- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Panorama traffic invisible
- LIVEcommunity
- Discussions
- General Topics
- Panorama traffic invisible
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2017 12:19 PM
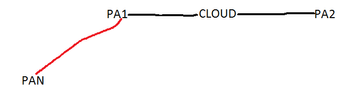
PAN(VM) and PA1 management interfaces are both Zone A.
PA1 connects to PA2(remote site) on IPSEC tunnel. Traffic from PA2 on PA1 is considered in Zone A and viceversa on PA2 for traffic from PA1.
If i do packet capture on either PA, I can see there is bidirectional traffic between PA2 and PAN. But traffic logs don't show anything, I may select any PAN/PA as source or destination.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2017 11:19 PM
Is the session visible in the session table?
The connection from a firewall back to panorama is a permanent ssl session
Because it is permanently up, it will not show up in the logs until it is terminated (it is 1 connection for an 'unlinited' amount of time, rather than a bunch of ssl sessions oer time) because logs are generated when a session ends (log at end)
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2017 12:31 PM - edited 10-05-2017 12:32 PM
Not sure if l fully understood your question, but for the traffic visibility on VM you must have an active licenses, otherwise no traffic will be shown in the monitor tab.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2017 12:44 PM
We have License for that. We manage both firewalls through Panorama and also push logs to it.
As both the management interface for PA1 and PAN are in same zone, I do not see traffic for it as it doesnot has to cross firewall. But for the remote site PA2 which is also managed by Panorama (location same as PA1), traffic has to pass though tunnel to PA2's management interface. This traffic should be vissible at both PA1 and PA2, which is not.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2017 08:24 PM
Traffic inside same zone will match to intrazone-default rule that does not log traffic by default.
Choose intrazone-default rule and click override.
Then you can edit rule settings to enable log at session end.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2017 11:19 PM
Is the session visible in the session table?
The connection from a firewall back to panorama is a permanent ssl session
Because it is permanently up, it will not show up in the logs until it is terminated (it is 1 connection for an 'unlinited' amount of time, rather than a bunch of ssl sessions oer time) because logs are generated when a session ends (log at end)
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-06-2017 09:04 AM
So what is the recomended log setting. As malacious traffic session if is able to stay up for long we would not see it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-06-2017 09:12 AM
This is only a unique issue with panorama 'call home' connections, this does not normally apply to regular traffic
If a threat is detected the threat will be logged and if the session is terminated becauer of the threat (in case threat action is reset or drop for example) that will be logged too
PANgurus - Strata & Prisma Access specialist
- 1 accepted solution
- 5326 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Cloud NGFW: Mandatory Panorama Upgrade to 11.2.7-h4 or higher for managing Cloud NGFW Firewalls. in General Topics
- Firwall is uable to send logs to the Panorma (Log collector is showing inactive) in Next-Generation Firewall Discussions
- Panorama reports not available since the upgrade in Panorama Discussions
- Log Collector Redundancy in Panorama Discussions
- Newsletter: Cloud Delivered Security Services, Oct-2025 in Advanced Threat Prevention Discussions