- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
recommendation when putting the Palo Alto in a vwire mode.
- LIVEcommunity
- Discussions
- General Topics
- recommendation when putting the Palo Alto in a vwire mode.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
recommendation when putting the Palo Alto in a vwire mode.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2018 06:55 AM
Folks,
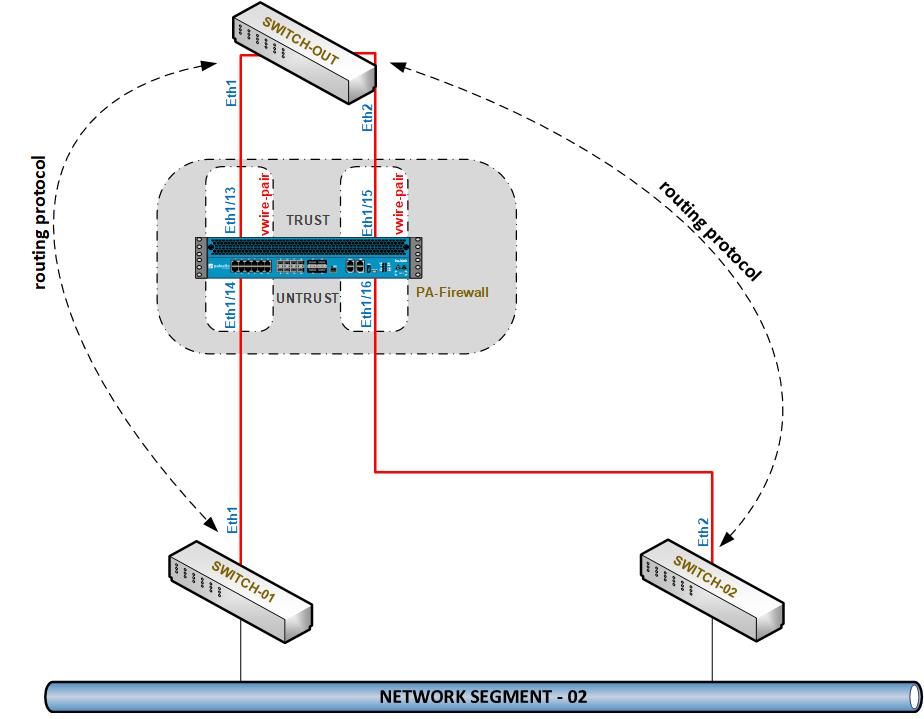
we have a switch to switch routing protocol running and the requirement is to put a palo alto in a vwire mode on such an environent. Please see the file attached with tis post.
Now, the catch to this is the "switch-out" forms neighbours with "switch-01" and "switch-02" and packets going inside one link could come out of the other. I just wanted to ensure that this will not cause any packets drops as long as the zones are correctly configured.
also, from a very high level what configuration would be needed? Convert each interface to a vwire? add the zones? add the policies? anything else?
Thanks!!!
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2018 09:07 AM
Does it have to be virtual wire?
What if you configure those 4 Palo interfaces in Layer 2 mode.
Set Ethernet 1 and 3 into one Aggregate Group.
Set Ethernet 4 and 6 into second Aggregate Group.
In this case all packets from same communication are correctly matched into correct session in Palo.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2018 09:28 AM
thanks for the comments mate!!
Yes, it has to be virtual wire becuase we do not want to disturb anything in the existing setup. There is already routing protocols running between the switches and we want to retain that.
The firewall should maintain the state table from one zone to the other, right?
if yes, this should work without any challenges from what I think.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2018 10:03 AM
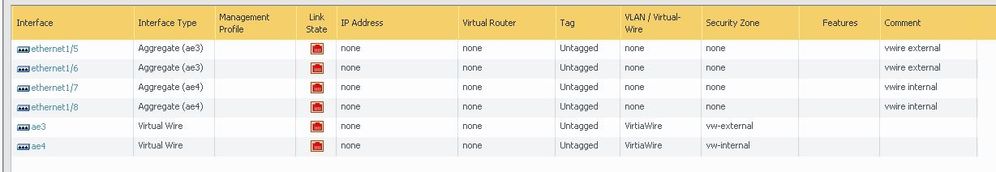
Hey I checked and virtual wire allows multiple interfaces in it also using aggregates.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2018 11:19 AM - edited 10-25-2018 11:24 AM
yes, I agree. But in my case the switches are on a single interface. There is no point using the aggregate interfaces. 🙂
aggregate interface would be needed if they are also connected to the same switch ...right?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2018 11:22 AM
It is not about switch. It is for Palo so that all packets both ways would be combined together into single virtual wire in Palo standpoint so it could correctly perform AppID and threat prevention.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-26-2018 01:11 AM
ok, understood. However, do you see a potential issue that could occur in the ealier design?
The firewall should still be able to keep session information if the packet comes inside over one path and goes out via the other, right?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-26-2018 11:34 AM
When you create Aggregate Ethernet Interface in Palo you leave LACP disabled so switches are not aware that this traffic is merged in firewall.
How should firewall otherwise merge packets passing over different interfaces together into same session?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-26-2018 11:42 AM
Gave this another thought and you would need to test how traffic exits from vw. Might not exit from interface you need.
Do you have single firewall or HA pair.
If HA pair then maybe it can be designed using A/A setup.
Palo Alto Networks certified from 2011
- 7403 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!