- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Pruning weak key exchange algo in Pan OS 8.19
- LIVEcommunity
- Discussions
- General Topics
- Pruning weak key exchange algo in Pan OS 8.19
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2021 07:48 AM
In Palo Alto v8.19, they added functionality to prune multiple weak key exchange algo in one line: (https://docs.paloaltonetworks.com/pan-os/8-1/pan-os-release-notes/pan-os-8-1-addressed-issues/pan-os...)
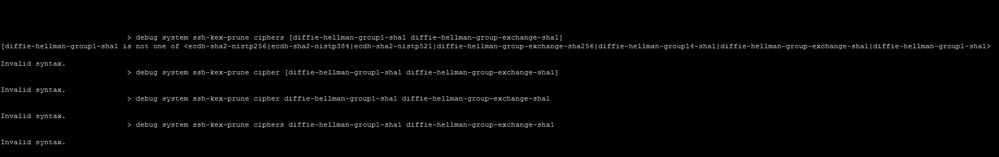
I followed the guide here (https://docs.paloaltonetworks.com/pan-os/8-1/pan-os-cli-quick-start/get-started-with-the-cli/refresh...) and tried to prune 2 ciphers in one line but it gives me the error "invalid". I can't prune them one by one as the guide says it won't work that way, but I am able to prune them one by one but just not 2 or more together even following the guide.
Does anyone know what is the correct syntax or what is the issue ?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-15-2021 09:59 AM
Need a space between the first "[" and the cipher.
"debug system ssh-kex-prune ciphers [ diffie-hellman-group1-sha1 diffie-hellman-group-exchange-sha1 ]" is successful.
Hope this helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-10-2021 02:33 PM
Can you provide a picture of the error and did you test with the example command from the article by copy and paste it, to check if it works atleast from the example from https://docs.paloaltonetworks.com/pan-os/8-1/pan-os-cli-quick-start/get-started-with-the-cli/refresh... ?
It could be a new bug as this feature is so new (added to the latest release) and if copy and paste from the aticle you still have issues, then better contact the TAC as 8.1.19 is the latest release and there are no releases to have solved this.
"debug system ssh-kex-prune cipher [diffie-hellman-group1-sha1 diffie-hellman-group-exchange-sha1]"
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-10-2021 07:37 PM
Yes we tried all kinds of combinations, without [] ,with [] as in the article.
We bought PA support through another vendor and they had already contacted PA TAC about it but PA TAC is taking a long time to reply so I was wondering if anyone is able to successfully run the command if they have a lab or so to try too.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-15-2021 09:59 AM
Need a space between the first "[" and the cipher.
"debug system ssh-kex-prune ciphers [ diffie-hellman-group1-sha1 diffie-hellman-group-exchange-sha1 ]" is successful.
Hope this helps.
- 1 accepted solution
- 3380 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!