new OTP and choose to Get Certificate on the PA which revokes the actual cert and requests a new one.
The new Cert request finished without problems.
Now i wait til 16-06 to see if the next renew will work automatically or if the problem comes up again.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2021 05:26 AM
same problem here, i also renew the certificates using one-time password.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-02-2022 08:37 AM
allow app 'paloalto-shared-services' to mgmt console rule, your most likely getting blocked. I was
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-16-2022 06:25 AM
Thanks, this is what helped me with getting the device cert installed on a couple of new firewalls.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-21-2022 11:44 AM
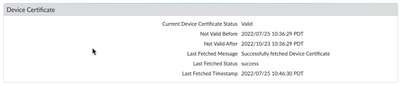
My cert expires in 31 days and I see no way to renew it. I don't have a way to track the firewalls attempts since this happens via the mgmt interface. All I see is the graphic below and it doesn't look like it's tried to connect to the server since the cert was issued.
How do I renew it?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-13-2022 12:37 AM
The Palo normally fetches a new cert by itself before the other expires. There should be no need to get it manually under normal conditions.
I see a link with get certificate wich i used the last time (see my older posting from 2021-03-18).
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-13-2022 07:58 AM
I have no such link.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2022 03:12 AM
Hi @Jason_Lieberman ,
There's a way to fetch it using the CLI:
admin@PA-LAB> request certificate fetch otp <value>
replace <value> with the OTP generated on the support portal.
Hope this helps,
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2022 06:30 AM
While the 'request certificate fetch otp' is not a valid command on my 440. 'request certificate fetch' is. When I ran that is managed to get a new cert. I'm shocked! It's been failing for a few weeks now and TAC is stumped as to why.
Thank you for that.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-10-2022 04:09 AM
Try the solution here on the 440 - it works luckily : https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA14u0000004NlxCAE
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-10-2022 04:11 AM
Then ssh in and try simply:
request certificate fetch
- 30417 Views
- 15 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Failed to generate CSR Device Certificate - PA-520 - in General Topics
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- GlobalProtect MFA with external/USB user certificate in GlobalProtect Discussions
- Is It Possible to Distribute Client Certificates to iOS Devices Using GlobalProtect SCEP Without MDM? in General Topics
- NGFW unable to fetch device certificate due to bug in Next-Generation Firewall Discussions