- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
S2S VPN Phase1 down
- LIVEcommunity
- Discussions
- General Topics
- S2S VPN Phase1 down
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
S2S VPN Phase1 down
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2021 10:26 PM - edited 08-24-2021 12:12 AM
We have deployed PA-VM in Azure. We are setting up S2S VPN with Cisco Router. PA-VM is the initiator.
All the P1 and P2 param are matching but Status for both are showing red.
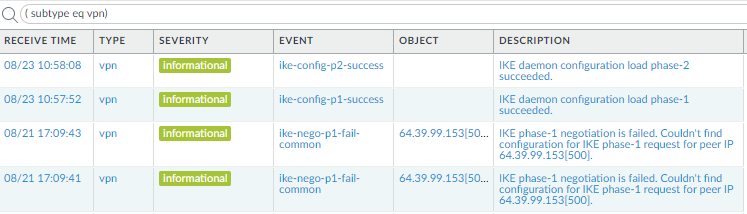
System logs show:
'IKE phase-1 negotiation is failed. Couldn\'t find configuration for IKE phase-1 request for peer IP 64.39.99.153[500].'
I do NOT have any 64.x.x.x IP configuration in PA or in Azure. Neither this is Peer WAN IP.
Please advise where this IP might be coming from.
Any help is appreciated.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2021 10:41 PM
Hi @Connected123 ,
I would recommend you to check if Peer IP address is accurate and properly configured at your side and also make sure there is reachability between your end public (or peer) IP & the remote end peer IP address.
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2021 11:06 PM - edited 08-24-2021 12:10 AM
Hi @SutareMayur
Thank you for your response.
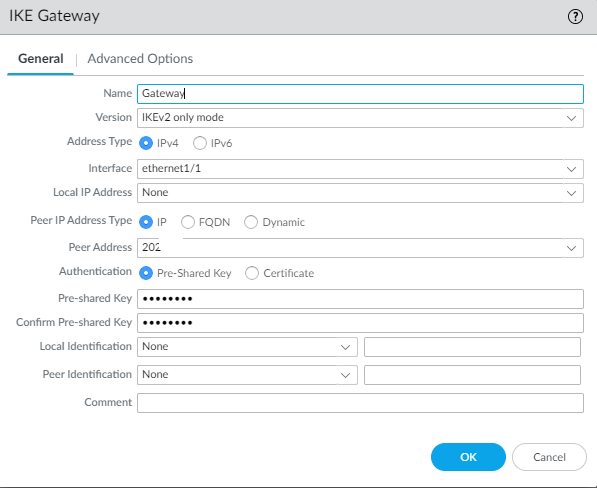
Peer WAN IP (202.x.x.x) address is correct. We have configured it in GW:
We have public IP of untrust interface (30.x.x.x) and Local Network (10.x.x.x) that peer end will reach to.
Kindly elaborate how to ensure the reachability from which IP to which IP and where to configure this.
Thanks in advance.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2021 11:49 PM - edited 08-22-2021 11:53 PM
Hi @Connected123 ,
Couple of points -
1. I see the configured peer IP address and the IP address shown in the logs are different. Kindly check if you are looking at the correct logs or there is some misconfiguration.
2. I would also recommend you to choose local IP address under drop down in IKE Gateway config. This IP would the one configured on selected interface. Also under local & peer identification, you can mention as IP addresses and add required entries.
3. Now answer to your query - Kindly elaborate how to ensure the reachability from which IP to which IP and where to configure this. - You can try to ping peer IP by keeping source as your end public IP using command ping source WAN_IP host destination_peer_ip
Now if destination IP is responding to icmp traffic then you should get response. Additionally you should have security policy configured to allow communication between peer IP addresses also. You can verify traffic to see if peer ip addresses traffic is getting allowed.
4. If still facing issues, kindly re-verify tunnel parameters configuration at both ends to check any mismatch. During troubleshooting, look at system logs to see any issues.
Click here for reference article - Configure IPSec VPN on Palo Alto
Hope it helps!
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2021 12:16 AM - edited 08-24-2021 04:41 PM
Hi @SutareMayur
Thank you so much for taking your time out and writing down all the points.
Please find my responses below.
1. You are right. The IPs are different and this is the issue. No idea where 64.x.x.x is coming from. This is the correct logs I am looking at as there is no other VPN configured in PA-VM.
2. The reason Local IP address of Eth1/1 was blank is because it is deployed in Azure and as per PA doc it says to select the Eth as DHCP (Step7.2 https://docs.paloaltonetworks.com/vm-series/10-1/vm-series-deployment/set-up-the-vm-series-firewall-...)
Anyway, I have changed it to Static as you mentioned and also filled out the Local ID and Peer ID.
3. Tried to ping as you have specified and the output is: bind: Cannot assign requested address
4. Policy is set to Allow All. Phase1 and Phase2 params are almost the same except for Encryption we are using AES-256-CBC and Peer Cisco is using AES-256. This was confirmed in one of the posts on this forum.
I am at a loss now and searched some similar posts (like below) where no resolution was provided.
Please help!
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2021 12:48 AM
Hi @Connected123 I guess you should focus on that wrong IP coming up under system logs. That must be the problem here. Can you try to initiate the traffic from your side again and check the traffic logs to verify the peer ip address ? Also verify the traffic logs for the seen peer IP in system logs and see if that request was came from peer side.
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2021 01:18 AM
Hi @SutareMayur
Thank you for the response.
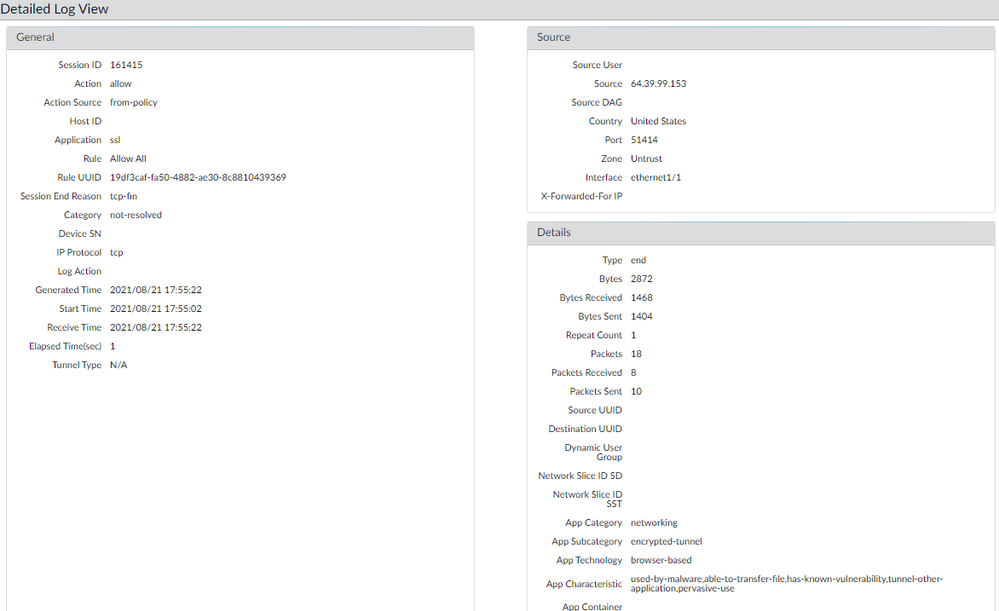
Traffic logs show logs from Untrust to Untrust but we have no clue abt the src IP 64.x.x.x. We cannot see the actual Peer IP address.
Detailed log is below.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2021 12:07 AM
Hi @SutareMayur
I made the VPN work and want to share the steps below in case someone else faces the same issue like me.
The error message on Peer IP was confusing and this may lead to wasting massive amount of time to solve the matter.
PA docs were extremely unhelpful and earlier posts in the forum did not help much in resolving the issue.
Also, I am not sure if my setup is accepted as I have seen few articles where TAC refused Loopback Interface for VPN setup.
So, below are the steps that helped.
1. 3 Zones: Untrust, Trust and VPN
2. 2 Interfaces: Ethernet 1/1 for Untrust and set the IP address as Static PRIVATE IP of WAN (even though in PA doc it says to select DHCP client otherwise VPN doesn't work!)
Ethernet1/2 for Trust and IPv4 as DHCP Client enabled (untick Automatically create.....)
3. 2 Tunnel Interfaces: Tunnel.1 and Tunnel.2 with Security Zone as VPN for both. Peer has two WAN circuits.
4. Customer requirement was to access their local machine traffic from our end needs to be NATTed as 172.x.x.x
So created loopback interface with IP 172.x.x.x and Security Zone as VPN.
5. For IKE GW, selected Untrust Interface Eth1/1 and Local IP address as the Static PRIVATE IP of WAN (even though PA doc says to leave it blank/none, otherwise VPN doesn't work!). I had to then select Local ID and Peer ID as Public IP address of WAN for both.
Left 'Enable NAT Traversal' as unticked. There are two GWs in my config.
6. For IPSec Tunnel, in Primary Tunnel, I selected tunnel.1 and Proxy ID as 172.x.x.x (NATTed IP) and 146.x.x.x (Peer Remote network).Technically, as per PA doc, it should have been 10.x.x.x (our local Network) and 146.x.x.x (Peer Remote network).
Did the same for Secondary Tunnel except I selected tunnel.2
7. For NATTing, I used SNAT by configuring Original Packet as below.
Src Zone: Trust
Dest Zone: VPN
Src Address: 10.x.x.x (our local Network)
Dest Address: 146.x.x.x (Peer Remote Network)
Translated Packet as DIPP with Interface Address as loopback Interface and IP address 172.x.x.x
8. Finally, I created two security policies. One with Src Zone: Trust, VPN and Dest Zone: Untrust.
Another one with Src Zone: Trust, VPN and Dest Zone: Trust, VPN
This now leads me to the next part of my problem. I need to create Tunnel Monitoring for the Primary and Secondary tunnel with Failover profile. No idea what to put as Destination IP as I am using loopback Interface.
Any idea?
- 6657 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Failed to initiate Plugin Phase1 commit in Panorama Discussions
- Service Connection and Cisco ASA - problem with establish VPN and BGP in Prisma Access Discussions
- Prisma Service Connection to Azure in Prisma Access Discussions
- IPSEC Tunnel Secondary is always down in Prisma Access Discussions
- Remote VPN gateway - IKE intitiator drop on Palo FW in General Topics