- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Palo Alto RADIUS authentication against Microsoft NPS is broken
- LIVEcommunity
- Discussions
- General Topics
- Re: Palo Alto RADIUS authentication against Microsoft NPS is broken
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 12:19 AM
Has anyone managed to get authentication on PAN-OS 7.0 working with microsoft NPS servers?
Since version 7.0 authentication against our microsoft NPS radius servers is broken. Because the firewall now always first tries CHAP instead op PAP (see this article) and microsoft NPS always replies with a ACCESS-REJECT massage (see this article -> item 9).
As it's insane to start storing our AD credentials with reversible encryption I guess microsoft NPS isn't compatible anymore with Palo Alto? Or am I missing something here?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 06:42 AM
Recreating the RADIUS server profile did the trick. (actually, changed the timeout and retry from 3 to 2 and pushed from panorama). The system log now says it switched to PAP for that radius server.
That's a nasty bug... Never would have tought 'touching' the radius config could fix the issue...
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 01:35 AM
I have configure radius authentication with NPS and it works perfect. I am using 7.0.2
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 01:44 AM
What are the settings of your policy? I've enable only PAP as an allowed authentication method.
I can't figure out how to trigger the PAP failover on palo alto. It keeps on using CHAP which isn't supported on our domain.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 02:05 AM
Oh, so you are running the windows 2012 version of NPS?
We're running it on 2008 R2. It might be there's a behaviour change between the 2 windows versions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 03:51 AM
Are you using the NPS for administrator or GlobalProtect access?
What version of PAN-OS?
What does the Event Viewer on the NPS say? Event Viewer -> Server Roles -> Network Policy Server
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 04:33 AM
We're using it for admin access on PAN-OS 7.0.2.
NPS logs give an error (19): No reversibly encrypted password is stored for the user account. This means you should enable reversible encryption on you domain controllers with the policy setting "Store password using reversible encryption for all users in the domain" which is not something we can do.
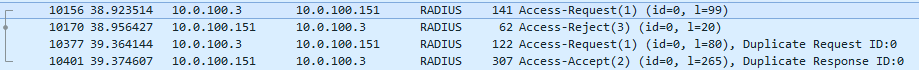
Packet captures show only 1 request and an ACCESS-REJECT radius reply from NPS (because of the CHAP). So no second attempt by the firewall.using PAP
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 04:52 AM
Is the Network Policy (or Connection Request Policy, if using overrides), specifically configured to only allow PAP?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 04:59 AM
Yes, The NPS settings are exactly the same as on your screenshot. I also see you're running windows server 2012.
Maybe 2012 does not reply on CHAP requests triggering a timeout, while 2008 replies with an access-reject?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 06:02 AM
All versions of NPS (2008 <-> 2012 R2) should behave the same way.
Dump below is from a 2012 R2. First a CHAP request is sent, that is rejected, and then PAP is tried.
The Event Viewer will also indicate two logins. Subsequent logins are only sent using PAP though.
Might be worth a shot to re-create the RADIUS server profile on the firewall.
What does a Wireshark trace from the NPS look like?
The whole CHAP implementation in 7.0 is pretty silly. The failover only works half the time for the inital logins, it causes massive issues with Multi Factor Authentication solutions using RADIUS Challenge/Response, there's no tickbox to turn it off and completely baffling that CHAP, instead of MS-CHAPv2 is supported..
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2015 06:42 AM
Recreating the RADIUS server profile did the trick. (actually, changed the timeout and retry from 3 to 2 and pushed from panorama). The system log now says it switched to PAP for that radius server.
That's a nasty bug... Never would have tought 'touching' the radius config could fix the issue...
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-19-2015 07:27 AM - edited 10-19-2015 07:27 AM
Found this issue on another firewall (Panorama 7.0.2) - I could also resolve it by modifying the RADIUS configuration. Great find!
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-22-2015 10:17 PM
Woop woop.. From the PAN-OS 7.0.4 release notes:
Added a new CLI operational command ( set authentication radius-auth-type <auto|chap|pap> ) to address an incompatibility issue between PAN-OS and some RADIUS servers. With this fix, you can manually override the automatic selection mechanism introduced with Challenge-Handshake Authentication Protocol (CHAP) support in PAN-OS 7.0 to select either CHAP or Password Authentication Protocol (PAP) as needed.
TLDR; CLI command set authentication radius-auth-type <auto|chap|pap>
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-24-2015 05:29 PM
Thank you. But, it looks like it can be done only via CLI, how about configuring CHAP from GUI?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-24-2015 05:37 PM
Well, even from the CLI, it doesn't seem to take the command.
rbista@MyFirewall> configure
Entering configuration mode
[edit]
rbista@MyFirewall# set authentication radius-auth-type chap
Invalid syntax.
[edit]
rbista@MyFirewall#
Any suggestions? I ran the command # find command keyword "radius-auth-type", it display the command though.
rbista@MyFirewall> find command keyword "radius-auth-type"
set authentication radius-auth-type <auto|chap|pap>
rbista@MyFirewall>
- 1 accepted solution
- 20310 Views
- 16 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Ownership Dispute Involving Palo Alto Hardware in General Topics
- GlobalProtect MFA with external/USB user certificate in GlobalProtect Discussions
- GP with saml authentication always redirects to idp in General Topics
- StoreDesktopExtension.exe - Again alerts are generated in Cortex XDR Discussions
- Global Protect is having issues with newer MACOS version. in Next-Generation Firewall Discussions