- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Queries for DUAL ISP link
- LIVEcommunity
- Discussions
- General Topics
- Queries for DUAL ISP link
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Queries for DUAL ISP link
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-08-2019 08:56 AM
I am following this KB link to set this up https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClFiCAK
1/ So the documents says i have to setup 2 source NATs for each interface. Can we getaway by using the interface as ANY in NAT rule? What is the best practice?
2/ What about destination interface for the traffic coming to our hosted web-servers, Should there also be 2 destination NAT's? ISP will be re-routing/advertising our subnet on the faild-over link for traffic destined to us.
3/ What happens to HA, we have firewalls in Active-Passive, with path-monitoring profiles enabled on them. Should we disable path monitoring with dual links?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-08-2019 06:48 PM
If you are definitely trying to use Dual ISP with automatic VPN failover, I would follow the KB article exactly.
As for the NAT rules, you definitely need to definite ingress interfaces vs using ANY.
You should probably be using loopback IPs that are available on both ISPs, so that if 1 ISP fails, the 2nd ISP will still know about the 2nd loopback address and inbound/destination NAT can still work (need to test thoroughly)
As for path monitoring, yes... i would agreed to turn it off from the HA config, but you need to ensure path monitoring is configured in your virtual router. This way, if the VR determines the 1st ISP is down, then it can remove the route from the FIB table, and send traffic to the ISP, using the 2 NAT rule. This is why you MUST define, in your NAT, what addressed is to be used, based on the interface, to ensure the correct NAT statement/IP is used.
More questions? 😛
let us know.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2019 08:09 AM
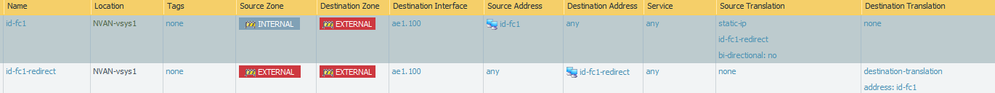
@S.Cantwell Thanks for the answers. For us ISP providing L2/L3 still remains the same, its only physical link that goes to two different ISP's so that is not an issue. So I would be duplicating both the below NAT rules as an example with each destination interface, correct?
- 3284 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!