- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect & SCCM
- LIVEcommunity
- Discussions
- General Topics
- GlobalProtect & SCCM
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
GlobalProtect & SCCM
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-17-2020 01:35 PM - edited 06-17-2020 01:36 PM
Long story short, we purchased GP and configured rules etc to allow SCCM traffic to and from VPN clients who are users working from Home.
We are struggling to release applications or updates to these users and would like to know if anyone has GP with SCCM configured and working?
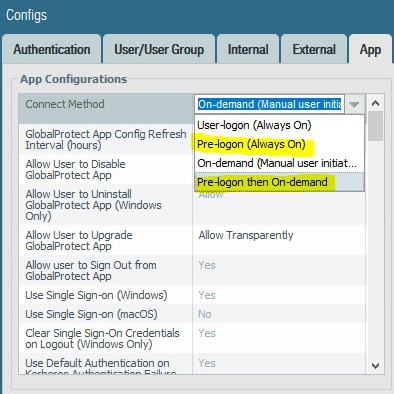
Someone mentioned on a Palo FB forum, that pre-logon should be set for SCCM to work seamlessly.
Anyone able to share some info on this?
Glo
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-17-2020 01:59 PM
What specific issue are you actually having in regards to SCCM? Can users not download updates or applications from SCCM at all, or is it just getting stopped because the user isn't on the VPN long enough for SCCM to check in and get everything downloaded?
If you are pushing updates from SCCM, I would switch over to pre-logon so that the device is connected to your internal network and can actually communicate with your SCCM infrastructure without the user actively logged on and connected to the VPN. Just keep in mind that if these are laptops, depending on how your power profile is set up pre-logon may not actually give you any additional benefit.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2020 07:07 AM
We've got GP being managed / deployed by SCCM. GP connect method is pre-logon / always on. We've done an initial deployment (4.1.6) 2 years ago, with a recent upgrade to 5.0.7 via SCCM all without major issue.
Like @BPry mentioned what are you needing help with?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2020 07:22 AM
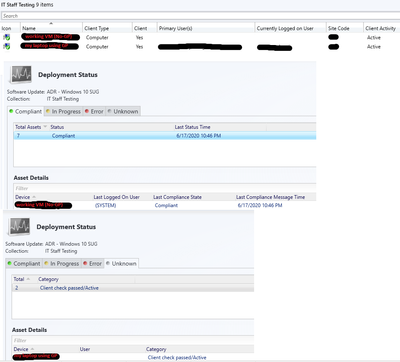
@BPry , thanks for the reply. We are just not receiving ANY deployments at all. SCCM is able to see the client, communicate with it etc. All clients are active when we view SCCM Console. It just wont deploy and we ruled out any SCCM issues when we recently deployed a VM on the same subnet which does not have/need the GP client. So now it all points to Global Protect.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2020 07:31 AM
So that's a completely separate thing then, and switching to utilize pre-logon isn't going to help that issue at all. Just to be sure, have you enabled interzone-default logging or otherwise setup a rule that would log any denied traffic between SCCM and whatever zone you have your GlobalProtect users setup in?
You'll also want to ensure that you've properly setup your boundary groups in SCCM to include GlobalProtect clients. Both those things would be the first things I would look at.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2020 07:32 AM
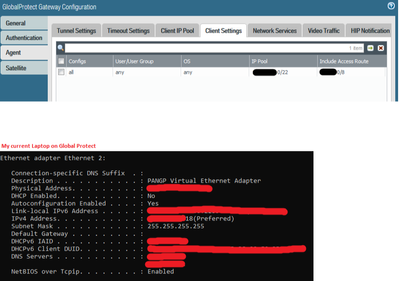
Some random config screenshots:
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2020 07:38 AM
Thanks, indeed - Boundary Groups were the first stuff I checked and they are all in order.
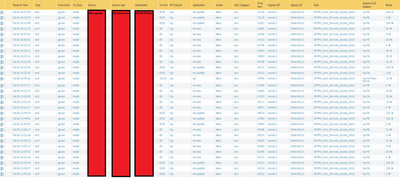
regarding the zones, the Global Protect clients are on a different zone as the sccm primary server, but rules are in place to allow for this:
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2020 12:11 PM
I am also seeing ALOT of aged out TCP (80) traffic . Well actually almost all of them...
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2020 08:23 PM
Do you bytes send and receive in the traffic logs?
Try to do the packet capture on the PA where source is GP Client IP of PC and destination is SCCM server.
Also you can see global counters to confirm that PA is not dropping the traffic.
Also check your threat logs.
Once in PCAP you see no drops and global counter filter and threat logs show no drop or block then it is not the firewall.
Help the community: Like helpful comments and mark solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-08-2021 02:54 AM
Dear all,
I'm sorry I hijacked this thread, but it looks a lot like our problem.
We are currently switching our VPN client from Cisco AnyConnect to PAN GlobalProtect (onDemand) and have a similar problem with ConfigMgr Agent 1910 and PAN GlobalProtect 5.0.9-15.
SCCM in general is working e.g.(un)installing selfservice packages, but new advertisements will not become visible in SoftwareCenter and will also not installed. Also SCCM advertisemnts we updated or changed will not be updated on the machine which is connected with GlobalProtect.
In the meantime we found out that when we restart the "SMS Agent Host" (ComExec) after connected with GlobalProtect everthing works like it should. That means SCCM boundaries are set correctly, all ports are open which are needed to communicate with the ConfigMgr server.
I had running Wireshark for hours but see only "Duplicate to the ACK in frame" which shouldn´t be a problem.
Has somebody an hint or maybe solved this already?
Thank you in advance!
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-19-2021 09:05 AM
Dear all,
Just for information if someone has the same problem, because we had solved our problem.
GlobalProtect client doesn´t set the Connection-specific DNS Suffix, it set the DNS suffix search list only for the network device.
One option is to set the Connection-specific DNS by yourself in the network device or to add your ConfigMgr servers in hosts file (including DNS suffix) - Yes, both options are workarounds only, but they will work.
I hope this helps someone with the same problem.
- 16674 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect, Release Notes, Build Numbers, CVE ?!?! in GlobalProtect Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Globalprotect Client 6.2.7 disconnects multiple times in GlobalProtect Discussions
- Global Protect count current users not match statistics in GlobalProtect Discussions