- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Help required to convert Cisco ASA NAT rule onto Palo Alto
- LIVEcommunity
- Discussions
- General Topics
- Re: Help required to convert Cisco ASA NAT rule onto Palo Alto
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Help required to convert Cisco ASA NAT rule onto Palo Alto
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2012 02:56 AM
Hi Guys,
I am not expert in reading or understanding the Cisco ASA NAT rules and I have just started to feel comfortable with Palo Alto except for NAT rules. Can someone please guide me through on how to go around configuring the following Cisco ASA NAT rule onto the Palo Alto?
I have just taken a couple of rules to convert. Based on this, I would get the rest done on my own.
Following are the CISCO ASA NAT RULEs:
Rule 1 # access-list inside_nat0_outbound extended permit ip 10.1.2.0 255.255.255.0 10.1.250.128 255.255.255.128
Rule 2 # access-list inside_nat0_outbound extended permit ip EH_Staff_Network 255.255.255.0 10.1.250.128 255.255.255.128
I know the exact rule cannot be expalined, but an overview on how to re-configure the above rules will be very helpful.
Many Thanks in Advance.
Regards,
Kal
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2012 10:39 AM
Hello Kal,
with my limited ASA knowledge I would say your sample code does not look like a NAT rule it looks like an ACL security rule.
This site might be a starting point for you to understand the cisco config:
http://www.tech21century.com/access-lists-and-nat-on-cisco-asa-firewalls-some-clarifications/
rgds Roland
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2012 11:07 AM
Look to me like that is the ACL that dictates what is allowed to be NAT'd outbound. The actuall NAT rule is setup with the command nat syntax below
xxxx(config)# nat ?
configure mode commands/options:
( Open parenthesis for the name of the network interface where the
hosts/network designated by the local IP address are accessed
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2012 05:03 AM
Thank you for the web link. Will look into it, find out more relevant stuff and then come back to you guys.
Cheers Guys.. Very Kind of you.
Regards,
Kal
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2012 05:36 AM
Kal just to let you know if you are not already aware of there is a migration tool.
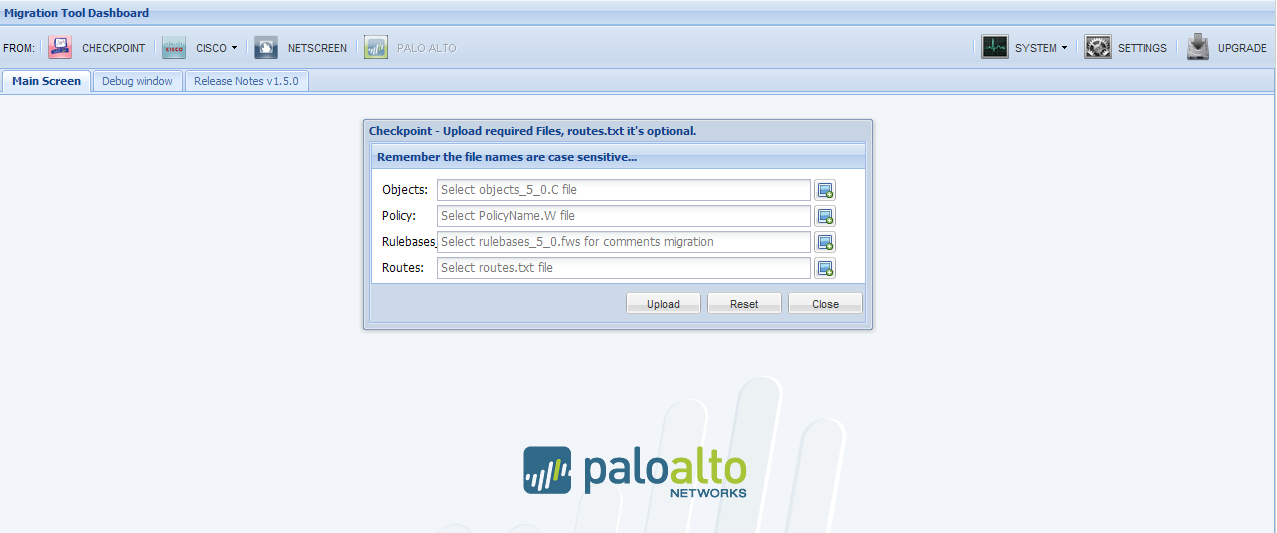
This tool can migrate a Cisco config to a PA config.
More info http://www.securlabs.net/
rgds Roland
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2012 05:44 AM
Roland,
I did know there was a migration tool and it does not convert the NAT rules is what I got to know. Secondly, I am not a CNSE qualified yet so might not have access to the tool is what I got to know. Am I correct? If not is there any way to get it sorted out?
Thank you
Kal
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2012 05:46 AM
Hi Kal,
everybody can use the migration tool just follow this link:
Yes you are right
Doesn't Convert VPN and Nat Rules
rgds Roland
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2012 09:00 AM
![]() that is exactly where i was stuck. Unfortunately, I do not feel very comfortable with configuring the NAT rules of PAN even though I understand them theoritically. Hence was asking for help.
that is exactly where i was stuck. Unfortunately, I do not feel very comfortable with configuring the NAT rules of PAN even though I understand them theoritically. Hence was asking for help.
Out of the cisco config, I could only find 3 these rules that state NAT: (do they make sense)
nat (inside) 0 access-list inside_nat0_outbound
nat (inside) 1 10.0.0.0 255.0.0.0
nat (dmz) 1 172.16.50.0 255.255.255.0
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2012 03:12 PM
Kalyanram,
Here you go...
nat (inside) 0 access-list inside_nat0_outbound
This statement is a no-nat rule. Traffic that arriving on the interface "inside" that matches the ACL "inside_nat0_outbound" is not natted.
nat (inside) 1 10.0.0.0 255.0.0.0
This statement does a hide nat for all traffic arriving on the interface "inside" that comes from 10.0.0.0/8. It will hide it behind the global nat address that corresponds to ID 1, and the correct outgoing interface.
nat (dmz) 1 172.16.50.0 255.255.255.0
This statement (you guessed it!) does a hide nat for all traffic arriving on your "dmz" interface that comes from 172.16.50.0/24. It nats behind the same global statements as the prior rule.
If you post (or PM me) the output of "show run | in global" and "show run | in static", I can explain the rest of the rules for you.
The nat rulebase in your PAN should do the same thing... one rule from inside to outside that does not nat (matching that ACL), and one that does nat (you can create a single rule that handles traffic from both your dmz and inside zones).
HTH,
James
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-24-2012 08:20 AM
James,
Thank you for the explanation. I will be going on site to do the migration for the customer. If any thing goes wrong in terms of NAT rules, I will post (or PM you). Thank you once again for your help.
Regards,
Kal
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-28-2012 11:31 AM
The www.securlabs.net website is not affiliated with, endorsed or supported by Palo Alto Networks. Use of the site is at your own discretion and risk.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-01-2012 05:45 AM
James,
This installation has been a disaster for me. Just could not understand how the Cisco ASA works in terms of VPN and NAT. Hence, i had to pull back and leave the network as it is. ![]()
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-01-2012 05:46 AM
Issues I had faced were:
a. We could access the Internet ONLY IF the Proxy settings were enabled on the web-browser ( The settings for proxy were; IP address set to 10.1.30.8 on port 8080). If the proxy settings were disabled, we COULD NOT access the Internet. This meant, all those who were using the proxy settings were able to browse to the internet and administrators who do not use the Proxy, but go through their Cisco ASA were unable to browse to the internet.
b. We were UNABLE to gain access to servers in DMZ ( FYI, on a couple of occasions, we could access the DMZ, strange..!!!).
c. We could NOT send emails, but COULD receive emails.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-01-2012 09:41 AM
I am sorry to hear that.
If you would like some assistance, you can contact me over PM.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-01-2012 10:01 AM
Have you tried working with your SE to iron out the rules? Ours has been more than helpful with all of our deployments.
- 8198 Views
- 16 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- A global protect connected client machine access a resource(behind Cisco router) that is connected to the host PA 800 Firewall via IPsec in GlobalProtect Discussions
- Start Network Security Basic to Advance || Firewalls Theory, Labs & Practical Project in General Topics
- IOC Upload through API - Security Level Advanced in Cortex XDR Discussions
- PANOS 10.x - share interface in Multi-vSYS mode in General Topics
- Convert from Cisco to Palo in General Topics



