- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
VLAN Confusion
- LIVEcommunity
- Discussions
- General Topics
- VLAN Confusion
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-31-2023 10:04 PM
Hi,
I’ve recently got a PA-440, and trying to make sense of the VLAN logic on PAN-OS has got me stumped.
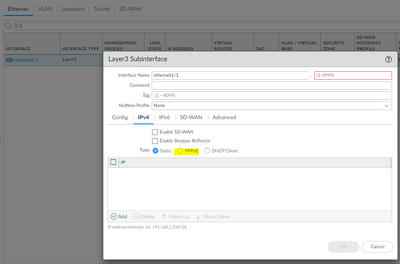
First of all, I get creating a layer 3 sub interface and assigning a VLAN tag, easy. A bit odd that the 'tag' doesn't then show up as a VLAN under Network > VLANs, but I can let that slide.
It's an access port where things really don't make sense. I follow the steps below, and even though it works it just doesn't make sense.
- Mark an interface as layer 2, and assign a layer 2 zone to it, ok.
- Create a VLAN (Network > VLANs) - sure, but you don’t specify a VLAN ID, just a name. What is the point of this construct?
- Assign created VLAN (from step 2) to the physical layer 2 interface - again, ok, but given the VLAN hasn’t got an ID, does this achieve anything?
- Create a VLAN Interface (with an ID between 1-9999) and assign a VLAN to it. I assume this is like an SVI, but I don’t need a layer 3 VLAN interface, why is this necessary? Also, it seems like the ID is meant to be the VLAN tag (but the range is not right, 1-9999 rather than 1-4094)?
I'm hoping someone can explain this to be, as the documentation isn't clear.
- What is the point of VLANs under Network > VLANs? Given you don't specify a VLAN ID.
- Is the ID under the VLAN interface actually a VLAN tag, rather than an interface ID? If so, why is the range 1-9999 (rather than 1-4094)?
Thanks for any help.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-01-2023 02:28 PM
Hi there,
Palo Alto have taken the approach of decoupling the VLAN ID from the VLAN virtual-bridge construct. When you create a VLAN object under Network -> VLAN, the name is the UID not a VLAN ID as would be the case on a cisco. The object you create here is a virtual-bridge which is used to bind the various Layer 2 interfaces defined Network -> Interfaces -> Ethernet and a single SVI under Network -> Interfaces -> VLAN.
The ID number which is required by a sub-interface or VLAN/SVI interface is arbitrary. The tag number which is selected under the sub-interface is the VLAN ID and is used for the 802.1Q encapsulation. The sub-interface ID and tag number do not have to match, but it can help with readability!
It is worth noting that this decoupling of VLAN ID from the VLAN object means that sub-interfaces which use different 802.1Q tags can use the same VLAN virtual-bridge effectively performing VLAN tag rewriting.
cheers,
Seb.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-01-2023 02:28 PM
Hi there,
Palo Alto have taken the approach of decoupling the VLAN ID from the VLAN virtual-bridge construct. When you create a VLAN object under Network -> VLAN, the name is the UID not a VLAN ID as would be the case on a cisco. The object you create here is a virtual-bridge which is used to bind the various Layer 2 interfaces defined Network -> Interfaces -> Ethernet and a single SVI under Network -> Interfaces -> VLAN.
The ID number which is required by a sub-interface or VLAN/SVI interface is arbitrary. The tag number which is selected under the sub-interface is the VLAN ID and is used for the 802.1Q encapsulation. The sub-interface ID and tag number do not have to match, but it can help with readability!
It is worth noting that this decoupling of VLAN ID from the VLAN object means that sub-interfaces which use different 802.1Q tags can use the same VLAN virtual-bridge effectively performing VLAN tag rewriting.
cheers,
Seb.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-02-2023 03:35 AM
Thanks, Seb.
This would suggest that an access port cannot exist (for example) in VLAN 20 unless a sub-interface has been created with tag '20' and both of these objects have been associated with a VLAN object (Network > VLAN)? Suppose this doesn't really matter, as an access port VLAN ID isn't relevant unless a trunk port exists somewhere on the said device (which it won't unless sub-interfaces have been created).
Finally, I take it a VLAN sub-interface (Network > Interfaces > VLAN) isn't needed unless inter-VLAN routing is required?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-02-2023 09:07 AM - edited 04-02-2023 09:11 AM
It is always easier to set interfaces in Layer3.
Main interface will be untagged and subinterfaces will tag packets.
Layer2 makes sense only if you deploy firewall in small office with few devices and you don't have dedicated switch (all devices connect directly to Palo) and you need multiple interfaces to be in same subnet/vlan.
Other reason to use Layer2 is if you have existing setup. Let's say web server and database servers were historically deployed in single vlan. You want to separate them and place firewall in between. What you can do is connect web server and database server directly to Palo. Set Palo interfaces in Layer2 and create firewall policy in between to permit only specific traffic. As a result no re-IP needed but security posture improved.
In all other cases Layer3 with subinterfaces is way to go.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-03-2023 01:31 AM
Hi there,
Once you configure a Layer2 sub-interface you are creating a trunk link and 802.1q will be enabled, using the 'tag' value as the VLAN ID on the encapsulated frame.
An access port if you think about doesn't really need a VLAN tag, as it is never imposed on the frame, they arrive and leave untagged. The VLAN tag/ ID is there purely to identify which virtual-bridge the frames belong to.
The object created under Network -> Interfaces -> VLAN is not a subinterface. I see you confusion as it prepends a digit to the interface name. The interface here is a SVI/ IRB . If you have configured your firewall interfaces all as Layer2, then yes you will need these for inter-VLAN routing. You can have a mix of routed Layer 3 interfaces (dedicated or subinterface) and VLAN interfaces for inter-VLAN routing, depending on your topology.
cheers,
Seb.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-03-2023 02:30 PM - last edited on 11-04-2024 05:32 PM by JayGolf
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-03-2023 05:21 PM
Once you get to v11 one day you can configure PPPoE on subinterface.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-03-2023 06:08 PM
Ah, nice, I've been waiting for this. How stable is v11? 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-04-2023 05:40 AM
I have few test installs and they run smooth and stable. They don't have too complex config though.
Have not found any new bugs.
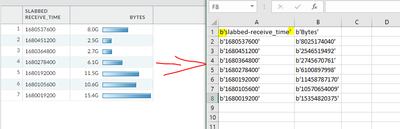
Old ones that have been issues also in 10.2 are still present. Mostly reporting related like CSV export still puts annoying b' ' characters around values in 11.0.1
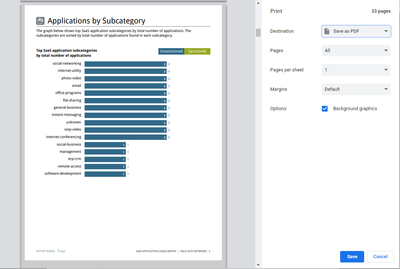
SaaS report print as PDF still puts gray frame around edges in 11.0.1
If config is pushed from Panorama then you can't use firewall built in UserID agent with 11.0.1. Got fix in 10.2.4 but v11 will get its fix with 11.0.2
Management plane cpu went up a bit with 10.2 > 11.0.0. Have not checked 11.0.1 yet.
Palo Alto Networks certified from 2011
- 1 accepted solution
- 14175 Views
- 8 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- traffic disruption on routing change in Next-Generation Firewall Discussions
- How to add Wildcard Domains as a destination for Firewall policy PA1420 in General Topics
- How to make Router BGP ping into IP inside Palo Alto in Next-Generation Firewall Discussions
- Panorama HA Pair and Managed Log Collectors Upgrade Process - Clarification in General Topics
- GUEST WIFI for new client in Next-Generation Firewall Discussions