- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
HOW TO Allow interface to access ethernet interface configured as Managment
- LIVEcommunity
- Discussions
- General Topics
- HOW TO Allow interface to access ethernet interface configured as Managment
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
HOW TO Allow interface to access ethernet interface configured as Managment
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2019 09:40 AM
We have a 2 system (firewall and RHEL7 server) configuration that has been set up to allow management access through ethernet1/11. What i am trying very unsuccessfully to do now is configure ethernet1/12 to be able to connect to the managment interface.
1/11 is set up to do DHCP so our laptops can connect for GUI use. I would like the RHEL7 server to be able to connect for cli access through second interface. I have the 11/1 configured with 192.168.0.2/28. Interfaces 1/11 and 1/12 are in a zone with only those two interfaces. The virtual router is configured with only these 2 interfaces.
I tried to set the 1/12 interface to 192.168.0.3, but that fails with overlapping subnets. I've tried setting up static routing with the 1/12 interface set to 192.168.1.0/28 but again it didn't work. Nothing i've tried has worked to allow the ssh connection from the server to reach the firewall interface (1/11) and log in.
Thanks for any help you all can give.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2019 02:50 PM - edited 12-30-2019 02:54 PM
Hello again.
You and I just discussed this last week, regarding DHCP and the Mgmt interface.
Have you configured and enabled an interface management profile on ether1/11?
I have a simple 2 port network, on a PA220 (well, technically 3, if you could count the mgmt interface)
My network is 172.17.13.0/24 with my management interface using IP of 172.17.13.253.
REGARDLESS of that piece of information.. My ethernet1/2 is the inside of my network, doing DHCP as well.
The Ethernet1/2 IP is 172.17.13.253/24. It acts as my DHCP server as well.
Anything plugged into my downstream switch can/could SSH into 172.17.13.254, because I enabled an interface management profile that allows SSH. This should 100% work.
So I do not understand why the RHEL server cannot simply SSH into your eth1/11.. why must it be connected to eth1/12?
Maybe you can help me to understand that, and then we can move forward.
I know I do not want to make it more complicated for you.. but it really sounds like what you need a 2 port vlan, with a VLAN interface that is doing the DHCP and allowing access to mgmt functionality.
eth1/11 ====\
|==> VLAN Interface, supporting DHCP, with interface mgmt profile allowing SSH.
eth1/12 ====/
Or you can create 2 separate networks 192.168.0.0/28 and then a different network (192.168.1.0/28) and have the virtual router do the routing between them.
What does your security policy show. Can you see traffic attempting to pass through the FW?
I am available for a phone call tomorrow (12/31) if you send me a message. This should have been resolved last week. 😛
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-31-2019 05:49 AM
Yes, i do appreciate the help. We have no switch and are looking to have the server able to connect to fw for cli access. I really didn't expect any issues after you helped with the DHCP and interface help. That worked perfectly and allowed laptop connectivity for GUI access. I have started the training that is available through Palo Alto to get a better understanding of the fw.
Ok, our setup is admittedly odd. 1 line in to the fw for network. Then the server off of that. No switch or other systems, the server is reachable through a KVM. I am looking to have the connection from the server to the fw be constant. and the laptop connection as needed. Hoping we can do most stuff via the CLI and only use the GUI for more involved issues.
I have tried 2 separate networks, but if that should have worked i did not do it correctly. I will re-try the VLAN answer since that seemed to be a workable solution i just didn't get it working.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-01-2020 08:46 AM
You need to configure the mgmt profile which allows ssh and bind that profile to the respective interface.
Sahithyan S
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-09-2020 07:37 AM
Sorry about the delay getting back to my thread, got re-tasked for a bit. What i ended up doing to get the systems up was enabling both ethernet1/11 and ethernet1/12 as Management ports. So the DHCP and Management on 1/11 will be for our laptop connection with GUI or CLI access. The 1/12 has Management profile with static IP reachable from the RHEL server for regular access via SSH to CLI.
Any major pitfalls/problems with doing it this way.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-09-2020 09:29 AM
Basically.. you are somewhat good.
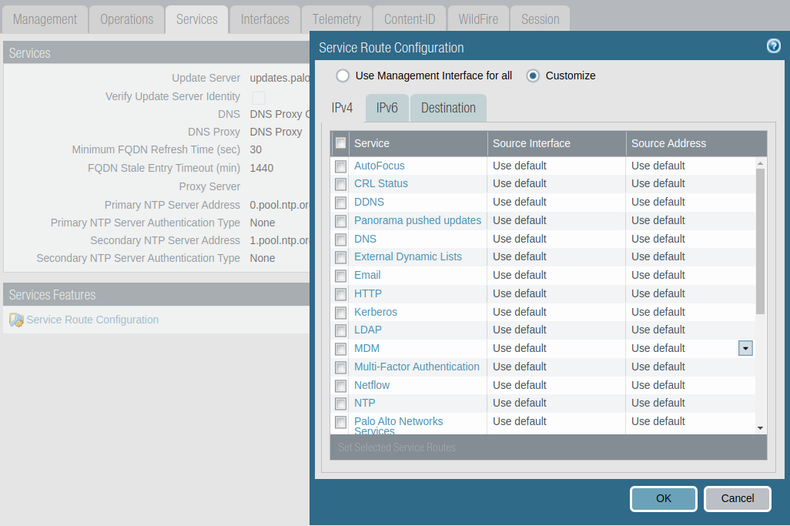
Now the mgmt port itself (not /11 or /12) has about 20 services (NTP, Panorama, DNS, Wildfire, etc)
What public facing interface on the FW is going outbound to get updates, such as NTP, DNS, WF, etc, etc?)
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-09-2020 10:28 AM - edited 01-09-2020 10:29 AM
1/1 is the incoming connection.
- 10348 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PA 445 setup in Next-Generation Firewall Discussions
- Setting static Management interface IP in Azure VM NGFW in General Topics
- Is DoS Protection Detection Possible in TAP Mode? in General Topics
- Continuous Threat Logs Showing Management Server IP as Source in Next-Generation Firewall Discussions
- How do I change a configuration given by a Strata Cloud Manager snippet in an NGFW? in Strata Cloud Manager