- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
HA path monitoring in virtual wire
- LIVEcommunity
- Discussions
- General Topics
- HA path monitoring in virtual wire
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
HA path monitoring in virtual wire
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-07-2013 04:05 PM
I've seen a couple answers here about using Path Monitoring in Virtual Wire. They say that one must use an IP address within the Virtual Wire subnet as the source address. OK, I get that. What I don't get is how to configure such an address. I don't see a way to add an address to a vwire interface. I've tried creating a loopback with no good result. Also gave vlan a shot, but that didn't look promising either. Thanks for any help.
- Labels:
-
Configuration
-
Networking
-
Set Up
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2013 01:37 AM
Device -> High Availability -> Path Monitoring -> Path Group -> Add Virtual Wire has the option to add Source and Destination address. I am also working on similar monitoring where I would like to monitor device beyond connected device. I am still not sure how the routing would though. I have a case open with support with not much progress.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2013 04:27 AM
How about configuring a L3 interface on PA and connecting it to the network providing a reachability to the Monitored Dest.
vwaghmar :
Excerpt from Admin guide : 5.0
Source IP—For virtual wire and VLAN interfaces, enter the source IP address used in the probe packets sent to the next-hop router (Destination IP address). The local router must be able to route the address to the firewall. The source IP address for path groups associated with virtual routers will be automatically configured as the interface IP address that is indicated in the route table as the egress interface for the specified destination IP address.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2013 04:49 AM
: L3 interface configuration is what suggested by our SE. The support talked about having src and dst ip in the subnet. That doesn't make any sense when you want to monitor devices beyond connected one. Have you tried this by yourself? Unfortunately I don't have an environment to play with and before touching the production devices, I wanted to make sure that I can plan ready for configuration and testing. I am running 4.x code. Do I need to have a combination of virtual wire and virtual router in the path monitoring config? Can you provide me more details?
Here is what my scenario is (apologies @gmparis for hijacking thread). Internet -> Internet router -> public switch -> Untrust firewall -> Untrust PAN -> Trust PAN -> DMZ switch. I can monitor dmz switch and trust interface of firewall using link monitoring and is working fine. I want to monitor the untrust firewall to pub switch connectivity. Here is what I understood.
- Connect new interface on PAN to dmz switch
- Configure L3 interface with trust side subnet of firewall
- Configure path monitoring with newly added interface? How do I add destination ip? I dont see any option to use single interface under path monitoring.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2013 05:46 AM
No problem about the hijacking, @vwaghmar. Thanks for answering my question. I was trying to test the path monitoring using ping before configuring it into HA. That apparently can't be made to work, but isn't necessary. Just putting the source address into the vwire path monitoring config is all that's needed. I was making it harder than it had to be.
Good luck with your layer-3 issue.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2013 02:03 AM
Hi all
I'll join this thread cause this is exactly what I'm looking for.
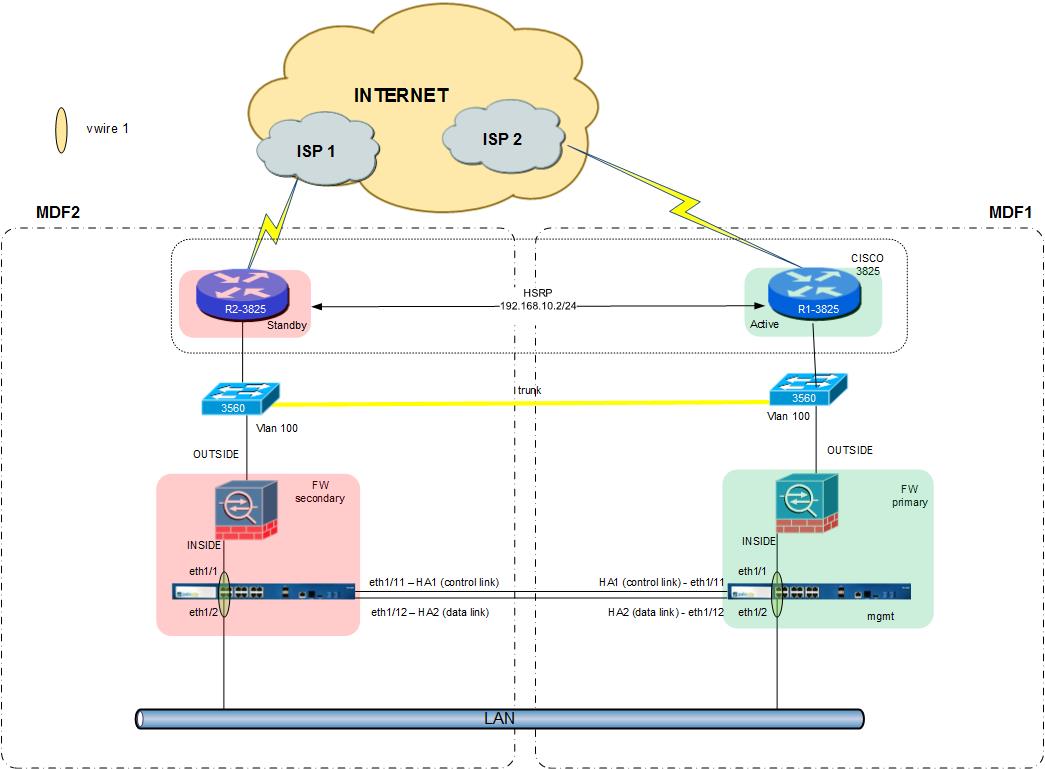
I need to monitor HSRP address of routers because If outside interface goes down on cisco ASA, ASAs will switchover and PANs not.
Do I realy need to create seperate L3 interface just for this purpose? If yes I think that it will be easier to create L3 interfaces on PAN.
regards
Przemek
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2013 03:46 AM
- Looks like we are in the same boat. The ASA failover does not trigger PA failover. Creating a separate L3 interface for monitoring is what suggested by our SE. Here is what I had tried over the last weekend but did not get satisfactory results due to ASA issues in our environment.
- Connect an interface from PAN to LAN switch
- Configure interface in L3 mode. I am assuming that PAN trust/inside is connected to a L3 switch having default gateway as ASA
- Configure new zone
- Configure new virtual router. I preferred to create new as the purpose was to use it purely for HA path monitoring. My PAN anyways configured in vWire mode
- Ping destination using src ping on PAN. Please note that somehow I was not able to ping ASA untrust from inside/trust. I am not sure if that is the feature in ASA but I did not have time to work on it. If you know how then please let me know. ASA egress IP is reachable from public
- Configure path monitoring with type as "virtual router". Configure destination address and select the virtual router with proper routing
- Check path monitoring status from cli # show high-availability path-monitoring
pan(active)> show high-availability path-monitoring
--------------------------------------------------------------------------------
total paths monitored : 1
interval to send ICMP probe packets : 200 ms
last N probes to determine path availability : 10
hold time to send probe packets : 60000 ms
(after device becomes active)
--------------------------------------------------------------------------------
name/type destination succ/total rtt min/max/avg (ms)
--------------------------------------------------------------------------------
ha-monitor-vrouter/virtual-router <destination ip> 10/10 0.80/1.04/0.88
--------------------------------------------------------------------------------
My failover scenario worked fine after shutting down the ASA untrust link. I however had issues later when Active PAN become Primary again. I will be trying the same thing with Juniper firewalls again over coming weekend. If you manage to test in the meanwhile then please share the results.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2013 04:19 AM
thx vwaghmar for your answer.
as I remember you can't ping outside interface of ASA from inside ![]() so don't bother. Maybe if you change "management-interface" for outside (which is not recomended) but it is not easily done casue managemnt-interface can't be the one with the lowest "security-level".
so don't bother. Maybe if you change "management-interface" for outside (which is not recomended) but it is not easily done casue managemnt-interface can't be the one with the lowest "security-level".
Unfortunately I dont have 2 ASAs in my lab to test all interesting parts.
My first question is whether PAN tranfers traffic in vwire when it is in passive mode? It is fundamental question cause
If the answer is yes then it is no use of creating L3 interface for path monitoring cause its default gateway (L3 switch or inside interface of ASA) is always available regardless which ASA is acitve or standby.
When ASAs do switchover the secondary one starts using the IP address of the previous primary one (which is default gateway for internal networks and L3 interface of PAN).
OK I've found the info that traffic handling links on the passive device are in "down" state. Of course it wouldn't make sanse the other way but I had to ask ![]()
As I said I can't test it in a full environment but I have to do it in production ![]() GREAT is it not?
GREAT is it not?
What about your case you've mentioned earlier? is it closed with the solution presented? or still have hope for some trick? idea?
regards
Przemek
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2013 04:35 AM
- Anyways we are getting rid of ASA with PAN so I am not bothered any more ![]() . I wanted to simulate it for other environment.
. I wanted to simulate it for other environment.
Passive PAN in vwire mode will have all its interfaces shut/down. Are you seeing the interfaces UP? Also the traffic will eventually flow from the vwire to reach ASA or gateway so the path monitor will have no data on the passive PAN. Check the output below from passive PAN. There is a possibility that the active PAN will be able to reach the destination ip from the standby ASA (when Active). I did not get time to check about it. I will check with our SE.
pan(passive)> show high-availability path-monitoring
--------------------------------------------------------------------------------
path monitoring statistics unavailable due to inactive device state
total paths monitored : 1
interval to send ICMP probe packets : 200 ms
last N probes to determine path availability : 10
hold time to send probe packets : 60000 ms
(after device becomes active)
--------------------------------------------------------------------------------
name/type destination succ/total rtt min/max/avg (ms)
--------------------------------------------------------------------------------
ha-monitor-vrouter/virtual-router <dst monitored ip> N/A N/A
-------------------------------------------------------------------------------
I tested it in production as well as I have running setup with this limitation :smileygrin:. I am going to try next with Juniper firewall which has the option to assign separate management ip address apart from the floating one to an interface.
As per support, it is not possible to monitor destination which is one hop away/routed. The L3 interface on PAN will have to be in the same subnet as dst address.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2013 05:11 AM
This is my first experience with PAN so sorry for silly questions ![]()
I see the interfaces Down on passive generaly becasue they are not connected to standby ASA (I don't have 2nd one in my lab ![]() )
)
However I've just seen there is an option for default bahaviour.
I didn't get the thing about support.
"L3 interface must be on the same subnet as dst address?"
According to docs (at least for 5.0) it can be done.
You also wrote:
I however had issues later when Active PAN become Primary again
What kind of issues? Did you enable Preemptive option? I think It should be disabled in this scenario as PAN need to follow ASAs.
For now I think I will need to redesign everything and make PAN in L3 mode cause I even have problems with creating vwire subinterfaces and putting them in deferent zones.
https://live.paloaltonetworks.com/thread/7403
Sorry for changing the subject. Do you have similar environment?
regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2013 05:49 AM
As far as I know or seen, PAN in vWire HA deployment will have ports shut on Passive device. I think I had checked/tried that initially and had same results. May be it is something different for L3 mode. My environment is vWire mode only.
I didn't get the thing about support.
"L3 interface must be on the same subnet as dst address?"
Honestly it does not make any sense to me as well as path monitoring is supposed to check path IMO. As per the support the src ip (L3 on PAN) should be part of destination subnet. May be it is limitation for vWire based deployment The option suggested was to connect a cable from PAN to the remote subnet and then configure monitoring of destination IP.
What kind of issues? Did you enable Preemptive option? I think It should be disabled in this scenario as PAN need to follow ASAs.
We had issues with managing secondary ASA after failover. Hence could not check the status on secondary ASA. After a while, the Active PAN was primary. I suspect that is due to the reason that the destination ip was reachable via Standby ASA (when Active). Yes I have preemptive option enabled. That is a good option to check for. Anyways I plan on checking the untrust IP availability and my affected environment has Juniper. I will configure the destination ip separate on PAN which will be the manage-ip of untrust interface (not floating). The aim is to failover PAN if the untrust link to connected switch dies.
I am running 4.x so cant comment about 5.x stuff.
I would love to have L3 environment but redesign is not an option for me considering config on the existing firewalls and criticality of the environment. I am however moving to L3 on PAN in some environment. ASA and PAN back to back becomes redundant. In my environment we are doing lot of stuff on PAN than ASA so we will be replacing ASA.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2013 06:02 AM
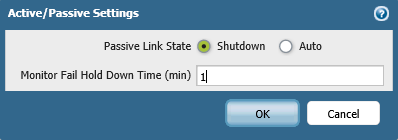
I just checked release notes of 5.0.4 and can see the enhancement in HA options.
• Passive Device Link State Control
–
This enhancement improves failover times in Active/Passive deployments that make use of L2 or virtual wire interfaces by keeping the physical interface link state on the passive device in the link
-
up state. This feature already exists for L3 interfaces.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2013 06:23 AM
We had issues with managing secondary ASA after failover. Hence could not check the status on secondary ASA. After a while, the Active PAN was primary. I suspect that is due to the reason that the destination ip was reachable via Standby ASA (when Active). Yes I have preemptive option enabled. That is a good option to check for.
I think this was your issue - I mean PREEMPTIVE option. As I remember ASA in active/standby mode doesn't behave in a preemptive manner (it can but as I remember only in multicontext mode). So after a while passive PAN regain its connectivity with path monitoring through currently active ASA so it switches again. What is your case?
I've just tried this "Passive Device Link State Control" and I changed it to "auto" as picture presented earlier. However this does not mean that ASA hearbeats can keep going !!! Its true that link is green but thats all. So no connectivity to the secondary ASA will be allowed when the PAN box is passive. This make sense in order to avoid the situation when we could evade the active box and its inspection, but it is pain in the a... when sth behind it needs to send its heartbeats ![]()
regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2013 07:55 AM
BTW - Check the release notes of 5.0.4. You can create sub-interfaces in vWire mode. I think this is what you are looking for???
Virtual Wire Subinterface
–
You can now create virtual wire subinterfaces in order to
classify traffic into different zones and virtual systems. You can classify traffic according to the VLAN tag, or VLAN tag plus IP address (IP address, IP range, or subnet).
- 19377 Views
- 22 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- "More runtime stats" not loading when Advanced routing is enabled in Next-Generation Firewall Discussions
- Newsletter: Cloud Delivered Security Services, Oct-2025 in Advanced Threat Prevention Discussions
- I cannot delete a virtual wire interface in General Topics
- Interface Errors after upgrade - VM Series in Next-Generation Firewall Discussions
- Static route path monitoring using a destination within a different virtual router in Next-Generation Firewall Discussions




