- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Inbound SSL decryption in vWire and Tap mode
- LIVEcommunity
- Discussions
- General Topics
- Re: Inbound SSL decryption in vWire and Tap mode
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Inbound SSL decryption in vWire and Tap mode
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-17-2012 04:28 PM
Short question:
Is inbound SSL decryption possible in vWire and/or Tap mode?
Regards,
Andreas
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-17-2012 04:39 PM
Hi James,
thanks for the quick reply.
I have outbound decryption working fine in vWire.
I didn't expect to get outbound decryption working in tap mode but I was hoping that it should work for inbound.
Need to debug then a bit more to get it working.
Regards,
Andreas
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-18-2012 03:20 PM
Good Luck!
Let us know if you need any further help
Best Regards
James
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-19-2012 06:19 PM
Looks like I need some additional help:
Let me first briefly describe my setup:
Internet - PAN vWire - SSG5 - SA2000
There is an incoming NAT rule forwarding traffic to port 443 directed to the SSG5 to the SA2000
I'd like to control the incoming traffic to the SA2000.
The SA 2000 is used for SSL VPN (Network Connect) and Activesync from mobile devices.
I loaded the certificate of the SA2000 to the PAN and started to decrypt inbound SSL traffic.
Originally I allowed only ssl and activesync to the SSG5. This didn't work.
When I checked the logs I saw that there was incoming web-browsing blocked to port 443
Looks like PAN first detects incoming SSL, next it sees the traffic as web-browsing and next as activesync.
My policy on the PAN has application default for the incoming services.
web-browsing on port 443 is blocked in this case.
I ended up adding an additional rule allowing web-browsing to port 443
After that activesync and network connect worked
But this is not what I want.
I'd like to allow only activesync and network connect (looks like there is no appID for Juniper Network Connect BTW)
Allowing web-browsing to port 443 leaves the door wide open for any sort of attacks.
Second question concerning outbound SSL decryption:
When I commit my config I get a warning that there is no untrust cert configured and therefore the trust cert will be used.
Any hint how to generate and load an untrusted cert to be used for outbound SSL decryption?
Regards,
Andreas
PS: I know that I probably could replace the SSG5 and SA2000 with the PAN but curently I'm missing the support for dynamic DNS.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-19-2012 11:54 PM
Hello Andreas,
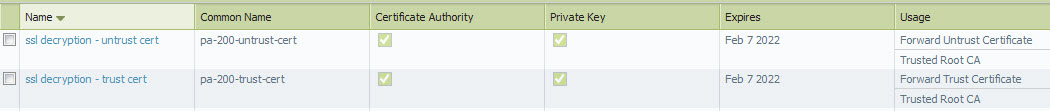
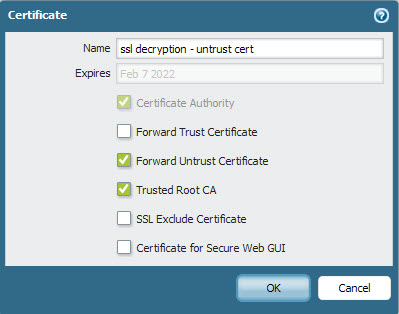
regarding the outbound SSL decr. cert. Optionally you can generate an untrust-cert like below
For the inbound SSL part I always recommend not to use APP-ID exclusively. From a security perspective this can be a bit problematic, because PA needs to pass a certain amount of traffic before it can decide on an APP-ID. This leaves a kind of an exposure.Therefore it is adviseable to use at least a service port together with an APP-ID for inbound traffic.
But this is not what I want.
I'd like to allow only activesync and network connect (looks like there is no appID for Juniper Network Connect BTW)
Allowing web-browsing to port 443 leaves the door wide open for any sort of attacks.
Since you terminate SSL on the PA Firewall you can use Threat Prevention to further protect your environment for inbound traffic.
rgds Roland
- 5706 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Reverse proxy for Exchange ActiveSync in General Topics
- Questions about the decryption performance of pa-5200 series in Next-Generation Firewall Discussions
- Demystifying the SSL Decryption on Palo Alto Firewall in Next-Generation Firewall Discussions
- Migration from HA pair PA-3220 running PanOS 9.1.16 to HA pair of PA-1420 running 11.0.2 in General Topics
- Issues fixed as recommended by AIOPS Premium console are still being reported negatively in AIOps for NGFW Discussions



