- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Restricting Global protect VPN access to specific countries
- LIVEcommunity
- Discussions
- General Topics
- Restricting Global protect VPN access to specific countries
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-19-2018 08:38 AM
How to configure Global Protect vpn users to access from only specific countries ?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-19-2018 09:25 AM
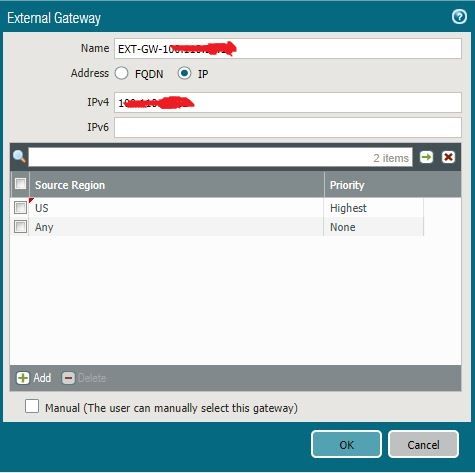
also... in version 8.something you can offer gateways dependant on what country the user is connecting from...
network/portal/agent/configs/external
this is the help link...
Source Region—Source region for client devices. When users connect, GlobalProtect recognizes the device region and only allows users to connect to gateways that are configured for that region. For gateway choices, source region is considered first, then gateway priority.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-19-2018 09:02 AM - edited 04-19-2018 09:02 AM
You can create an inbound VPN security policy that is only allowing from those geographical regions, the firewall has built-in regions that you can choose from or you can define your own
On my lab device I have it setup to do this. depending on your topology/config it may vary but should be easily accomplished and you can narrow it down to the layer 7 specific apps as well
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-19-2018 09:25 AM
also... in version 8.something you can offer gateways dependant on what country the user is connecting from...
network/portal/agent/configs/external
this is the help link...
Source Region—Source region for client devices. When users connect, GlobalProtect recognizes the device region and only allows users to connect to gateways that are configured for that region. For gateway choices, source region is considered first, then gateway priority.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-19-2018 01:52 PM
Thank you MickBall. I have 8.1.0 version and this is the vpn setting i was lookin for.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2018 11:06 PM
I tried this as shown below, but did not work as expected. Global protect can still connect from other countries. I have only one portal and one gateway.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2018 11:25 PM
What happens if you remove the “Any” from region settings...
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-25-2018 12:49 AM
same effect without "Any". i already tried this.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-25-2018 12:56 AM
OK worth a try.. I must admit I have never used it but I just noticed the option when was looking into gateway priority.
If it's causing an issue perhaps it should be logged as a fault with support.
going by the documentation, it should work.
can you confirm that your PA is deffo recognising the regions you are connecting from.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-25-2018 02:21 AM
In the log, source country is showing corrctly.
Also "show location ip x.x.x.x" is showing correct country
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-13-2019 06:56 AM
@TechnologySvcs , did you get this working?
I require this capability in a new GP deployment and would like to avoid putting another device upstream to restrict the portal and gateway access by region.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2019 08:29 AM
fyi, in my case it did not work at that time. I haven't tried again.
But i believe it is possible to restrict Global protect access to your public ip address using security policy rules.
Try creating two rules as mentioned below.
RULE1
--------
source zone : outside
source address : IN (for eg. India, add required countries)
destination zone : outside
destination address : x.x.x.x (your public ip)
applications : panos-global-protect, panos-web-interface, ssl,
service : application-default
action: allow
RULE2
--------
source zone : outside
source address : any
destination zone : outside
destination address : x.x.x.x (your public ip)
applications : panos-global-protect, panos-web-interface, ssl,
service : application-default
action: deny
- 1 accepted solution
- 33471 Views
- 12 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- error: azure marketplace vm-series do not bootstrap in VM-Series in the Public Cloud
- How to restrict GP Portal authentication to specified countries in GlobalProtect Discussions
- Reports not working multi-vsys PAN-OS 11.0.2 in General Topics
- Clarification on Application and Service in security policy in Next-Generation Firewall Discussions
- Block Platform by Country of Ownership in Custom Signatures