- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
PAN-DB URL Version Remains 0000.00.00.000
- LIVEcommunity
- Discussions
- General Topics
- PAN-DB URL Version Remains 0000.00.00.000
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
PAN-DB URL Version Remains 0000.00.00.000
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-24-2020 11:05 AM
The firewall is running 9.1.4 (5250). The mgmt interface does not have general internet access so service routes have been configured for the following to use the external interface (internet connected):
DNS
EDL
NTP
Palo Alto Networks Services
URL Updates
Policy is created to allow outbound traffic to the internet sourced from the external IP (NAT in place as well).
NTP is working
NTP state:
NTP synched to 1.us.pool.ntp.org
NTP server: 0.us.pool.ntp.org
status: available
reachable: yes
authentication-type: none
NTP server: 1.us.pool.ntp.org
status: synched
reachable: yes
authentication-type: none
Support check is good
Contact Us
https://www.paloaltonetworks.com/company/contact-us.html
Support Home
https://www.paloaltonetworks.com/support/tabs/overview.html
Manage Cases
https://support.paloaltonetworks.com/pa-portal/index.php?option=com_pan&task=viewcases&Itemid=100
Click the contact link at right.
May 30, 2021
Premium
24 x 7 phone support; advanced replacement hardware service
but URL DB is not being updated
PAN-DB URL Filtering
License : valid
Cloud connection : not connected
URL database version - device : 0000.00.00.000
URL protocol version - device : pan/0.0.2
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-24-2020 02:28 PM
Hi @jlieberman ,
You need to download the initial seed file for the PAN-DB.I believe you are missing the second step from this document
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClIdCAK
When URL filtering is enabled firewall will evaluate the URL that is passing through it, as you can imagine the are so many urls that FW cannot store information for all of them. That is why it will contact Palo Alto cloud and ask for evaluation, when reply is received the firewall will cache it and if it needs to check the category for the same url it will use the cached value instead of asking the cloud again (saving time and resources). The initial seed file is basically pre-build cache file with most visited address for given region. So in order to enable the engine it needs to have this initial cache file. As mentioned the seed file contains of trending address for given region, and Palo Alto is updating this information periodically, that is why fw will periodically download newer version of this file.
It is recommended to select the relevant region for which your firewall is located, this will ensure that more of the urls that you need to evaluate are already in the cache
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-24-2020 04:40 PM
@A_Astardzhiev Thank you for the prompt reply but that seed file is a thing of the past and no longer used in PANOS 9.0 and later.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-24-2020 04:43 PM
@A_Astardzhiev as can be seen at https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PNx4CAG
Additional Information
The below commands do not work on OS 9.0.x but will work on prior OS versions and will fix the Pan-DB 0000.00.00.000 issue:
> request url-filtering download paloaltonetworks region <region_name>
> request url-filtering download status vendor paloaltonetworks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-24-2020 11:28 PM
Thanks @jlieberman ,
I was not aware of this change, I will have it in mind.
The only other reason I have experience is if the firewall is in active-passive HA and the secondary member is not able to connect to the cloud via the service route as it doesn't have running routing engine.
Have you tried to confirm to run some captures to confirm bi-directional connectivity to the cloud?
First check with capture that you see DNS requests and replies. Based on the DNS reply run capture with returned cloud ip and check what traffic is generated. Most probably it will be SSL but at least you can confirm that you have basic TCP connectivity.
- Mark as New
- Subscribe to RSS Feed
- Permalink
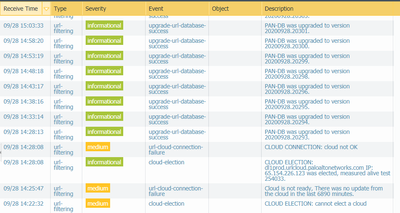
09-28-2020 05:16 PM
I've no idea why, but it seems that my URL-filtering DB started working today.
- 9498 Views
- 5 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- DHCP vulnerability error false postive content version 9104-10068 in General Topics
- how to erase this "Warning Expired Certificate Check" PA-1410 version 12.1.6 in General Topics
- Active Passive Failover in AWS in VM-Series in the Public Cloud
- [FIREWALL] - Commit Issue in Next-Generation Firewall Discussions
- OSPF process crashes after manual HA Failover in Next-Generation Firewall Discussions