- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Nest Thermostat
- LIVEcommunity
- Discussions
- General Topics
- Nest Thermostat
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Nest Thermostat
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-21-2016 02:18 PM
Anyone running a Nest Thermostat behind a Palo Alto Networks firewall? I am seeing an inability to connect to the nest site. Logs show a repating SSL on 443 with session end reason: tcp-rst-from-client
Any thoughts would be appreciated.
Bob
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-21-2016 02:25 PM
I've got a pair of Nests at my house behind a PA-200. Almost all the connections end up with a client reset, but everything works for my Nest reporting and login. My phone can manage them just fine, and I can see all my historical data. I think that Nest is just really aggressive with TCP handling.
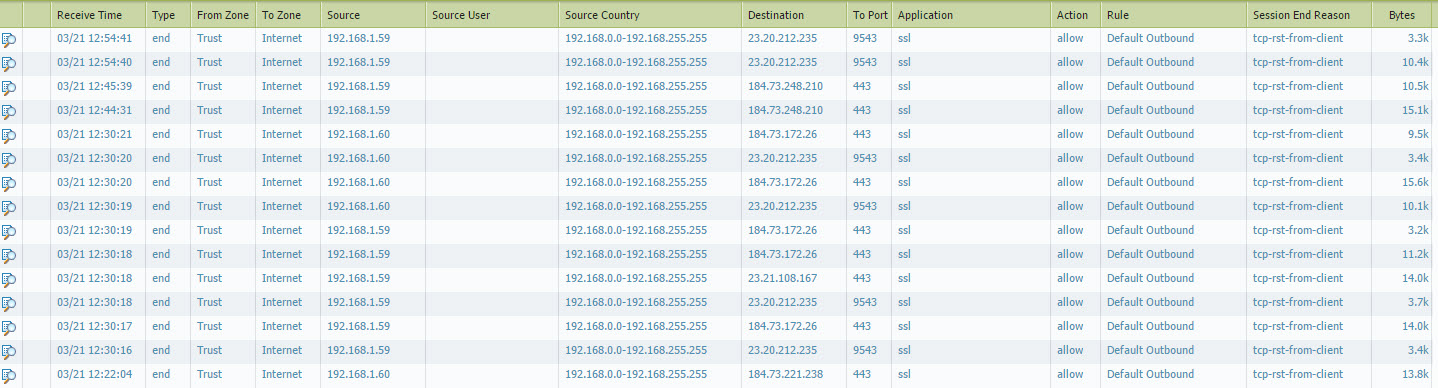
Here's a screenshot of my logs. You'll notice that everything ends with rst, but the byte sizes are significant:
Hope this helps,
Greg
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-21-2016 02:32 PM
Thanks for the prompt reply.
I have very similar logs. Problem is it is always offline and can not be controlled. As soon as I remove the PA-200 and switch to an old school wireless router it works fine.
Any thoughts on what settings to tweak, what to look for to try and figure it out? etc.
Thanks
Bob
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-21-2016 02:39 PM
I haven't had any issues with it connecting and being controlled. Are you doing NAT on your firewall for the Nest device? That's the only thing I can think of, as it doesn't need any inbound rules and your security rules are probably good.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-03-2018 06:57 PM
Any update on this? I am troubleshooting Nest cameras and thermostat with the same symptoms.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-05-2018 12:16 PM
My solution was to throw up another AP/router with a different SSID for the Nest as well as the PS4 and other UPNP devices. That assumes your ISP gives you more than a single external IP.
Hope that helps,
Bob
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-06-2018 12:07 PM
I'm running a nest thermostat (v3) at home behind a PA-200 and haven't run into any issues or had to configure anything differently. Have you chedked the unified log to make sure any other traffic required may not be being blocked?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-15-2018 08:09 AM
The problem the Nest is having (or at least mine was having), is that it is trying to use the dropcam app on a non-default port (tcp-9543). if you're using policies that use application-default to allow your nest traffic out, it won't work.
Add a rule that allows dropcam (& web-browsing) outbound using tcp-9543 (along with your regular app-default outbound rules) and you should be golden.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-09-2018 09:08 AM
I just noticed our Nest thermostats are using tcp/9543 and are being ID'd as dropcam as well. Seems like a bad app-ID.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2020 09:11 AM
Hello,
Its 2020 and i also had the same issues of all 8 of my nest protects and 2 cameras disconnect from the nest services. They were still on my wifi networks, i could see the dns requests hitting the firewall and a single http request, but that http request never got a response from the nest cloud. I figured out that my firewall had a bad entry in its dns cache for the nest cloud. Once i disabled the dns cache option on the firewall everything came back to life. Just thought i would post the solution here. Thanks, michael
- 9825 Views
- 9 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Cortex XQL "Let" replacement in Cortex XDR Discussions
- Palo Alto EDLP Nested Data Profile Incident shows incorrect count of occurances in Enterprise Data Loss Prevention Discussions
- is there is a limit to nested app groups? (how many nested groups can be inside each other) in Next-Generation Firewall Discussions
- Nested plist capable for Mac GlobalProtect? in GlobalProtect Discussions
- Split nested JSON in Cortex XDR Discussions