- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Timeout value of user-ID log
- LIVEcommunity
- Discussions
- General Topics
- Timeout value of user-ID log
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Timeout value of user-ID log
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2018 09:37 PM - edited 01-31-2018 09:38 PM
We are using ldap authentication and globalprotect.
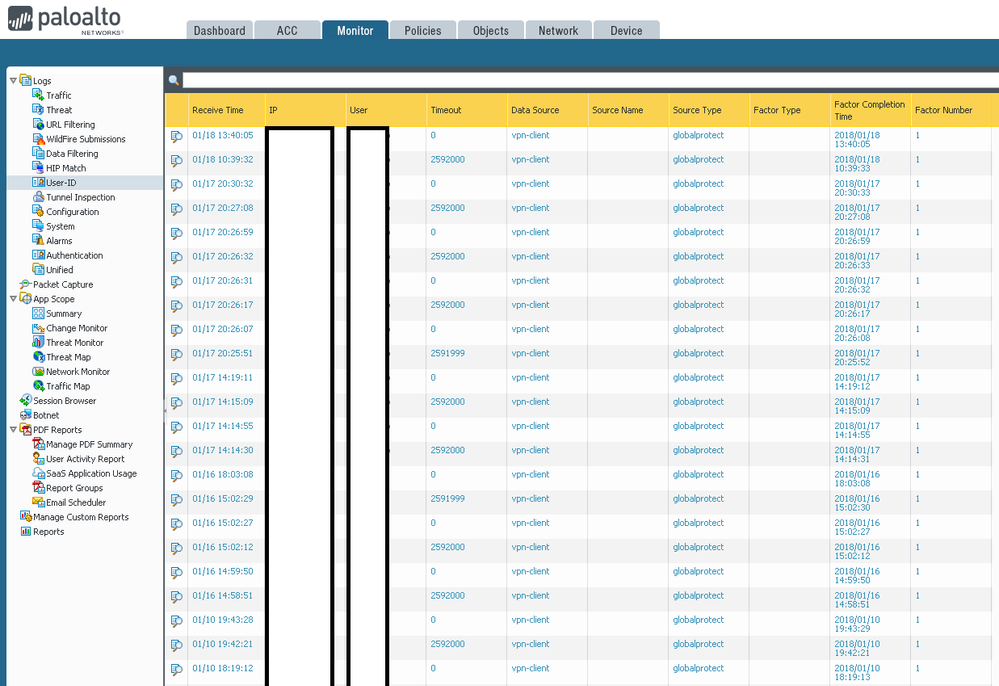
In the above picture, the timeout value continues to be 2592000 and 0
time out 2952000 and 0 , what does that mean?
Why does it look like above?
Please let me know.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-25-2018 07:54 AM - edited 03-25-2018 07:59 AM
Hello jskang,
The Timeout value is officially defined as "Timeout after which the IP/User Mappings are cleared." in this document: https://www.paloaltonetworks.com/documentation/80/pan-os/pan-os/monitoring/use-syslog-for-monitoring...
With that in mind, what should be happening is that your users authenticate to GP or any other source (AD, captive-portal, etc.) and authenticate at that time and this user-id log entry shows a Timeout value.
However, due to the logs attempting to show everything related to user-id, you'll also see any refresh times or secondary authentication attempts, etc. but these will NOT have their own Timeout value, only refresh the original Timeout for the actual mapping.
In the case of active-directory mappings, you'll also see the original mapping and then a few times where the Source Name shows up as "probing", and this also has a Timeout of 0, but that's because it also is refreshing the original mapping and doesn't have a timeout of its own
Basically what you're seeing is the user-id log mapping every bit of information it gets because that's its job, not because that was a genuine mapping at that time. It likely was assisting the original mapping, but how could you troubleshoot the refreshes/probings if you don't see them on the user-id log?
- 4880 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Intelligence Stream 504 Error, PCC v.33 in Prisma Cloud Discussions
- PAN-275077 is this bug still affected in 11.1.10-h1? in Next-Generation Firewall Discussions
- Firwall is uable to send logs to the Panorma (Log collector is showing inactive) in Next-Generation Firewall Discussions
- Rollout Strategy: GlobalProtect Disconnect Comments + 12-Hour Auto-Reconnect in GlobalProtect Discussions
- GlobalProtect Name Normalization issue in GlobalProtect Discussions