- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
PA Traffic is logged under different users other than the logged in user
- LIVEcommunity
- Discussions
- General Topics
- Re: PA Traffic is logged under different users other than the logged in user
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
PA Traffic is logged under different users other than the logged in user
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-21-2017 08:56 PM
Hi guys,
We have a security rule that grant a certain app access to users based on AD group.
User complained that sometime they can access the app and sometime they cant.
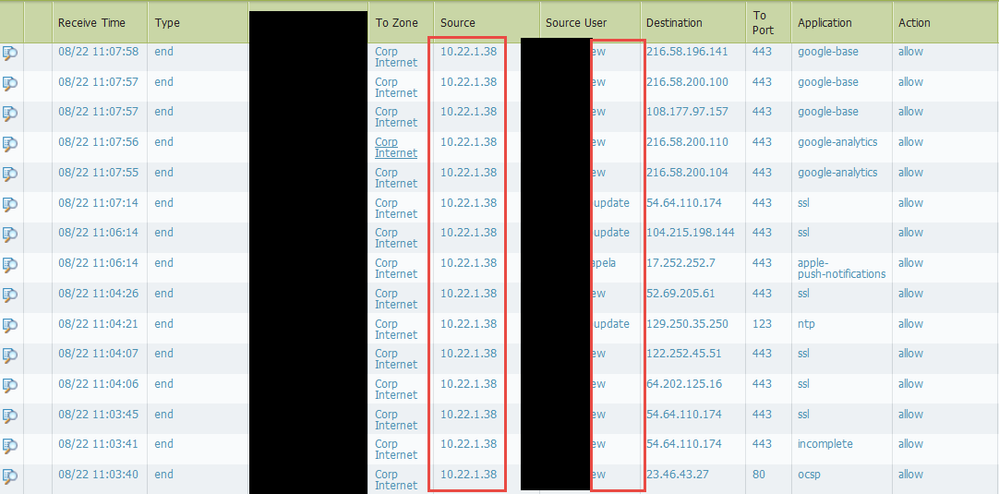
Checked the firewall and found out that some of the traffics are logged under different user accounts, hence the right policy didnt get applied.
User is using OSX (mac) and has more than 2 exchange mailboxes connected to the outlook profile.
Is there a way to control this?
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2017 12:03 AM
how is user-ID being performed?
is the second account a shared one that should not have individual access, you could add it to the user-ID ignore user list
PANgurus - Strata specialist; config reviews, policy optimization
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2017 01:21 AM
does user part of AD group, if not captive portal will be an option
Firewalldog dot com
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2017 01:22 AM
does the username show the same AD domain name or different
Firewalldog dot com
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2017 02:16 AM - edited 08-23-2017 02:17 AM
Hi Esutedy,
In this situation it may be better to remove the exchange servers from user-id monitoring but I don't know enough about how your user-id and environment set-up to see if that would be the best solution.
As always, I find the best way of doing user-id is using GlobalProtect. Not for the VPN side of it but for internal host detection as this will always identify the correct user and authenticated to the internal gateway on the firewall.
hope this helps,
Ben
- 2567 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Problem with viewing and downloading 30-day logs on Panorama server in Panorama Discussions
- NAT mapping public to private IP in General Topics
- Need clarification on URL Filtering logs in Next-Generation Firewall Discussions
- After Endpoint Traffic Policy Enforcement, client can not be access microsoft login portal for smal auth. in GlobalProtect Discussions
- Monitor Logs - filtering with wildcard? in General Topics