- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
IPSec VPN tunnel no longer working
- LIVEcommunity
- Discussions
- General Topics
- IPSec VPN tunnel no longer working
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-05-2012 09:47 AM
Hello guys
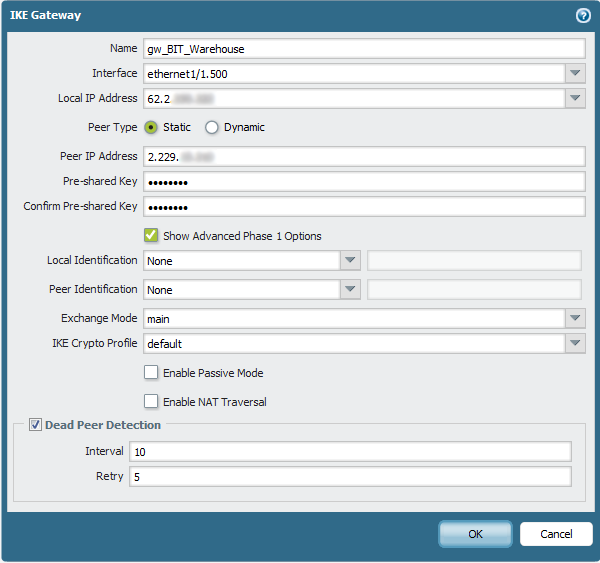
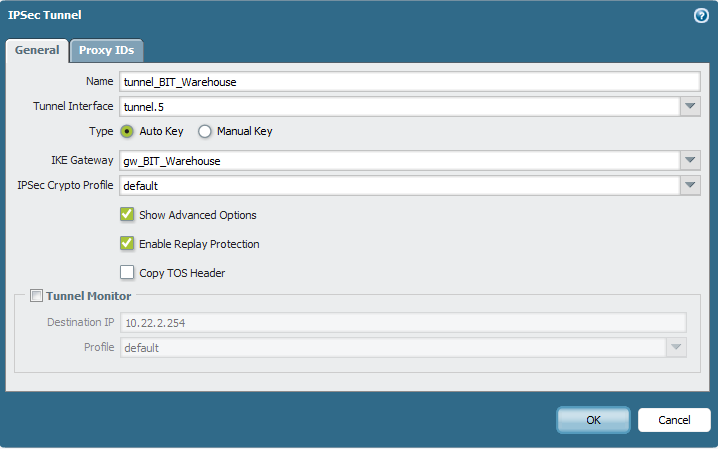
We have a few VPN tunnels between our PA-2050 (in HA cluster) and some WatchGuard firewalls (different models). We migrated these tunnels to the PA-2050 a few weeks ago and they ran stable. Now suddenly two of 10 tunnels are down and we don't get them back up.
Here's what we tried so far:
- Rebooting the WatchGuard firewalls
- Suspending the active PA-2050 so the standby HA device takes over
- Removing the VPN config on the WatchGuards and rebuild them (only VPN part)
- Overwrite the PSK on both ends
- On the PA-2050 CLI: clear vpn ike-sa gateway <gw-name> and clear vpn ipsec-sa tunnel <tunnel-name>
- some more small stuff
The config is the same on all tunnels, including the two not working...
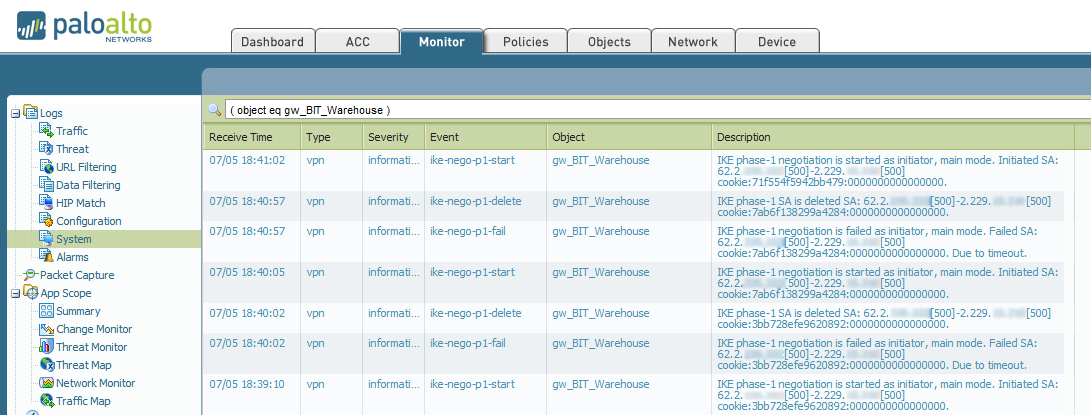
Any inputs would on how we can further troubleshoot the issue would be much appreciated. The connection by the way is working. We can ping the endpoints mutually and we can also access the external admin interface of the remote WatchGuard firewalls...
Thanks!
Oliver
- Labels:
-
Networking
-
Troubleshooting
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-09-2012 01:00 AM
Thank you for that oschuler will try it next time
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-10-2012 11:11 PM
Looks like the latest release (version 318) contains modifications on the 'ike' decoder. We'll install it on Sunday, hopefully the issues are gone with it...
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-11-2012 02:59 AM
OK our VPN is lasting for 28 hours with an 8 hour lifetime.
Having just got it back, it would appear that the UDP packets are not being correctly identified as IKE and being dropped at the firewall. I am guessing this is on a re-negotiation of the link. I just looked for 318 and there was no sign of it so I will keep an eye on it being available
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-12-2012 06:53 AM
I haven't had an issue since reverting back to 4.1.4. Perhaps there was just an issue with the install...
When 4.1.7 is released I'll try that along with the 318 content.
-J
- 20218 Views
- 18 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- return traffic being dropped, not being sent through the vpn tunnel in General Topics
- IPSEC to Azure establish but cannot use traceroute in General Topics
- GlobalProtect 6.1.11-175 Connection Issues in GlobalProtect Discussions
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics
- Azure to OnPrem Connectivity issue in Next-Generation Firewall Discussions




