- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Rules check by logs with expedition
- LIVEcommunity
- Discussions
- General Topics
- Rules check by logs with expedition
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Rules check by logs with expedition
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-01-2020 12:30 AM
Hello,
For one of our client , using PA 850 in cluster,
They have 8 zones for voip , printer , camera etc
And all the security policies are wide open.
Now we want to restrict the policy by looking at logs from each zone towars other.
Can we export logs from panorama to expedition to see or analyse it ?
Or what is best approach to do reverse engineering and implement the specific rules between zones.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-01-2020 03:47 AM - edited 10-01-2020 03:51 AM
Hi,
you can go with this filter so see respective logs.
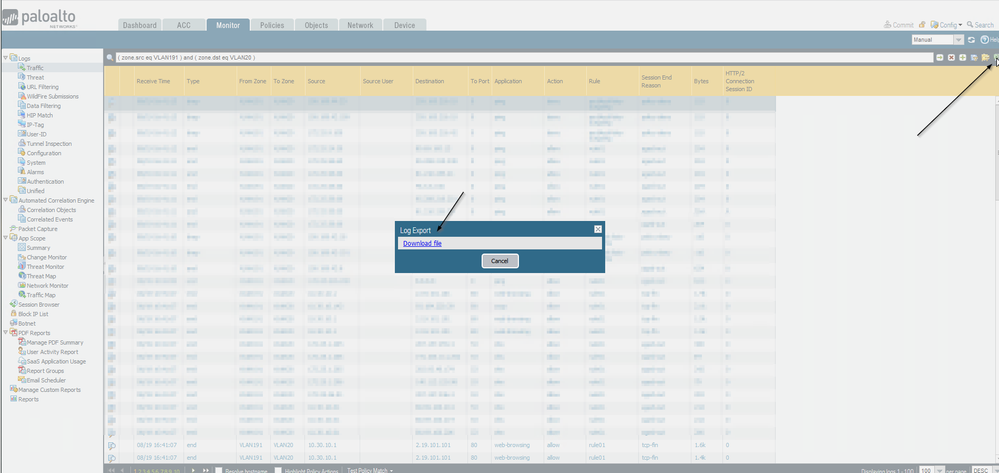
Monitor > Logs > Traffic > ( zone.src eq SRC_ZONE) and ( zone.dst eq DST_ZONE )
You can export the output shown into an CSV file.
Based on this output normally a good approach, in my opinion, is:
- setup an application group with apps you want to allow (good apps)
- setup an application group with apps you do not want to allow (bad apps),
- set up a policy with "application" = application group good apps, set it do allow, enable logging at session end
- set up a policy with "application" = application group bad apps, set it to deny or drop (whatever suits your setup), enable logging at session end
- set up a policy with "application" = any, set it to allow, enable logging at session end
Continually monitor this rules and fine tune your policy. In Policies > Name column > hover over policy name > triangle icon > log viewer. Later on it might become more difficult because with a single "allow rule" you will be forced to decide for a service (any/select/app default). In case of you need different ports other than "app-default" you need to add a specific policy.
Hope that helps.
René
// If you like my answer force commit it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-01-2020 10:24 AM
Good luck. Let us know if anything is missing.
René
// If you like my answer force commit it.
- 3072 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PAN-OS-PHP Combining actionss in General Topics
- How does the Azure Virtual Network discovers that there is Palo Alto Gateway Interface in VM-Series in the Public Cloud
- Issue with call recording (flow_predict_convert_rtp_drop) in Next-Generation Firewall Discussions
- AIOPs in AIOps for NGFW Discussions
- Security Posture Settings are now moved to Incident Settings in Strata Cloud Manager