- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Getting to internal servers
- LIVEcommunity
- Discussions
- General Topics
- Re: Getting to internal servers
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 12:07 PM
Hello all,
I have a Guest/BYOD Wireless Zone that can get out to the internet just fine. The internet & internal network can get to my webservers just fine. The problem im having is that my Wireless zone can not get an internallyu hosted website from the public IP of my webserver. I do not want any kind of connection or link of the wireless and internal zones (ie be on guest wireless and be able to access anything on the internal network). Any help would be appreciated!
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-03-2017 07:52 AM
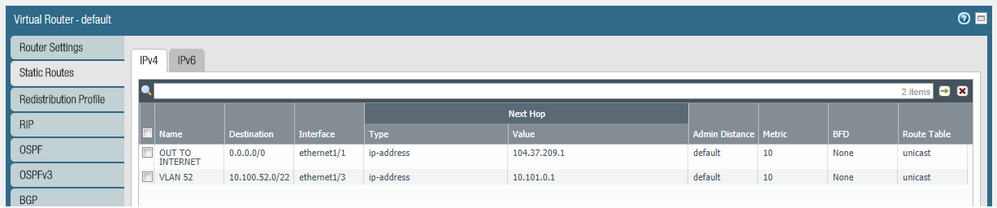
Have it working, had to set up another interface to an outside address on eth1/7 and set up a new virtual router that has my wireless network eth1/8 and 1/7 in it with a static route to the internet. May not be the best solution or best practice, but it works.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 12:14 PM
IS the public IP of your webserver the same public IP that is getting NATd for to your Guest/BYOD wireless zone users?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 12:20 PM
Hi @SNikolaidis
If my understanding is correct, you have the users in the Wireless network, that need to go out to the Internet to hit your Webserver public IP address and come back in to access the actual DMZ server.
If this is the case, we are talking about a uTurn-NAT situation, and it needs to be explicitly configured in the NAT and security policies.
Take a look at this article and let me know if this is your exact scenario.
https://live.paloaltonetworks.com/t5/Learning-Articles/DotW-U-Turn-NAT-Issue/ta-p/53115
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 12:21 PM
The outward internet interface is x.x.x.70 the public ip of the server is x.x.x.10 all on the same class c if that's what you are asking
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 12:36 PM
I think this link video will help you.
If I try to explain here it will not be very interactive 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 12:58 PM
I actually thought that you were trying to access the public IP of your web server while the NAT policy had all traffic from this zone sharing that same IP.
I suspect that @acc6d0b3610eec313831f7900fdbd235 is correct and you simply need to configure the U-turn correctly to get this to function.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 01:23 PM
Thank you I will try it as soon as I get home, Does it make a differance if the server is not in a DMZ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 02:03 PM
That would depend on knowing a little bit more about your routing statements, but in the vast majority of circumstances you would still need a U-Turn.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 03:03 PM
@BPry @acc6d0b3610eec313831f7900fdbd235
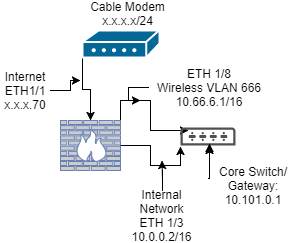
The U-Turn works for my internal network, the problem with the wireless network is it is independant, it only shares the internet interface Eth1/1 and the virtual router with the rest of the network, NAT & Policy & DHCP & DNS Proxy take it straight out to the internet and has filtering and security applied to the Security Policy. It seems to me I need a way to differentiate destination of internet traffic and send the desination 10.66.6.1/16 to that Eth1/8 interface were the 10.66.6.1/16 network resides
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 03:33 PM
You could utilize PBF for that pretty easily but you shouldn't really have to. I feel like if you shared a network diagram along with your NAT policies and routing table we could likely get this straightened out without resorting to PBF.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2017 04:35 PM
But on the firewall is where DHCP, DNS Proxy (8.8.8.8) exist for the gateway 10.66.6.1 . The vlan 666 is completely cut off from anything other than the internet that which 10.66.6.1 gets through Security & NAT Policy to the ETH1/1 x.x.x.70/24 .
We want to keep this wireless network completely isolated from everything other than the internet. That being said, type our domain name into chrome and it just times out. Internally and Publicly everything loads just fine.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2017 06:37 AM
With how you describe it I would expect to actually see the traffic hitting the firewall as it comes back from your cable modem or at least see it trying to hit the untrust zone on your firewall. Have you enabled logging on the default interzone rule and checked the logs to see if you aren't simply blocking the traffic from reaching the server? If you can hit it with intrazone perfectly in your testig I would expect that you simply need to create a security policy to allow the zone tied to vlan 666 to access that web server.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-03-2017 07:52 AM
Have it working, had to set up another interface to an outside address on eth1/7 and set up a new virtual router that has my wireless network eth1/8 and 1/7 in it with a static route to the internet. May not be the best solution or best practice, but it works.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-03-2017 07:54 AM
Actually that may be the best solution for actually making sure that it won't have any chance to get into your production network.
- 1 accepted solution
- 8657 Views
- 14 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- SSL certificate has expired end date after PA decryption in General Topics
- Request to locate account or transfer asset for S/N 023209008637 in Custom Signatures
- how to erase this "Warning Expired Certificate Check" PA-1410 version 12.1.6 in General Topics
- PA-410 commit shows internal error and found that logdb-quota shows abnormal in General Topics
- Enforce GlobalProtect Access Based on Microsoft Intune Compliance Status in GlobalProtect Discussions