- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Has anybody encountered a situation where a rule was configured for one application but matched other applications?
- LIVEcommunity
- Discussions
- General Topics
- Re: Has anybody encountered a situation where a rule was configured for one application but matched other applications?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Has anybody encountered a situation where a rule was configured for one application but matched other applications?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2014 04:17 AM
I have the following rule
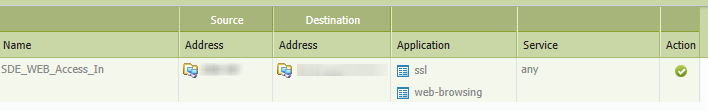
I used 'any' as the service because we have web servers running on multiple ports and not just on the default.
While it does match ssl and web-browsing traffic as expected, it also matches unexpected application traffic like the following
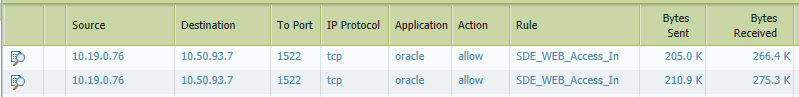
I don't understand why it would match oracle traffic. Any ideas?
- Labels:
-
App-ID
-
Troubleshooting
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2014 04:20 AM
Hi
It's because You put ANY as a service. Please put there app-default and oracle shouldnt hitted this rule.
Explanation is that oracle using probably SSL. Corect me if I'm wrong.
Regards
Slawek
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2014 04:26 AM
The reason we have any is we have a few dozen virtual web servers running on different ports so I was hoping not to enumerate every single port.... I guess I'll have to start typing then :smileygrin:
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2014 04:41 AM
Excuse me but this is a totally bogus explanation... so what if he put service any? The whole point of App-ID is to be port agnostic, that's how the product was sold to us. The replies above make no sense to me.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2014 04:44 AM
Hi Ericgearhart
If I'm wrong - please put here Your explanations.
So in your opinion its improperly identyfied aplication or so?
Regards
Slawek
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2014 04:49 AM
out of curiousity, would you mind checking if you have log "at start" enabled and if the logs you see hitting the wrong rule are start or end logs
PANgurus - Strata specialist; config reviews, policy optimization
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2014 04:50 AM
I must correct Slawek, if you put ANY to service, it's mean this application WITH any Port and not ANY application on any port. So you did it right.
The Problem what Slawek think, is the dependence in the Applications, if you put for example the application icq to the rule it will be automaticly allow the application ssl & web-browsing. But only if you don't have a deny any Rule at the end.
Back to your Problem with Oracle, with version do you have installed? PAN-OS and Application&Threats?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2014 05:18 AM
I only have 'log at session end' enabled
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2014 05:21 AM
PAN OS version 6.0.3 , Apps version 449-2321
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2014 05:26 AM
Incorrect sir...setting service to "ANY" will only allow for the traffic to traverse any port that still matches the specified application. Based off your logic, there would be no need to specify the application.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-14-2014 09:05 AM
I just put in another rule to match the oracle traffic on port 1522. The traffic doesn't get matched by my ssl/web-browsing rule anymore.
It still doesn't explain how a rule configured with an ssl or web-browser application could match oracle traffic.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-14-2014 09:51 PM
The behavior is quite odd. Usually, if there is application shift i.e application is first identified as web-browsing and later after the firewall has seen more packets, the same traffic gets identified as oracle, it should trigger a second policy look-up. Clearly this is not happening. If the issue is still persisting, i would suggest opening up a ticket with support.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-15-2014 01:41 AM
Hi FJU
You read from my mind ![]()
I thought that Palo_al has more security rules (below is more narrow rules especially for oracle application) but was curious why this traffic hitting this rule.
So Your explanation is correct.
I'm fighting with support with ammy-admin and backup-exec application aren't correctly identified by PAN OS. So maybe it's happened to You too.
Regards
Slawek
- 6381 Views
- 15 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Data Base application acees is slow through IPSEC Tunnel in Next-Generation Firewall Discussions
- Latency while using client application such as MS RSAT with GP VPN in GlobalProtect Discussions
- Diabled Application in VSYS1 in Next-Generation Firewall Discussions
- Restricting non work related downloads and applications in Next-Generation Firewall Discussions
- URL & Application level blocking possibilities in Cortex XDR. in Cortex XDR Discussions



