- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
UDP log that hit any deny rule and show allow
- LIVEcommunity
- Discussions
- General Topics
- UDP log that hit any deny rule and show allow
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
UDP log that hit any deny rule and show allow
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-15-2018 07:17 PM - edited 06-15-2018 07:21 PM
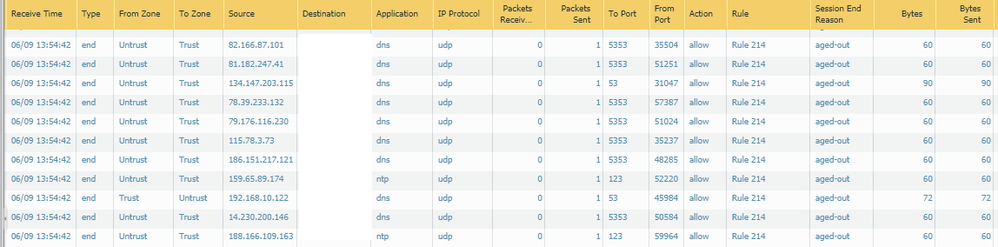
Hello, i have a question about UDP session
rule 34
untrust any
trust any
app icmp, traceroute, ping
service any
action allow
rule 214
any any deny
you can see allow log hit rule 214
i found similar case about tcp.
i think UDP session was created hitting rule 34 but don't understand UDP log showing allow and hit rule 214
Could you explain this log?
Best regards.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2018 09:51 PM
It might help if you expand one of the sessions so that we can actually see what happened. Just the log doesn't really tell anyone much, but it likely has to do with the fact that you are allowing icmp, traceroute, and ping on service any with an action of allow. My guess would be that if you look at the actual session you'll see something a little different than what the base log is showing in your traffic logs. -
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-17-2018 10:01 AM
It could be exactly the same behaviour as described in the article you mentionned as the applications in your screenshot are also analysed with a decoder. When you enable the start log or even better with a flow basic analysis you probably find out more about this.
But besides this behaviour with allow logs for a deny rule. From your screenshot it looks like your trust zone has private IP addresses (RFC1918), so may I ask you why you have a rule allowing ping, icmp and traceroute from the internet towards your internal network?
And: do you still have these "allowed"-deny-logs when you set the service in rule 34 to application-default?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-17-2018 11:01 AM - edited 06-17-2018 11:02 AM
Hello, @Remo
why you have a rule allowing ping, icmp and traceroute from the internet towards your internal network?
- it replaced old checkpoint firewall
And: do you still have these "allowed"-deny-logs when you set the service in rule 34 to application-default?
- There is no allowed log in rule 214 after set the service in rule 34 to application-default
when allowed log created i was doing HA A-P Failover test.
There was always System log that HA state change from passive to active between Start time and Receive time in allowed log
In other words, i think allowed log session was started on peer.
Best regards.
- 1691 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Amber LED on PA3220 in Next-Generation Firewall Discussions
- Detect and Restrict Powershell cmdlets in Cortex XDR Discussions
- Automation rule to add IP address to EDL in Cortex XDR Discussions
- QoS bandwidth limit in General Topics
- High Disk Space Usage on / root partition of Panorama in Panorama Discussions