- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Firmware Updation A-P
- LIVEcommunity
- Discussions
- General Topics
- Firmware Updation A-P
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-20-2020 11:03 PM
Hi Guys,
We have to upgrade firmware of our PA FWs in Active-passive Cluster (It's first time). Referred some online available documents to get familiar with upgradation process but all of them have difference at certain steps (I mean they are not unique). requesting if anyone can share the easy and effective straight forward steps (preferably through GUI).
Usually what is the downtime expected for business critical applications during firmware updating process on Act-Pas setup.
Rgds
Jimmy
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-22-2020 09:54 PM
For HA setup upgrade, 3 hours maintenance window is more than sufficient. Usually it should get completed within 2 hours but having extra time will be always good for you in case you come across any issues.
If you have failure condition 'ANY' for link and path monitoring, in case of any interface goes down or any of the destination mentioned under path monitoring goes down, it will trigger HA failover. So if you purposely make any of firewall interface down using any mean, it will trigger failover and also solve your purpose.
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-20-2020 11:57 PM
Hi @Jimmy20 ,
You can refer below article for the best practices for Palo Alto HA upgrade. You can refer points
Pre and Post upgrade checklist, HA Firewall Upgrade Procedure
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClRrCAK#anchor4
As you have HA firewall, the downtime shouldn't be there if HA failover works fine. I have done several upgrades till date and with HA, if i am doing failover, i had seen only few drops (one or two) to internet. So Downtime shouldn't be there. Still it is mandatory to do firewall upgrade during planned maintenance window for safer side.
Also take care of few more steps before upgrade -
a. Take configuration backup of both firewalls and save file locally on your system before upgrade.
b. Keep all the latest dynamic updates downloaded and installed on both firewalls.
Hope it helps!
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-22-2020 04:08 AM - edited 09-22-2020 04:11 AM
Hi Mayur, So You are recommending to start firmware upgrade first from Primary(Active) unit despite start from Secondary.
Confirming as most of the available docs suggesting to start from secondary unit. And how much time the whole activity will take to complete.
Rgds
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-22-2020 09:09 AM - edited 09-22-2020 09:12 AM
@Jimmy20 ,
The only advantage you get if you upgrade Primary Unit first is
Your HA failover gets tested before proceeding for the upgrade. If you finalized to upgrade Primary Unit first then, initially you need to do HA failover first so secondary unit becomes active if HA failover works fine. Then you can upgrade primary unit as it will be in passive state post failover.
You should never upgrade active state unit directly in case of Active-Passive Setup. If you want to upgrade unit which is in active state at that time, first do HA failover then do the upgrade so there won't be issues to the ongoing traffic...
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-22-2020 10:07 AM
Thanks Mayur..!
How much time usually firmware activity takes to complete (active and passive both).
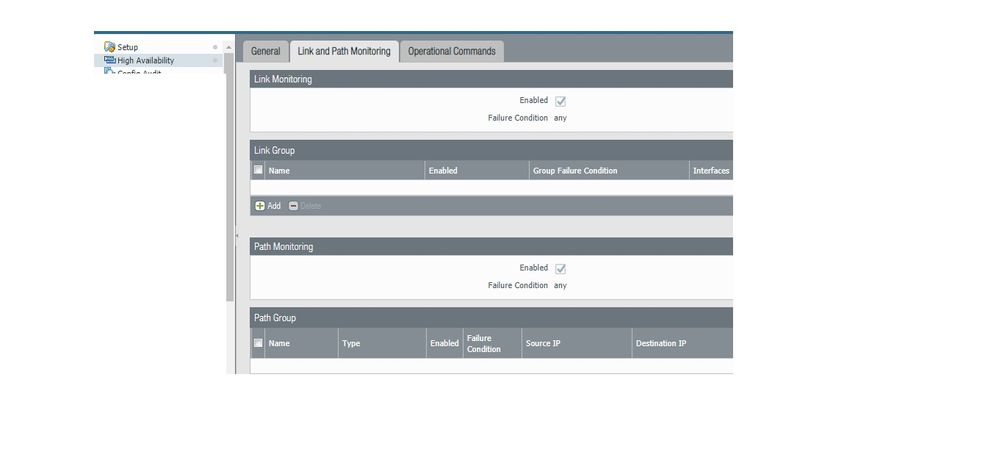
I was checking something today related to "Link and Path monitoring" which is for another activity of failover testing only.
Plan is to disconnect or disable the cable/ Interface from switch end ( any of the connected Interface on PA firewall) This is just to avoid any changes directly on firewall (Eg: Suspend local device) else that would be sort of manual failover.
For now on our firewall Link Group is enabled with "ANY" and Path Monitoring is also enabled with "ANY". except this nothing has been available under Link group (I mean about Interfaces).
Would like to know, if both the mentioned options which are Enabled with ANY ...will solve our purpose or will something additional also need to configure.
Rgds
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-22-2020 09:54 PM
For HA setup upgrade, 3 hours maintenance window is more than sufficient. Usually it should get completed within 2 hours but having extra time will be always good for you in case you come across any issues.
If you have failure condition 'ANY' for link and path monitoring, in case of any interface goes down or any of the destination mentioned under path monitoring goes down, it will trigger HA failover. So if you purposely make any of firewall interface down using any mean, it will trigger failover and also solve your purpose.
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-25-2020 05:41 AM
Hi Mayur,
Just captured a screen shot for Link & path monitoring configuration when we have enabled this time.
Will this be sufficient to trigger failover to passive , if in case we have disconnect / disabled any of the directly connected interface from Active firewall Unit.
Thought to ask here to avoid any understanding gap.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2020 11:36 PM
You need to configure at least one Link Group and Path Group for link and path monitoring respectively. You can also have multiple link & path groups.
Under Link group, you can select all interfaces or specific interfaces under monitoring.
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- 1 accepted solution
- 6489 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Paloalto (PA-440) Firmware upgrade from 10.2.7-h8 to 11.2.10-h3 in General Topics
- OSPF process crashes after manual HA Failover in Next-Generation Firewall Discussions
- Palo Alto 820 - Software Update for CVE-2026-0300 in Next-Generation Firewall Discussions
- Updating Cortex Agent by MDM in Cortex XDR Discussions
- Failed to add authkey / Failed to update DB on Panorama 12.1.6 in Panorama Discussions