- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Solution for "SSL decryption bypass for Anydesk"
- LIVEcommunity
- Discussions
- General Topics
- Solution for "SSL decryption bypass for Anydesk"
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Solution for "SSL decryption bypass for Anydesk"
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-11-2021 05:43 AM - edited 03-22-2021 01:45 AM
Hello,
I am being asked a lot about why is Anydesk getting a "decrypt-error" end reason when SSL Decryption is active.
Here is a simple explanation and how to overcome this.
What you usually going to do with this kind of errors is creating a Decryption bypass rule for Anydesk (in this example)
Since is it impossible to bypass based on application, you would probably use a Custom URL category with a wildcard (*.anydesk.com), and apply it in a bypass rule. Unfortunately, this doesn't work (I'm not sure why, I think Anydesk uses IP addresses and not URLs)
The other option I came across is using an FQND (relays.net.anydesk.com) published in one of the related articles, that also didn't work for me. It was not consistent.
Then I found that Anydesk is being bypassed by default in PANOS (Device --> Certificate management --> SSL Decryption Exclusion).
Then why isn't it being bypassed?!
Well, it is because of the certificate Anydesk uses. It is using a Self-Signed certificate, and your device does not trust it (yet).
This is the reason for the decrypt-error.
Basically, what you would like to do now is:
Start a packet capture and export the CA certificate.
Then, import the certificate to your device, and mark it as a trusted CA.
Commit, and now Anydesk should work.
I am sharing here the CA certificate currently being used by Anydesk.
Copy the text below to a text file and rename it to ".crt"
-----BEGIN CERTIFICATE-----
MIIFYzCCA0ugAwIBAgIJAIf7DQy3sYvoMA0GCSqGSIb3DQEBBQUAMEgxFzAVBgNV
BAMMDkFueU5ldCBSb290IENBMSAwHgYDVQQKDBdwaGlsYW5kcm8gU29mdHdhcmUg
R21iSDELMAkGA1UEBhMCREUwHhcNMTQwNDExMDIzNzU1WhcNMjQwNDA4MDIzNzU1
WjBIMRcwFQYDVQQDDA5BbnlOZXQgUm9vdCBDQTEgMB4GA1UECgwXcGhpbGFuZHJv
IFNvZnR3YXJlIEdtYkgxCzAJBgNVBAYTAkRFMIICIjANBgkqhkiG9w0BAQEFAAOC
Ag8AMIICCgKCAgEAtBVBDdoa01og/vnfvwqM8aSt79RUlufigrcNAOrxN+LXjKEW
O6BoCDiqbdsmvqZpkzaojh5w3KyBHuLdFoM0tRVw9YrNne5dgHxaeKIHpK7m+NYx
+lx7u+Ba61Evl7/2+zMnkLPY5ODNaDtqh2ymDefYvWHfVmsq4Rwr9Z+/hd2MWwYe
cX+6SqZAsHcX6iw/W5QUhS6tEWGriPYBu7NHa+KBGPGOOebYewxjhoOscIR1Jy01
PXt7qM6ySHkIOC2CJn6TSzJ2ZoWn/crxCi/HYg9qQP4aa1gcU+RjwXWDmqt4BEmD
H+cjcJ+jv2jRMy9M3l6GmH1hfQE09Zzpy0FrrlArZ9XZ8gL8X6NSNLncZ+/6c8WU
QOq1iveY7Oibu4ZsbzY3ioCMn4T2ykp2InKNUn2FdU1V762v8+UWIwBb6Lbtfp8u
gEvu1V/cZemJ3NumQwS7zv2pTC8ZM6rmcSCG/kWLl+bIHU9wusfAw/Om8trCpBvd
iU7sHNp7JI+qQvkUMoNoY8gmvOwTsw0L4rYIxsYGfqMWbxXSGxZSPB8ikSUXFcxC
gto7qDnHKlDK2UygjJUzdQNwuN+gybKyixs4g3kywxLaM5ZC9JERqsYmMbzqQ4ow
VGXFQ55QO/qRkw6dOyNKPUPBxiKbaK8v/AGAUhgFIg69auQuydbsxY/zE7MCAwEA
AaNQME4wHQYDVR0OBBYEFBlleQaAxt6yqliZV7I2XO0BYo1HMB8GA1UdIwQYMBaA
FBlleQaAxt6yqliZV7I2XO0BYo1HMAwGA1UdEwQFMAMBAf8wDQYJKoZIhvcNAQEF
BQADggIBALOqRxekr9JgNBWtJdWOKF7BqrGNMFabR3by4CBUBj3xI8Lvu6Hyn+Or
DAa/VF4MGjVWbeGTS8WZX5CGflKDlKCgRzby/PLCTXDJyW40XKcPBP3rFl6KvoY7
oAxzf6P1Xz0rxUEMZwrjSCvKYvapmh7J5ES8F/nbXEWYCWnsyGPvhSlOce35maxJ
IIqQvFmO8fOlmZkS46d75Wg0q1NarfFEyrp/wqZzkhDqjLHGydXkXisPHkqT+W1M
BoWQZVHTicwuomu15PDqNzWpfcDLhxIycpMhUYEdowzKlviB9JKgr/cZJPPmzeoR
KcnxKR2yKxgatKPAWMRwOXiniNd0MsKAYoNY47Q+JbhWLGB3UiWqYTLRl413JDQk
xdvy3WHI7WNXDsJw5R9S3WxvOLLa7Z2nL4f6s3DlZE35wwLVRtofy/BYIPxElvDK
tps55s8n0CyZdNTK3keI7d/3nDusimLSdZDZAIHT+MJHjpq9h23O5Zp/KHakd8Y/
ub9N8cvfDyxz/rRg4yZeg/KuNlaU6aedoT3KXW49Xahv8qWP855ohSfs6WeFNBYN
RTQUjgcMeyVRVPM/oSrvmheeUd4WZPvd4ciUCYw5u3dz1Ga7SStc+itXi2at96hw
O4+eCXHeEi7tAhBM1Wcecv86PjRtkmA9RF70IWDubC46cxrDJmr0
-----END CERTIFICATE-----
Hope this is helpful.
Cheers!
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-21-2021 03:23 PM
And idea is If you want you can remove Anydesk from the "SSL Decryption Exclusion" and test decrypting it and presenting the users with the trusted certificate as a workaround (they will not see the self signed cert in this way) just check also if the SSL decryption profile allows self signed certficates.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PPJfCAO
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-22-2021 01:51 AM
Due to client Certificate authentication, you cannot decrypt Anydesk.
This is Why is it added by PANW to "SSL Decryption exclusion" list.
The need to import the certificate into the NGFW is to make PANOS trust the self-signed certificate used by Anydesk server.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-22-2021 09:47 AM
In this cas you are right that Palo Alto can't decrypt it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2021 12:43 AM
It need even this anydesk relay certificate. After seen works.
-----BEGIN CERTIFICATE-----
MIIFYzCCA0ugAwIBAgIJAIf7DQy3sYvoMA0GCSqGSIb3DQEBBQUAMEgxFzAVBgNV
BAMMDkFueU5ldCBSb290IENBMSAwHgYDVQQKDBdwaGlsYW5kcm8gU29mdHdhcmUg
R21iSDELMAkGA1UEBhMCREUwHhcNMTQwNDExMDIzNzU1WhcNMjQwNDA4MDIzNzU1
WjBIMRcwFQYDVQQDDA5BbnlOZXQgUm9vdCBDQTEgMB4GA1UECgwXcGhpbGFuZHJv
IFNvZnR3YXJlIEdtYkgxCzAJBgNVBAYTAkRFMIICIjANBgkqhkiG9w0BAQEFAAOC
Ag8AMIICCgKCAgEAtBVBDdoa01og/vnfvwqM8aSt79RUlufigrcNAOrxN+LXjKEW
O6BoCDiqbdsmvqZpkzaojh5w3KyBHuLdFoM0tRVw9YrNne5dgHxaeKIHpK7m+NYx
+lx7u+Ba61Evl7/2+zMnkLPY5ODNaDtqh2ymDefYvWHfVmsq4Rwr9Z+/hd2MWwYe
cX+6SqZAsHcX6iw/W5QUhS6tEWGriPYBu7NHa+KBGPGOOebYewxjhoOscIR1Jy01
PXt7qM6ySHkIOC2CJn6TSzJ2ZoWn/crxCi/HYg9qQP4aa1gcU+RjwXWDmqt4BEmD
H+cjcJ+jv2jRMy9M3l6GmH1hfQE09Zzpy0FrrlArZ9XZ8gL8X6NSNLncZ+/6c8WU
QOq1iveY7Oibu4ZsbzY3ioCMn4T2ykp2InKNUn2FdU1V762v8+UWIwBb6Lbtfp8u
gEvu1V/cZemJ3NumQwS7zv2pTC8ZM6rmcSCG/kWLl+bIHU9wusfAw/Om8trCpBvd
iU7sHNp7JI+qQvkUMoNoY8gmvOwTsw0L4rYIxsYGfqMWbxXSGxZSPB8ikSUXFcxC
gto7qDnHKlDK2UygjJUzdQNwuN+gybKyixs4g3kywxLaM5ZC9JERqsYmMbzqQ4ow
VGXFQ55QO/qRkw6dOyNKPUPBxiKbaK8v/AGAUhgFIg69auQuydbsxY/zE7MCAwEA
AaNQME4wHQYDVR0OBBYEFBlleQaAxt6yqliZV7I2XO0BYo1HMB8GA1UdIwQYMBaA
FBlleQaAxt6yqliZV7I2XO0BYo1HMAwGA1UdEwQFMAMBAf8wDQYJKoZIhvcNAQEF
BQADggIBALOqRxekr9JgNBWtJdWOKF7BqrGNMFabR3by4CBUBj3xI8Lvu6Hyn+Or
DAa/VF4MGjVWbeGTS8WZX5CGflKDlKCgRzby/PLCTXDJyW40XKcPBP3rFl6KvoY7
oAxzf6P1Xz0rxUEMZwrjSCvKYvapmh7J5ES8F/nbXEWYCWnsyGPvhSlOce35maxJ
IIqQvFmO8fOlmZkS46d75Wg0q1NarfFEyrp/wqZzkhDqjLHGydXkXisPHkqT+W1M
BoWQZVHTicwuomu15PDqNzWpfcDLhxIycpMhUYEdowzKlviB9JKgr/cZJPPmzeoR
KcnxKR2yKxgatKPAWMRwOXiniNd0MsKAYoNY47Q+JbhWLGB3UiWqYTLRl413JDQk
xdvy3WHI7WNXDsJw5R9S3WxvOLLa7Z2nL4f6s3DlZE35wwLVRtofy/BYIPxElvDK
tps55s8n0CyZdNTK3keI7d/3nDusimLSdZDZAIHT+MJHjpq9h23O5Zp/KHakd8Y/
ub9N8cvfDyxz/rRg4yZeg/KuNlaU6aedoT3KXW49Xahv8qWP855ohSfs6WeFNBYN
RTQUjgcMeyVRVPM/oSrvmheeUd4WZPvd4ciUCYw5u3dz1Ga7SStc+itXi2at96hw
O4+eCXHeEi7tAhBM1Wcecv86PjRtkmA9RF70IWDubC46cxrDJmr0
-----END CERTIFICATE-----
Claudio Verniani - PAE
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2024 12:58 PM
Does anyone have the updated CA certificate? This one expires April 7th this year.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-25-2024 08:33 AM
I am in the same boat. I cannot find a replacement anywhere.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-05-2024 03:51 AM
Same for me - anybody has the new certificate?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-05-2024 04:19 AM
Have you fixed it somehow?
We got same problem, can't get new CA certificate from sslabs.
Managed to get *.relay.net.anydesk.com certificate, but it's not working without AnyNet Root CA 2
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2024 12:15 PM - edited 04-08-2024 12:16 PM
Hello,
In the past it was working the workaround from this discussion: https://live.paloaltonetworks.com/t5/general-topics/anydesk-issue/m-p/516607#M107283
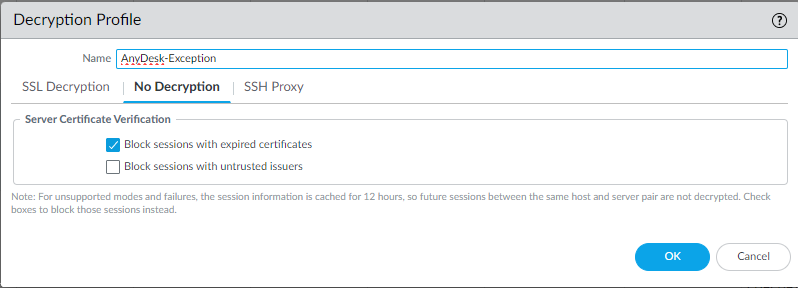
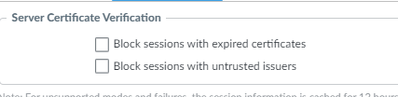
Now, when I can't have the AnyNet Root CA 2, I modified my Decryption Profile and unchecked "Block session with untrusted issuers" and I'm based only on URL's
Maybe this information will help you.
Cosmin
Don't forget to Like items if a post is helpful to you!
Please help out other users and “Accept as Solution” if a post helps solve your problem!
Read more about how and why to accept solutions.
Disclaimer: All messages are my personal ones and do not represent my company's view in any way.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2024 10:53 PM
In my case both options unchecked, but still not working, can yo share your Decryption policy for AnyDesk?
I'm using URL category *.net.anydesk.com and action no-decrypt.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2024 05:34 AM
this has stopped working once the anynet rootCA cert expired on the 7th of april , we urgently need the updated ROOT CA cert.
please someone post it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2024 05:45 AM
Welcome to the club . ( By the way anydesk started using the new certificate on 4/April/24 )
We have 2 open tickets with anydeks and 1 with PaloAlto and still nobody is helping in any way.
If someone manage to find the new certificate from the captures please share.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2024 09:53 AM
Hello @ArtursOstapenko
Please see my comments from this post: https://live.paloaltonetworks.com/t5/general-topics/anydesk-issue/td-p/198761 (on second page - it's step 3 Custom URL list)
Cosmin
Don't forget to Like items if a post is helpful to you!
Please help out other users and “Accept as Solution” if a post helps solve your problem!
Read more about how and why to accept solutions.
Disclaimer: All messages are my personal ones and do not represent my company's view in any way.
- 43551 Views
- 32 replies
- 7 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- I have a question CVE-2026-0256 PAN-OS in VM-Series in the Public Cloud
- Multi-VSYS 11.2.8 - How to assign a dedicated Forward Trust Certificate per VSYS for SSL Decryption in Next-Generation Firewall Discussions
- Failed to generate CSR Device Certificate - PA-520 - in General Topics
- Foward Trust Cert and MacBook Pro in General Topics
- Is It Possible to Distribute Client Certificates to iOS Devices Using GlobalProtect SCEP Without MDM? in General Topics