- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GZIP File - Google Translate
- LIVEcommunity
- Discussions
- General Topics
- GZIP File - Google Translate
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
GZIP File - Google Translate
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-15-2014 05:37 AM
Hi,
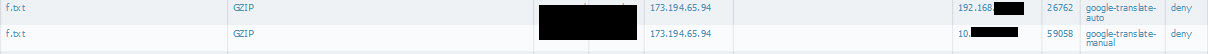
some users reported they are unable to use Google-Translate any more. I saw in the logs, Clients are trying to download GZIP files with the app google-translate-auto and google-translate-manual:
I'm sure, the users were able to use Google-Translate in past. So the problem is since recently.
- Labels:
-
App-ID
-
Configuration
-
Troubleshooting
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 05:29 AM
Hi,
we see also many GZIP (f.txt) download attempts with the app web-browsing.
When we block this download Google Instant and Google Maps does not work anymore.
This behavior started last week.
Our Data Filtering protocols are flooded with such entries.
Does anyone also see such a behavior?
Best regards,
Rainer Grothues
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 05:55 AM
I'm not a web dev guy.. at all..
But I wonder if they are using HTML5 to get the content to you in compressed format (gzip) then using the power of HTML5 to uncompress it within the browser. It would make their service faster and take less bandwidth.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 06:19 AM
SSL decryption was always on. also for google...
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 06:22 AM
It appears my assumption was correct. Google Maps uses gzip compression.
https://google-developers.appspot.com/coordinate/v1/performance#gzip
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 07:19 AM
but since when? And we talking about google translate (ok, maybe google earth is also effected).
I think, it happens after a content update.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 07:31 AM
Sorry Hithead I brought Google Maps into play with my post.
I made the test also with Google Translate and saw the same behavior as you.
Maybe a little change on the ssl decoder?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 07:37 AM
its ok. seems the two problems (apps) have the same root cause.
if we could solve both, google translate and earth, would be nice.
I hope PAN can modify the google apps to let the gzip file passed.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 07:52 AM
You could modify your file blocking policy to allow gzip.
After that all works fine but only if you chose the action allow or forward. Continue does not work.
Nevertheless I would like to know what happened.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 07:56 AM
I know this workaround. but the problem is, I cannot select google-translate as application. Don't want to allow gzip with all applications...
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 08:23 AM
Create a new ACL line which matches on Google Maps and Google Translate. Create a new File Blocking profile for that rule which allows GZIP.
This will allow you to let GZIP work for these apps but the rest of the traffic will match on your previous rules.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 08:28 AM
thank you for your comments guys, but I know this kind of workarounds.
I like to know, if PAN is responsible for this change or Google? And regardless if PAN is able to modify the apps and include gzip as 'necessary'.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 08:35 AM
That is hard to answer depending on many variables.
For example, maybe Google was using TLS1.2 but your PAN was not yet at the version which added 1.2 support so it wasn't decrypting that specific traffic.
Or maybe Google just added GZIP compression to their public services. Or maybe a PAN content update allowed it to better identify GZIP compression within Google apps.
PAN has supported GZIP compression identification for quite a bit though. It even uncompresses and scans GZIP encoded traffic essentially (IPS Scanning of Compressed Files)
As for PAN adding gzip as necessary to the App-ID for the Google Apps, are you just looking for the firewall to tell you that you also need to allow GZIP? Because if you have an explicit deny, I do not believe it auto-allows other needed apps. I think it only does this if you lack an explicit Deny.
But you should always have an explicit deny. ![]()
- 5454 Views
- 13 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Python Script isn't being executed completely in Cortex XDR in Cortex XDR Discussions
- Sliver Framework Command and Control Traffic Detection - ThreatID 86680 in Threat & Vulnerability Discussions
- XDR Resource IPs for Connectivity to XDR Server in Cortex XDR Discussions
- True Positive / no incident / evasion / self made alerts helped to detect in Cortex XDR Discussions
- EVE-NG Setup & VMWare installation for Palo Alto & Multi vendor devices in General Topics



